Source: securityboulevard.com - Author: Alexandra Charikova Welcome to the Elephant in AppSec, the podcast to explore,...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
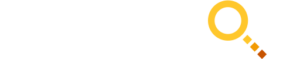
Source: securityboulevard.com - Author: Marc Handelman via the comic artistry and dry wit of Randall Munroe,...
Source: securityboulevard.com - Author: Tony Bradley Salt Security has announced a pivotal partnership with CrowdStrike. This...
Source: securityboulevard.com - Author: John Gallagher Until recently I thought we had a lot of time...
Source: securityboulevard.com - Author: John P. Mello Jr. Organizations are struggling with software supply chain security....
Source: securityboulevard.com - Author: FireMon FireMon is purpose-built for compliance reporting with 12 built-in reports, over...
Source: securityboulevard.com - Author: claude.mandy It’s time to embrace the season of love and connection. Valentine’s...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: Priyanka Nanayakkara, Mary Anne Smart, Rachel Cummings, Gabriel Kaptchuk,...
Source: securityboulevard.com - Author: Orlee Berlove, reviewed by Gregg Laroche Small and Medium Certified Public Accountants...
Source: securityboulevard.com - Author: Orlee Berlove, reviewed by Gregg Laroche Educational Institutions and third parties providing...
Source: securityboulevard.com - Author: Marc Handelman via the comic artistry and dry wit of Randall Munroe,...
Source: securityboulevard.com - Author: Richi Jennings Does your home security need a rethink? Wireless cameras are...
Source: securityboulevard.com - Author: Flare Initial access brokers (IABs) gain unauthorized access to the system then...
Source: securityboulevard.com - Author: Katie Fritchen This Indiana School District Partners With ManagedMethods To Help Keep...
Source: securityboulevard.com - Author: Jeffrey Burt South Korean researchers exploited an implementation vulnerability in the ransomware...
Source: securityboulevard.com - Author: Team Nuspire Several cybersecurity advisories and agencies recommend not caving into ransomware...
Source: securityboulevard.com - Author: Deb Radcliff By Deb Radcliff, industry analyst and editor of CodeSecure’s TalkSecure...
Source: securityboulevard.com - Author: Alison Underdown As cyber threats grow alongside penalties for negligence, risk and...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: Thomas Tan Intro The Kubernetes documentation describes operators as “software extensions to...
Source: securityboulevard.com - Author: bacohido San Mateo, Calif., Feb. 13, 2023 – The U.S. White House...
Source: securityboulevard.com - Author: Richi Jennings While Rome burns, Federal Communications Commission is once again behind the curve.The...
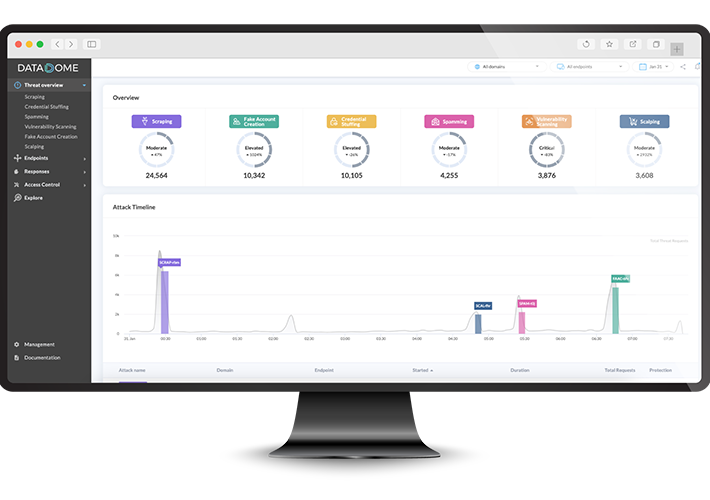
Source: securityboulevard.com - Author: DataDome If you sell anything online or store any sensitive information digitally,...
Source: securityboulevard.com - Author: Marc Handelman Wednesday, February 14, 2024 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: Jenn Markey The new year is always a time for reflection, and...
Source: securityboulevard.com - Author: NSFOCUS In 2023, countries worldwide continued to strengthen their cybersecurity capabilities and...
Source: securityboulevard.com - Author: Digital Defense by Fortra What is Fortra IdP? Fortra Identity Provider (IdP)...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: Nissy Sombatruang, Tristan Caulfield, Ingolf Becker, Akira Fujita, Takahiro...
Source: securityboulevard.com - Author: Digital Defense by Fortra How the justice system deals with cybercrime is...
Source: securityboulevard.com - Author: Rick It was only a matter of time before someone did this....