Source: securityboulevard.com - Author: hrbrmstr The 2024 U.S. Presidential election isn’t just another tick on the...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Joe Breen Cloud Security, Governance and Skills in 2024 Step 1 of...
Source: securityboulevard.com - Author: Jai Vijayan Container technologies are rapidly transforming application development and deployment practices...
Source: securityboulevard.com - Author: Marc Handelman No one specifically Someone on our general security team A...
Source: securityboulevard.com - Author: Webzoly SEO Fraud is everywhere, and it’s affecting you whether you realize...
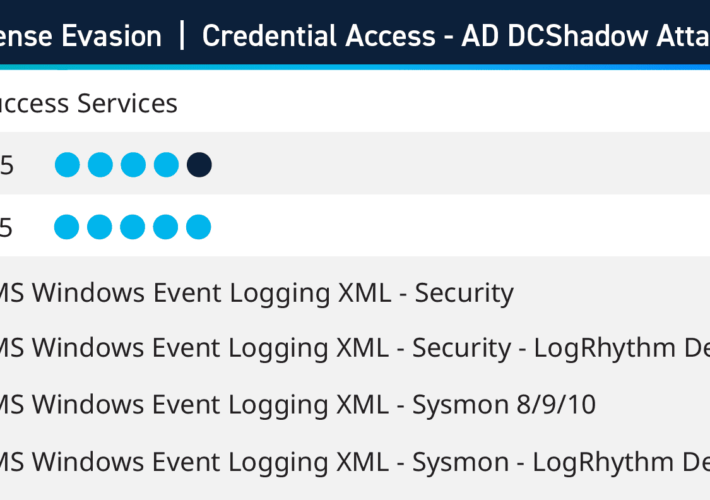
Source: securityboulevard.com - Author: Kelsey Gast As part of Success Services, this past quarter LogRhythm consultants...
Source: securityboulevard.com - Author: Webzoly SEO It’s unfortunately become an all-to-common scenario: you’re waiting for a...
Source: securityboulevard.com - Author: Michael Vizard Abnormal Security has published examples of cyberattacks that illustrate how...
Source: securityboulevard.com - Author: Jaweed Metz In the realm of cybersecurity, the metaphor of “Leaky Buckets”...
Source: securityboulevard.com - Author: Marc Handelman No one specifically Someone on our general security team A...
Source: securityboulevard.com - Author: Tova Osofsky In July 2023 the US Security and Exchange Commission (SEC)...
Source: securityboulevard.com - Author: Marc Handelman No one specifically Someone on our general security team A...
Source: securityboulevard.com - Author: Jeffrey Burt Palo Alto Network’s cybersecurity recently outlined two vulnerabilities it found...
Source: securityboulevard.com - Author: Michael Vizard As the New Year dawns, a cybersecurity report from Google...
Source: securityboulevard.com - Author: bacohido By Yuga Nugraha In today’s digital landscape, organizations face numerous challenges...
Source: securityboulevard.com - Author: Marc Handelman No one specifically Someone on our general security team A...
Source: securityboulevard.com - Author: Team Nuspire Security posture is a term often mentioned in cybersecurity, with...
Source: securityboulevard.com - Author: Dana Epp Never trust user input. It’s been the mantra for years...
Source: securityboulevard.com - Author: Richi Jennings Infostealer scrotes having a field day with unpatched vulnerability.A zero-day...
Source: securityboulevard.com - Author: Deepen Desai Amidst the ever-evolving realm of enterprise security, a new year...
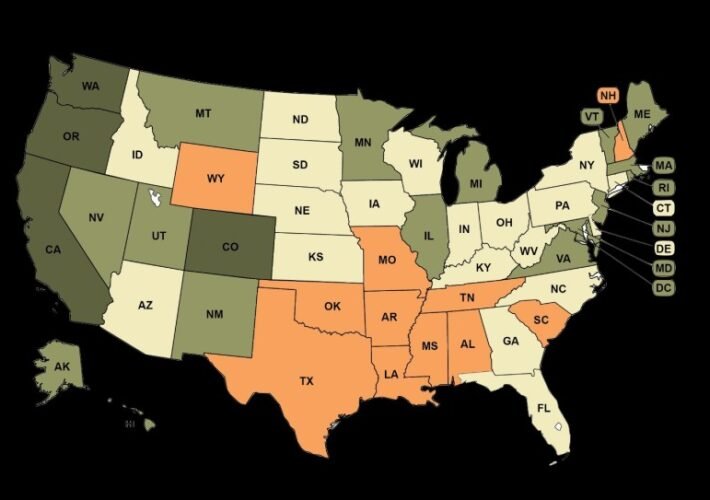
Source: securityboulevard.com - Author: hrbrmstr Hey folks, This is likely our last shot at preserving liberal...
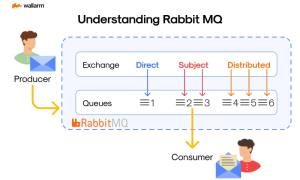
Source: securityboulevard.com - Author: Ivan Novikov Grasping the Basics: What is RabbitMQ? Take a step into...
Source: securityboulevard.com - Author: Michelle Ofir Geveye The narrative of technology surpassing human intelligence and altering...
Source: securityboulevard.com - Author: Rohan Timalsina In an ever-evolving digital landscape, the healthcare and public health...
Source: securityboulevard.com - Author: TuxCare Team When you find out your website is hacked, it’s understandable...
Source: securityboulevard.com - Author: Marc Handelman No one specifically Someone on our general security team A...
Source: securityboulevard.com - Author: Wajahat Raja Threat actors with malicious intent have now been exploiting an...
Source: securityboulevard.com - Author: Tom Eston In this episode, host Tom Eston shares the three key...
Source: securityboulevard.com - Author: Marc Handelman No one specifically Someone on our general security team A...
Source: securityboulevard.com - Author: Emma Kelly As we say goodbye to 2023, let’s look back on...