Source: securityboulevard.com - Author: Alison Mack Is Your NHI Management Ready to Face Evolving Security Needs?...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Alison Mack Are You Really Securing Your Non-Human Identities and Secrets? How...
Source: securityboulevard.com - Author: bacohido By Byron V. Acohido APIs have become the digital glue of...
Source: securityboulevard.com - Author: Devesh Patel If you’ve worked with SCIM for any length of time,...
Source: securityboulevard.com - Author: Tom Hollingsworth In cybersecurity, the old maxim “you can’t secure what you...
Source: securityboulevard.com - Author: Expert Insights on Synthetic Data from the Tonic.ai Blog Updated 1/29/24: Since the...
Source: securityboulevard.com - Author: Expert Insights on Synthetic Data from the Tonic.ai Blog This is the...
Source: securityboulevard.com - Author: Expert Insights on Synthetic Data from the Tonic.ai Blog This is the...
Source: securityboulevard.com - Author: Mend.io Team Best SAST Solutions: How to Choose Between the Top 11...
Source: securityboulevard.com - Author: Dev Kumar Imagine receiving a video call from your company’s CEO asking...
Source: securityboulevard.com - Author: FireMon Enterprise security teams are stretched thin, and the attack surface keeps...
Source: securityboulevard.com - Author: Alison Mack How Reliable are Your Non-Human Identity Security Measures? Have you...
Source: securityboulevard.com - Author: Alison Mack Are Your Cybersecurity Strategies Evolving Effectively? The question arises: Is...
Source: securityboulevard.com - Author: Alison Mack Why is Budget-Friendly NHI Management Crucial for Business Success? Effective...
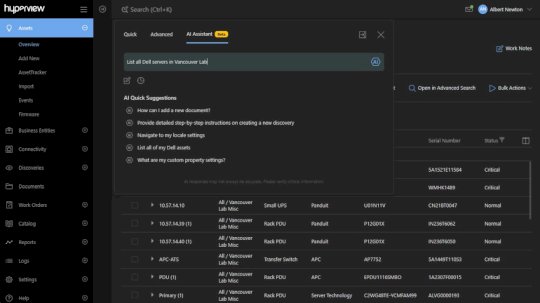
Source: securityboulevard.com - Author: Rajan Sodhi Product Update: Version 5.0 We’ve rolled out our biggest update...
Source: securityboulevard.com - Author: Marc Handelman Author/Presenter: Carl George (Principal Software Engineer, Red Hat) Our sincere...
Source: securityboulevard.com - Author: Alexa Sander In school environments, blocking apps is necessary. Not only to...
Source: securityboulevard.com - Author: Tony Thompson Who is Hero? AI Companionship that Force-Multiplies Cybersecurity AI is...
Source: securityboulevard.com - Author: Matt Palmer A few years ago I wrote a short article about...
Source: securityboulevard.com - Author: Brian Bensky The decision to adopt a purpose-built container operating system (OS)...
Source: securityboulevard.com - Author: Matthew Rosenquist A coalition of banking industry associations, including SIFA, the American...
Source: securityboulevard.com - Author: Marc Handelman Author/Presenter: Joe Ryan (High Performance Computing Systems Engineer, Institute for...
Source: securityboulevard.com - Author: Tom Hollingsworth In the evolving landscape of cyber threats, security teams often...
Source: securityboulevard.com - Author: Tom Hollingsworth In March 2024, Veeam, a leader in data protection, made...
Source: securityboulevard.com - Author: Namita Sharma Product-market fit is every startup’s holy grail, but getting there...
Source: securityboulevard.com - Author: Kasada NEW YORK & SYDNEY – June 25, 2025 — Kasada, the trusted provider of...
Source: securityboulevard.com - Author: Jason Kwon Organizations may have a need to write applications or scripts...
Source: securityboulevard.com - Author: Tyrone Dougherty From a packed house in NYC to screens across the...
Source: securityboulevard.com - Author: MixMode Threat Research MixMode Threat ResearchMixMode Threat Research is a dedicated contributor...
Source: securityboulevard.com - Author: Alison Mack Could Secrets Management Be the Key to Unburdening Your Teams?...











![How To Block Apps On Any Device [2025 Guide] – Source: securityboulevard.com](https://ciso2ciso.com/wp-content/uploads/2025/06/176611-how-to-block-apps-on-any-device-2025-guide-source-securityboulevard-com.png)