Source: www.schneier.com - Author: Bruce Schneier Once you build a surveillance system, you can’t control who...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Schneier on Security
Source: www.schneier.com - Author: Bruce Schneier A whole class of speculative execution attacks against CPUs were...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Iranian Blackout Affected Misinformation Campaigns Dozens of accounts on...
Source: www.schneier.com - Author: Bruce Schneier American democracy runs on trust, and that trust is cracking....
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Friday Squid Blogging: What to Do When You Find...
Source: www.schneier.com - Author: Bruce Schneier We need to talk about data integrity. Narrowly, the term...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog White House Bans WhatsApp Reuters is reporting that the...
Source: www.schneier.com - Author: Bruce Schneier Simon Willison talks about ChatGPT’s new memory dossier feature. In...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Mexaly • June 24, 2025 7:25 AM Look...
Source: www.schneier.com - Author: Bruce Schneier It was a recently unimaginable 7.3 Tbps: The vast majority...
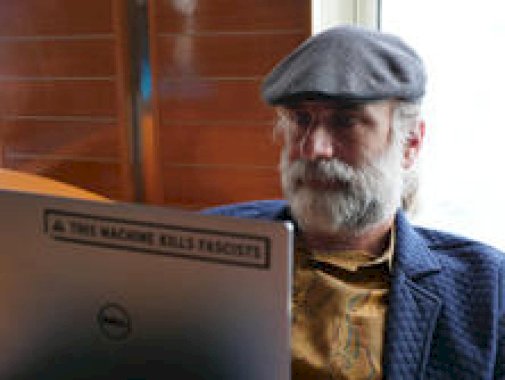
Source: www.schneier.com - Author: Bruce Schneier About Bruce SchneierI am a public-interest technologist, working at the...
Source: www.schneier.com - Author: Bruce Schneier Good article from 404 Media on the cozy surveillance relationship...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Ian Stewart • June 19, 2025 8:36 AM...
Source: www.schneier.com - Author: Bruce Schneier The variations seem to be endless. Here’s a fake ghostwriting...
Source: www.schneier.com - Author: Bruce Schneier If you’ve worried that AI might take your job, deprive...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Friday Squid Blogging: Stubby Squid Video of the stubby...
Source: www.schneier.com - Author: Bruce Schneier Researchers have discovered a new way to covertly track Android...
Source: www.schneier.com - Author: Bruce Schneier Paragon is an Israeli spyware company, increasingly in the news...
Source: www.schneier.com - Author: Bruce Schneier This is news: A data broker owned by the country’s...
Source: www.schneier.com - Author: Bruce Schneier Researchers have discovered a new way to covertly track Android...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Friday Squid Blogging: Squid Run in Southern New England...
Source: www.schneier.com - Author: Bruce Schneier Hearing on the Federal Government and AI On Thursday I...
Source: www.schneier.com - Author: Bruce Schneier OpenAI just published its annual report on malicious uses of...
Source: www.schneier.com - Author: Bruce Schneier You can read the details of Operation Spiderweb elsewhere. What...
Source: www.schneier.com - Author: Bruce Schneier They’re interesting: Tracked as CVE-2025-5054 and CVE-2025-4598, both vulnerabilities are...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Vesselin Bontchev • June 2, 2025 10:38 AM...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Clive Robinson • May 29, 2025 8:52 AM...
Source: www.schneier.com - Author: Bruce Schneier There’s a new cybersecurity awareness campaign: Take9. The idea is...
Source: www.schneier.com - Author: Bruce Schneier About Bruce SchneierI am a public-interest technologist, working at the...
Source: www.schneier.com - Author: Bruce Schneier Russia is proposing a rule that all foreigners in Moscow...