Source: securityboulevard.com - Author: Dancho Danchev I recently came across to another image courtesy of Conti...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: davehull In my second job out of college, my boss’ boss would...
Source: securityboulevard.com - Author: Pierre Noujeim We are excited to announce the launch of D3’s public...
Source: securityboulevard.com - Author: Brian Fox In the fast-changing fields of cybersecurity and software development, the...
Source: securityboulevard.com - Author: Jeffrey Burt Avast Software will pay a $16.5 million fine to settle...
Source: securityboulevard.com - Author: Marc Handelman Friday, February 23, 2024 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: Marc Handelman via the inimitable Daniel Stori at Turnoff.US. Permalink *** This...
Source: securityboulevard.com - Author: DataDome 1. Is the bot management solution delivered as a service (is...
Source: securityboulevard.com - Author: Riddika Grover Before understanding the need for endpoint security, let’s make you...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: claude.mandy This blog originally appeared here: https://aws.amazon.com/blogs/apn/cloud-native-data-security-posture-management-deployments-on-aws-with-symmetry-systems/ With Amazon Web Services (AWS), you...
Source: securityboulevard.com - Author: Digital Defense by Fortra Any business that accepts credit card payments is...
Source: securityboulevard.com - Author: Aaron Linskens Wednesday, February 21, 2024 Security Boulevard The Home of the...
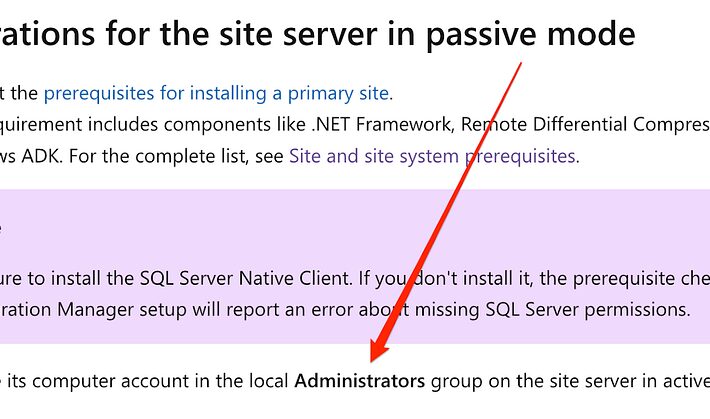
Source: securityboulevard.com - Author: Garrett Foster TL;DR: SCCM sites configured to support high availability can be...
Source: securityboulevard.com - Author: AJ Starita Containers offer many benefits, including lightweight portability from one environment...
Source: securityboulevard.com - Author: Marc Handelman Many thanks to USENIX for publishing their outstanding USENIX Security...
Source: securityboulevard.com - Author: Kevin Smith Keeping students’ data safe from prying eyes and malicious actors...
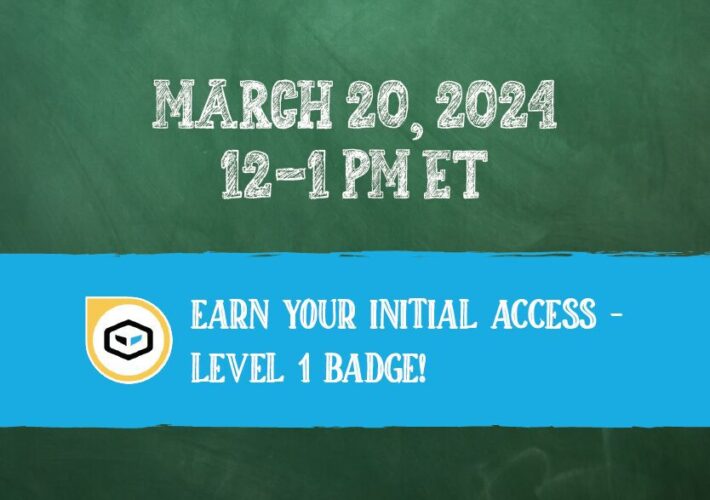
Source: securityboulevard.com - Author: Cyborg Security Get ready to elevate your threat hunting skills with Cyborg...
Source: securityboulevard.com - Author: Tal Zacks Find out the key capabilities of secret scanners and what...
Source: securityboulevard.com - Author: Wes Wright Identify and address at-risk assets to protect your healthcare enterprise...
Source: securityboulevard.com - Author: Lauren Blanc, Marketing Manager, Scytale Picture this: June 2020, the year our...
Source: securityboulevard.com - Author: Matt Palmer How Boards can clear the path for effective cyber risk...
Source: securityboulevard.com - Author: Kasada Executive Summary True Alliance, a retailer and distributor of premium brands,...
Source: securityboulevard.com - Author: richard-r.stewart@thalesgroup.com How to protect your machinelearning Models richard-r.stew… Tue, 02/20/2024 – 21:50...
Source: securityboulevard.com - Author: Michael Vizard Menlo Security today unfurled a software-as-a-service (SaaS) platform that makes...
Source: securityboulevard.com - Author: Avast Blog Last week, Charlotte Cowles—a seasoned journalist with a notable tenure...
Source: securityboulevard.com - Author: Jeffrey Burt The European Commission is once again turning its attention to...
Source: securityboulevard.com - Author: Hyperproof Team In enterprise risk management (ERM), the “R” in Governance, Risk,...
Source: securityboulevard.com - Author: Team Nuspire Zoom, the widely used video conferencing platform, has recently patched a series of...
Source: securityboulevard.com - Author: bacohido AI chatbots are computer programs that talk like humans, gaining popularity...