Source: securityboulevard.com - Author: Michael Vizard A report published by Netskope today revealed that, on average,...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Joe Breen If you see something, say something and get paid by...
Source: securityboulevard.com - Author: Kevin Smith If you are a managed service provider (MSP) handling small...
Source: securityboulevard.com - Author: EasyDmarc In response to evolving email authentication standards set by tech giants...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Michael Toback I understand that security is a top priority for you....
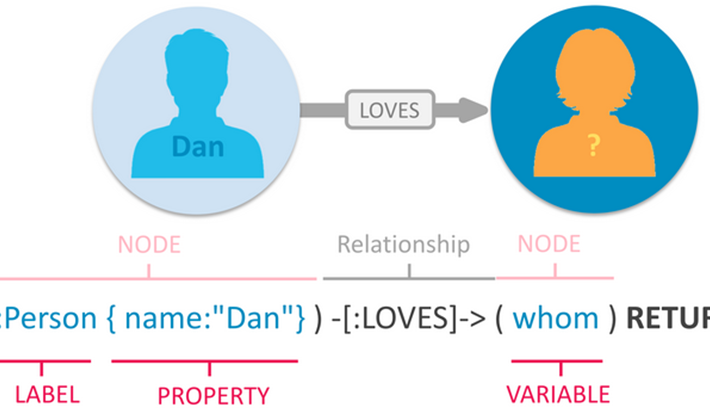
Source: securityboulevard.com - Author: Dana Epp API security isn’t a dark art. But no soothsayer out...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: Renjie Xie, Jiahao Cao, Enhuan Dong, Mingwei Xu, Kun...
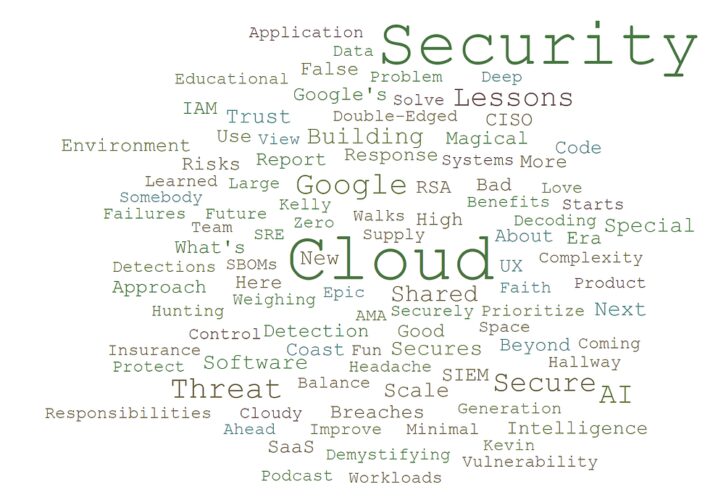
Source: securityboulevard.com - Author: Anton Chuvakin So, we (Tim and Anton, the crew behind the podcast)...
Source: securityboulevard.com - Author: Michael Vizard Kasada has updated its bot defense platform to add hundreds...
Source: securityboulevard.com - Author: Jenn Jeffers Looking ahead to the digital terrain of 2024, it is...
Source: securityboulevard.com - Author: Marc Handelman Wednesday, January 10, 2024 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: Richi Jennings Chinese citizens using peer-to-peer wireless comms “must be identified.”The Beijing...
Source: securityboulevard.com - Author: Katie Fritchen This article was originally published in Hackernoon on 12.13.23 by...
Source: securityboulevard.com - Author: Nathan D. BloodHound Enterprise (BHE) recently saw the addition of a new,...
Source: securityboulevard.com - Author: Impart Security Blog We’re excited to announce our newest Integrated Password Strength...
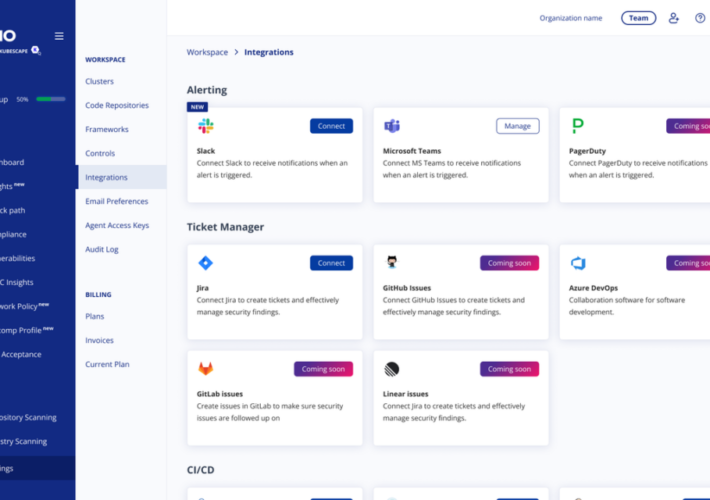
Source: securityboulevard.com - Author: Yossi Ben Naim We’re thrilled to introduce a fresh ARMO app designed...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: Jian Qu, Xiaobo Ma, Jianfeng Li, Xiapu Luo, Lei...
Source: securityboulevard.com - Author: Jeffrey Burt The issues of outside interference in U.S. elections and the...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
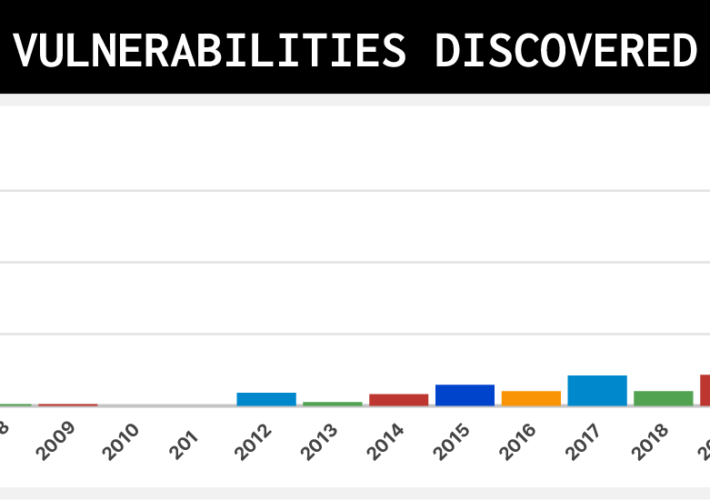
Infographic: A History of Network Device Threats and What Lies Ahead – Source: securityboulevard.com
Source: securityboulevard.com - Author: Chris Garland In 2023, the industry experienced a significant uptick in attacks...
Source: securityboulevard.com - Author: Kelsey Gast Entering a new year, the cybersecurity landscape is poised for...
Source: securityboulevard.com - Author: John P. Mello Jr. Zoom, best known for its online videoconferencing and...
Source: securityboulevard.com - Author: Team Nuspire The exploitation of an undocumented Google OAuth endpoint, MultiLogin, by...
Source: securityboulevard.com - Author: Erin Crapser Boston MA—January 9, 2024—TrustCloud, the Trust Assurance platform using AI...
Life in the Swimlane with Principal Data Scientist, Dima Skorokhodov – Source: securityboulevard.com
Source: securityboulevard.com - Author: Kelly Dougherty Welcome to the “Life in the Swimlane” blog series. Here...
Source: securityboulevard.com - Author: Deepak Gupta - Tech Entrepreneur, Cybersecurity Author In today’s digital age, passwords...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: Michele Campobasso, Luca Allodi Many thanks to USENIX for...
Source: securityboulevard.com - Author: Erin Crapser The position of CISO is not an enviable one. Modern...
Source: securityboulevard.com - Author: CyB3rBEA$T Navigating through directories is a fundamental aspect of working in a...