Source: securityboulevard.com - Author: Marc Handelman No one specifically Someone on our general security team A...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
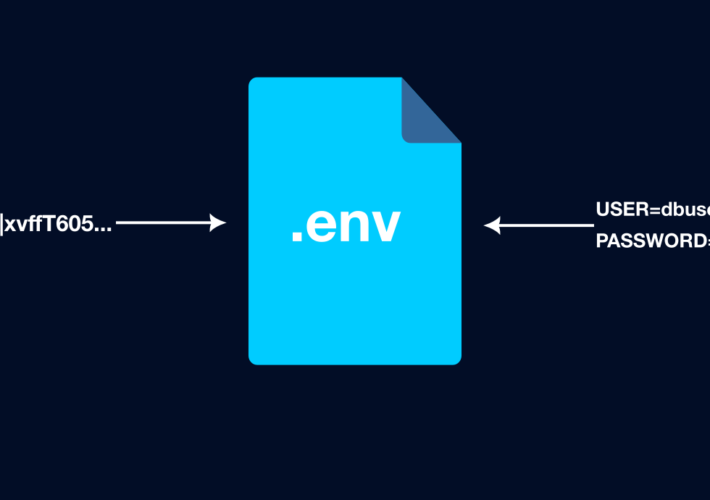
Source: securityboulevard.com - Author: Greg Bulmash Using environment variables to store secrets instead of writing them...
Source: securityboulevard.com - Author: Jeffrey Burt The accelerating development and expanding deployment of AI systems is...
Source: securityboulevard.com - Author: Flare The Network Information Systems Directive (NIS) was published in 2016 and...
Source: securityboulevard.com - Author: Marc Handelman No one specifically Someone on our general security team A...
Source: securityboulevard.com - Author: Marc Handelman No one specifically Someone on our general security team A...
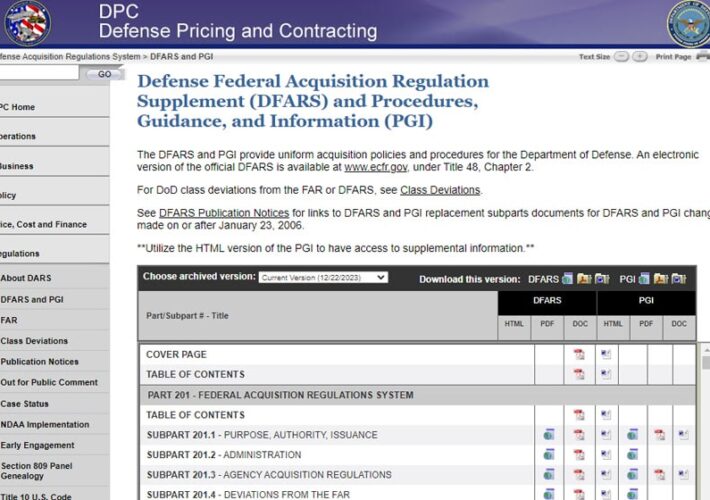
Source: securityboulevard.com - Author: Max Aulakh The Defense Federal Acquisition Regulation Supplement, better known as DFARS,...
Source: securityboulevard.com - Author: hrbrmstr Three years ago, on January 6, 2021, the U.S. Capitol was...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: Garrett Smith, Tarun Yadav, Jonathan Dutson, Scott Ruoti, Kent...
Source: securityboulevard.com - Author: CyB3rBEA$T In the ever-evolving landscape of operating systems, Linux stands out as...
Source: securityboulevard.com - Author: Hyperproof Team Incident response is a critical piece of any enterprise cybersecurity...
Source: securityboulevard.com - Author: Kartik Subramanian, Engineering Welcome back to our series on automating phishing investigation...
Source: securityboulevard.com - Author: Marc Handelman No one specifically Someone on our general security team A...
Source: securityboulevard.com - Author: Pondurance With more than 3 billion phishing emails received each day, employees...
Source: securityboulevard.com - Author: Marc Handelman No one specifically Someone on our general security team A...
Source: securityboulevard.com - Author: Michael Vizard Mimecast this week announced it has acquired Elevate Security as...
Source: securityboulevard.com - Author: Jeffrey Burt The co-founder and CEO of a startup cryptocurrency wallet said...
Source: securityboulevard.com - Author: Marc Handelman No one specifically Someone on our general security team A...
Source: securityboulevard.com - Author: Aaron Linskens No one specifically Someone on our general security team A...
Source: securityboulevard.com - Author: stackArmor Utilize the Self-Reminder model. When using RAG, provide a similarity_score_threshold. When...
Source: securityboulevard.com - Author: Michael Vizard A survey of 214 senior executives involved in cybersecurity decisions...
Source: securityboulevard.com - Author: Michael Vizard SentinelOne this week announced it is acquiring PingSafe to add...
Source: securityboulevard.com - Author: Marc Handelman No one specifically Someone on our general security team A...
Source: securityboulevard.com - Author: Patrick Bedwell Netography Fusion Expands Microsoft Integrations for Greater Context Enrichment and...
Source: securityboulevard.com - Author: Cavelo Blog At its core, Attack Surface Management (ASM) is the process...
Source: securityboulevard.com - Author: Marc Handelman No one specifically Someone on our general security team A...
Source: securityboulevard.com - Author: Harris Maidenbaum Article Discover how combining your investigative research into a configurable,...
Source: securityboulevard.com - Author: Team Nuspire Cyber threat actors continue to focus much of their sights...
Source: securityboulevard.com - Author: Jeffrey Burt Password manager vendor LastPass, beset by high-profile data breaches from...
Source: securityboulevard.com - Author: Marc Handelman Cloud Security, Governance and Skills in 2024 Step 1 of...