Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Tristan Morris October 5, 2023 Guest Blogger: Aubrey King | Community Evangelist...
Source: securityboulevard.com - Author: Jeffrey Burt Developers and tech vendors need to improve multifactor authentication (MFA)...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: newscred Welcome back to our journey through Kaseya DattoCon 2023, which took...
Source: securityboulevard.com - Author: Coby Montoya Transitioning from legacy fraud solutions like Kount may be easier...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Joel Wong With today’s unpredictable and evolving cybersecurity landscape, Swimlane understands that...
Source: securityboulevard.com - Author: Chris Garland When it comes to IT and cybersecurity, few industries can...
Source: securityboulevard.com - Author: CISO Global October 5, 2023 Author: Baan Alsinawi, CISSP, CCSP, CISM, CGEIT,...
Source: securityboulevard.com - Author: Pandian Gnanaprakasam Ordr welcomes Wes Wright as our new Chief Healthcare Officer...
Source: securityboulevard.com - Author: Rick Wednesday, October 4, 2023 Security Boulevard The Home of the Security...
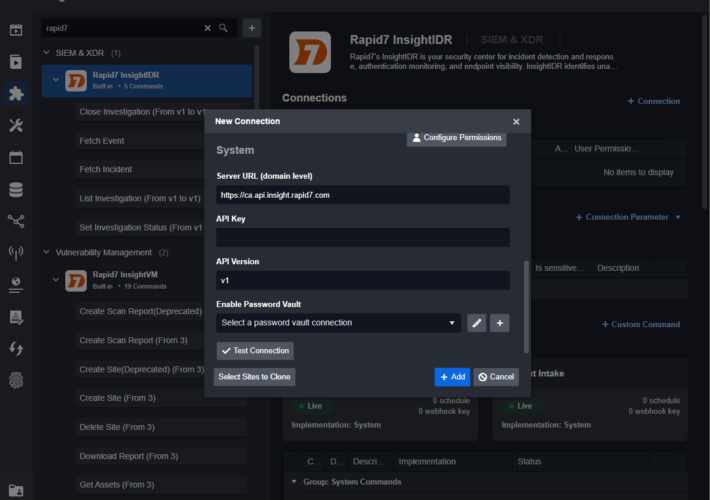
Source: securityboulevard.com - Author: Pierre Noujeim Integration between platforms has become a necessity rather than a...
Source: securityboulevard.com - Author: Deb Radcliff Interview with Vince Arneja, Chief Product Officer of CodeSecure (formerly...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Hurricane Labs Financial institutions are entrusted with a vast treasure trove of...
Source: securityboulevard.com - Author: Hurricane Labs In today’s rapidly evolving digital landscape, the financial services industry...
Source: securityboulevard.com - Author: Hurricane Labs In an era of persistent cyber threats, financial institutions must...
Source: securityboulevard.com - Author: Mark Knowles When it comes to successfully securing your organization today, the...
Source: securityboulevard.com - Author: Jeffrey Burt The popular NPM code registry continues to be a target...
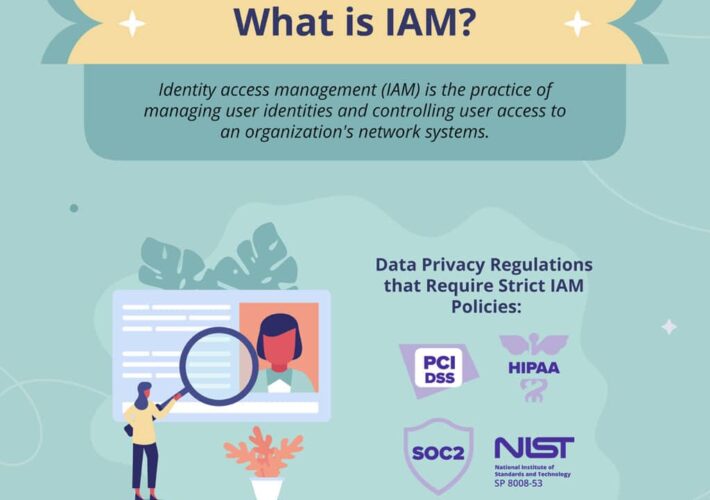
Source: securityboulevard.com - Author: Grip Security Blog In today’s digital age, data breaches and cyberattacks have...
Source: securityboulevard.com - Author: Sectigo CAs are trusted organizations that store, sign and issue SSL certificates...
Source: securityboulevard.com - Author: Ashley Stevensonn It’s no secret that growing revenue through digital channels is...
Source: securityboulevard.com - Author: Scott Wright More importantly, the hackers claim to have stolen 6 terabytes...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
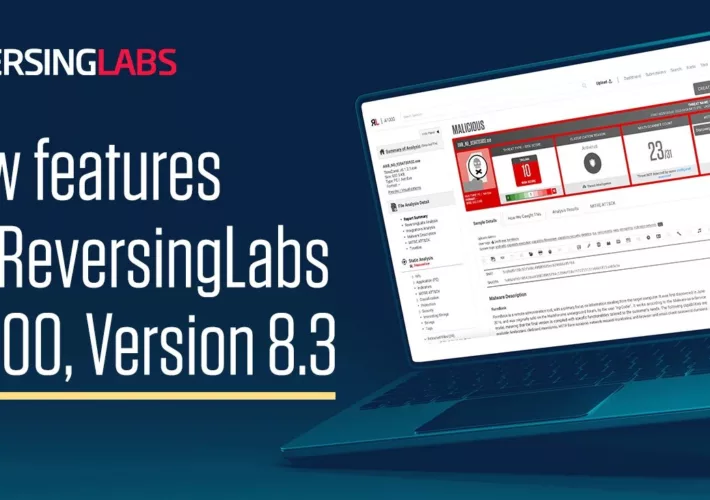
Source: securityboulevard.com - Author: ReversingLabs Our customers rely on ReversingLabs A1000 Threat Analysis and Hunting Solution...
Source: securityboulevard.com - Author: Jeffrey Burt Engineers with Amazon Web Services more than a decade ago...
Source: securityboulevard.com - Author: Jenn Jeffers The duality of the botmaster underscores the versatility of botnets,...
Source: securityboulevard.com - Author: Kelly Dougherty Welcome to the “Life in the Swimlane” blog series. Here...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...