Source: www.schneier.com - Author: Bruce Schneier Microsoft is reporting that a Russian intelligence agency—the same one...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Schneier on Security
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Friday Squid Blogging: Footage of Black-Eyed Squid Brooding Her...
Source: www.schneier.com - Author: Bruce Schneier For most of history, communicating with a computer has not...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Quantum Computing Skeptics Interesting article. I am also skeptical...
Source: www.schneier.com - Author: Bruce Schneier Poisoning AI Models New research into poisoning AI models: The...
Source: www.schneier.com - Author: Bruce Schneier Really interesting research: “Lend Me Your Ear: Passive Remote Physical...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Tom • January 22, 2024 8:12 AM Something...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Friday Squid Blogging: New Foods from Squid Fins We...
Source: www.schneier.com - Author: Bruce Schneier Okay, so this is weird. Zelle has been using my...
Source: www.schneier.com - Author: Bruce Schneier This is a fascinating story. Last spring, a friend of...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Canadian Citizen Gets Phone Back from Police After 175...
Source: www.schneier.com - Author: Bruce Schneier Interesting research: “Do Users Write More Insecure Code with AI...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Chris Becke • January 16, 2024 8:18 AM...
Source: www.schneier.com - Author: Bruce Schneier About Bruce SchneierI am a public-interest technologist, working at the...
Source: www.schneier.com - Author: B. Schneier About Bruce SchneierI am a public-interest technologist, working at the...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Clive Robinson • January 12, 2024 6:35 PM...
Source: www.schneier.com - Author: Bruce Schneier New law journal article: Smart Device Manufacturer Liability and Redress...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Clive Robinson • January 11, 2024 8:58 AM...
Source: www.schneier.com - Author: Bruce Schneier In 2000, I wrote: “If McDonald’s offered three free Big...
Source: www.schneier.com - Author: Bruce Schneier This is an old piece of malware—the Chameleon Android banking...
Source: www.schneier.com - Author: Bruce Schneier Last month, I convened the Second Interdisciplinary Workshop on Reimagining...
Source: www.schneier.com - Author: Bruce Schneier Friday Squid Blogging—18th Anniversary Post: New Species of Pygmy Squid...
Source: www.schneier.com - Author: Bruce Schneier We don’t have a useful quantum computer yet, but we...
Source: www.schneier.com - Author: Bruce Schneier Kaspersky researchers are detailing “an attack that over four years...
Source: www.schneier.com - Author: Bruce Schneier Kaspersky researchers are detailing “an attack that over four years...
Source: www.schneier.com - Author: Bruce Schneier A helpful summary of which US retail stores are using...
Source: www.schneier.com - Author: Bruce Schneier TikTok seems to be skewing things in the interests of...
Source: www.schneier.com - Author: Bruce Schneier Wow: To test PIGEON’s performance, I gave it five personal...
Source: www.schneier.com - Author: Bruce Schneier They’re short unique strings: Sqids (pronounced “squids”) is an open-source...
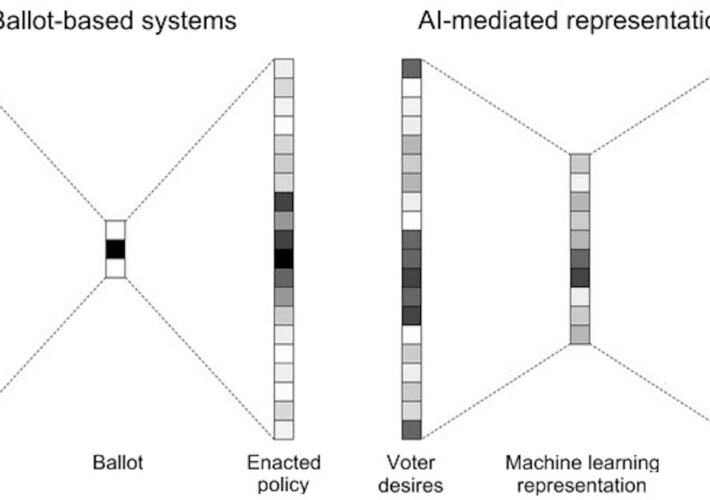
Source: www.schneier.com - Author: B. Schneier Artificial intelligence is poised to upend much of society, removing...