Source: securityboulevard.com - Author: claude.mandy This article was originally published on Spiceworks. The holiday season is...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Marc Handelman Many thanks to USENIX for publishing their outstanding USENIX Security...
Source: securityboulevard.com - Author: Cavelo Blog For organizations looking to improve their data protection and data...
Source: securityboulevard.com - Author: Cavelo Blog The public nature of the legal system makes law firms...
Source: securityboulevard.com - Author: Marc Handelman No one specifically Someone on our general security team A...
Source: securityboulevard.com - Author: claude.mandy This article was originally published on Spiceworks. The holiday season is...
Source: securityboulevard.com - Author: Sift Trust and Safety Team Have you ever felt the frustration of...
Source: securityboulevard.com - Author: Alexandra Charikova Welcome to the Elephant in AppSec, the podcast to explore,...
Source: securityboulevard.com - Author: Marc Handelman No one specifically Someone on our general security team A...
Source: securityboulevard.com - Author: Jeffrey Burt Dozens of banks around the word are in the crosshairs...
Source: securityboulevard.com - Author: Pierre Noujeim In 2023, we’ve achieved a remarkable milestone in the cybersecurity...
Source: securityboulevard.com - Author: Ayan Halder Over the last six days alone, Arkose Labs identified and...
Source: securityboulevard.com - Author: Marc Handelman Thursday, December 21, 2023 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
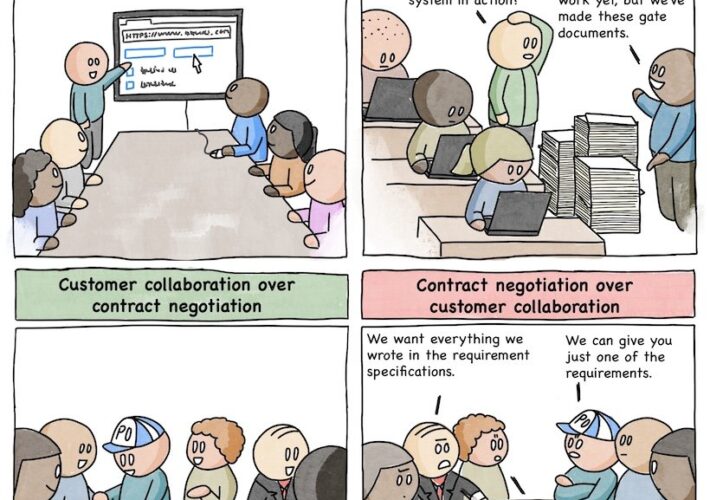
Source: securityboulevard.com - Author: Aaron Linskens Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Marc Handelman Thursday, December 21, 2023 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: Joe Breen Hot Topics Advancing SOAR Technology: Key 2023 Updates in Incident...
Source: securityboulevard.com - Author: Jeffrey Burt International authorities took two big swipes at cybercriminals this week,...
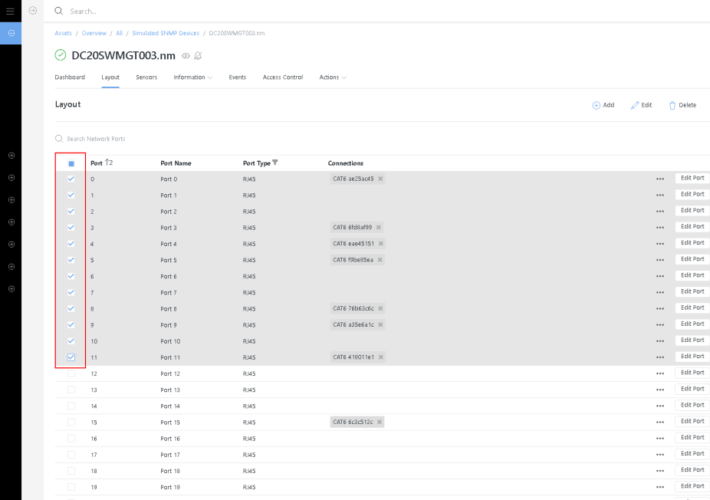
Source: securityboulevard.com - Author: Rajan Sodhi Product Update: Version 4.2 We’re wrapping up the year with...
Source: securityboulevard.com - Author: Katie Bykowski RV Connex is a Thailand-based company that specializes in national...
Source: securityboulevard.com - Author: Jeffrey Burt Threat actors are finding new ways to take advantage of...
Source: securityboulevard.com - Author: Alison Napolitano CodeSonar static application security testing (SAST) tool now provides integrated...
Source: securityboulevard.com - Author: Marc Handelman Wednesday, December 20, 2023 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: Paul Asadoorian Introduction Firmware security analysis is a critical aspect of modern...
Source: securityboulevard.com - Author: Michael Vizard AppOmni this week unveiled a technology preview of a digital...
Source: securityboulevard.com - Author: Marc Handelman Wednesday, December 20, 2023 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: Ronen Slavin In today’s hyper-connected world, secure software development is no longer...
Source: securityboulevard.com - Author: George McGregor This overview outlines the history and use of Google Play...
Source: securityboulevard.com - Author: Richi Jennings Lurking vuln in SSH spec means every implementation must build...
Source: securityboulevard.com - Author: Corey Sinclair As we prepare to ring in the new year, the...