Source: securityboulevard.com - Author: Nick Rago The cost of not knowing what good is. Could you...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Marc Handelman Network Security Security Bloggers Network Home » Cybersecurity » Network Security...
Source: securityboulevard.com - Author: Adam Cheriki, Co-founder & CTO, Entro As per the State of Developer...
Source: securityboulevard.com - Author: Julie Peterson We live in a world filled with constant notifications. From...
PixieFail Bugs in UEFI Open Source Implementation Threaten Computers – Source: securityboulevard.com
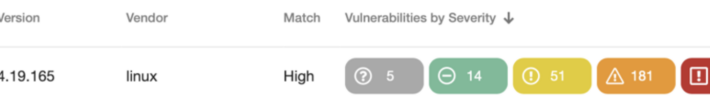
Source: securityboulevard.com - Author: Jeffrey Burt A collection of security vulnerabilities found within the de facto...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
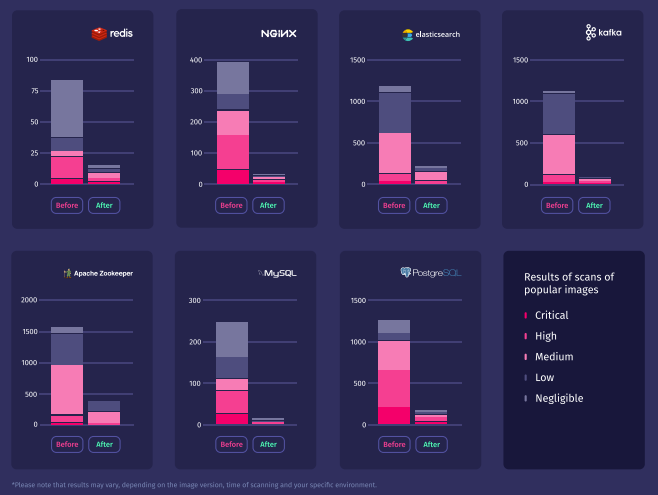
Source: securityboulevard.com - Author: Ben Hirschberg With the rapid pace of technological evolution, ensuring security within...
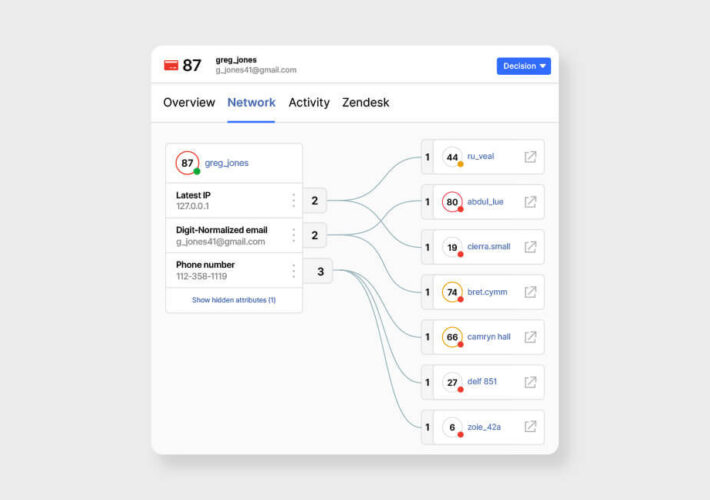
Source: securityboulevard.com - Author: Sift Product Team The world of iGaming is fiercely competitive, and attracting...
Source: securityboulevard.com - Author: Lance B. Cain Authored By: Lance B. Cain and Alexander DeMine Overview...
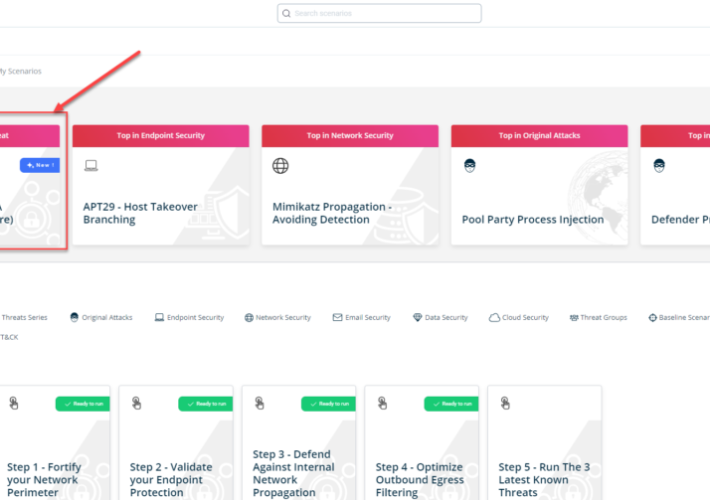
Source: securityboulevard.com - Author: Kaustubh Jagtap Author: Kaustubh Jagtap, Product Marketing Director, SafeBreach On January 16th,...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: Floris Gorter, Enrico Barberis, Raphael Isemann, Erik van der...
Source: securityboulevard.com - Author: Team Nuspire A significant security concern has been raised for organizations using...
Source: securityboulevard.com - Author: Vikas Shetty Thanks to various 2023 security reports, we know phishing attacks...
Source: securityboulevard.com - Author: Marc Handelman Wednesday, January 17, 2024 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: bacohido Los Angeles, Calif., Jan. 17, 2024 – Spam calls continue to...
Source: securityboulevard.com - Author: Michael Vizard A report published today by Netcraft, a provider of cybersecurity...
Source: securityboulevard.com - Author: Kevin Smith Taking a hands-off approach to cybersecurity is no longer good...
Source: securityboulevard.com - Author: Chuck Randolph Article By: Chuck Randolph | January 16, 2024 This article...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Richi Jennings Sam says avoid AI abuse—protect the democratic process.With elections coming...
Source: securityboulevard.com - Author: Dana Epp Introduction Sometimes, the way to bypass API auth is easier...
Source: securityboulevard.com - Author: Mark Hermeling There is lot of talk about Software Bill of Materials...
Source: securityboulevard.com - Author: Avoid The Hack! Welcome to the world of online/digital privacy! Like its...
Source: securityboulevard.com - Author: Marc Handelman Hot Topics Netcraft Report Surfaces Spike in Online Healthcare Product...
Source: securityboulevard.com - Author: Carolynn van Arsdale Software supply chain attacks are now mainstream events —...
Source: securityboulevard.com - Author: Nik Hewitt Identity Threat Detection and Response (ITDR) remains crucial for preventing...
Source: securityboulevard.com - Author: Alexandre Tang Want to know how to secure your Express.js APIs? Dive...
Source: securityboulevard.com - Author: Jeffrey Burt Environmental services websites are becoming significant targets for threat groups...
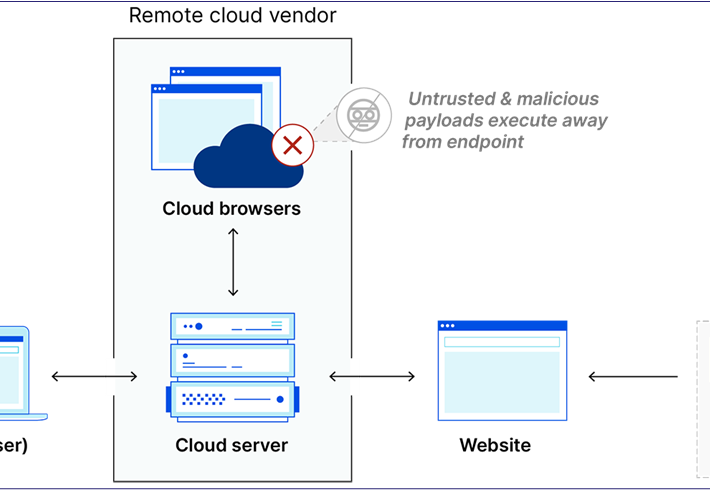
Source: securityboulevard.com - Author: Gilad David Maayan Cloud operations, often referred to as CloudOps, is the...
Source: securityboulevard.com - Author: Rohan Timalsina In the dynamic realm of cybersecurity, staying ahead of potential...