Source: www.schneier.com - Author: Bruce Schneier Google’s vulnerability finding team is again pushing the envelope of...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Schneier on Security
Source: www.schneier.com - Author: Bruce Schneier Clive Robinson • August 7, 2025 8:59 AM @ Bruce,...
Source: www.schneier.com - Author: Bruce Schneier Earlier this week, the Trump administration narrowed export controls on...
Source: www.schneier.com - Author: Bruce Schneier About Bruce SchneierI am a public-interest technologist, working at the...
Source: www.schneier.com - Author: Bruce Schneier An Arizona woman was sentenced to eight-and-a-half years in prison...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Friday Squid Blogging: A Case of Squid Fossil Misidentification...
Source: www.schneier.com - Author: Bruce Schneier Airportr is a service that allows passengers to have their...
Source: www.schneier.com - Author: Bruce Schneier Peter Gutmann and Stephan Neuhaus have a new paper—I think...
Source: www.schneier.com - Author: Bruce Schneier The current state of digital identity is a mess. Your...
Source: www.schneier.com - Author: Bruce Schneier “Who’s winning on the internet, the attackers or the defenders?”...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Clive Robinson • July 29, 2025 12:44 PM...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Steve • July 28, 2025 5:44 PM The...
Source: www.schneier.com - Author: Bruce Schneier Chinese hackers are exploiting a high-severity vulnerability in Microsoft SharePoint...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments not important • July 25, 2025 7:22 PM...
Source: www.schneier.com - Author: Bruce Schneier Today’s freaky LLM behavior: We study subliminal learning, a surprising...
Source: www.schneier.com - Author: Bruce Schneier The current state of digital identity is a mess. Your...
Source: www.schneier.com - Author: Bruce Schneier It will be interesting to watch what will come of...
Source: www.schneier.com - Author: Bruce Schneier Law journal article that looks at the Dual_EC_PRNG backdoor from...
Source: www.schneier.com - Author: Bruce Schneier ProPublica is reporting: Microsoft is using engineers in China to...
Source: www.schneier.com - Author: Bruce Schneier Beautiful photo. Difficult to capture, this mysterious, squid-shaped interstellar cloud...
Source: www.schneier.com - Author: Bruce Schneier The Chinese have a new tool called Massistant. Massistant is...
Source: www.schneier.com - Author: Bruce Schneier The ICEBlock tool has vulnerabilities: The developer of ICEBlock, an...
Source: www.schneier.com - Author: Bruce Schneier Seems like an old system system that predates any care...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments anon • July 14, 2025 5:50 PM From...
Source: www.schneier.com - Author: Bruce Schneier New research: One reason the early years of squids has...
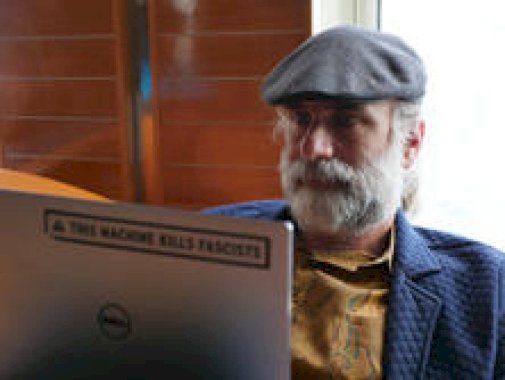
Source: www.schneier.com - Author: Bruce Schneier About Bruce SchneierI am a public-interest technologist, working at the...
Source: www.schneier.com - Author: Bruce Schneier Menu Blog Newsletter Books Essays News Talks Academic About Me...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Swede • July 9, 2025 8:38 AM well...
Source: www.schneier.com - Author: Bruce Schneier Academic papers were found to contain hidden instructions to LLMs:...
Source: www.schneier.com - Author: Bruce Schneier About Bruce SchneierI am a public-interest technologist, working at the...