Source: www.schneier.com - Author: B. Schneier Artificial intelligence (AI) has been billed as the next frontier...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Schneier on Security
Source: www.schneier.com - Author: Bruce Schneier In the first week of January, the pharmaceutical giant Merck...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog China Surveillance Company Hacked Last week, someone posted something...
Source: www.schneier.com - Author: Bruce Schneier Apple announced PQ3, its post-quantum encryption standard based on the...
Source: www.schneier.com - Author: Bruce Schneier AIs Hacking Websites New research: LLM Agents can Autonomously Hack...
Source: www.schneier.com - Author: Bruce Schneier echo • February 23, 2024 6:17 PM Originally I had...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog New Image/Video Prompt Injection Attacks Simon Willison has been...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Details of a Phone Scam First-person account of someone...
Source: www.schneier.com - Author: Bruce Schneier Microsoft announced that it caught Chinese, Russian, and Iranian hackers...
Source: www.schneier.com - Author: Bruce Schneier The European Court of Human Rights has ruled that breaking...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Friday Squid Blogging: Vegan Squid-Ink Pasta It uses black...
Source: www.schneier.com - Author: Bruce Schneier Good essay on software bloat and the insecurities it causes....
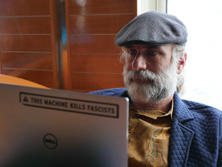
Source: www.schneier.com - Author: B. Schneier About Bruce SchneierI am a public-interest technologist, working at the...
Source: www.schneier.com - Author: Bruce Schneier The winner of the Best Paper Award at Crypto this...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog A Hacker’s Mind is Out in Paperback The paperback...
Source: www.schneier.com - Author: Bruce Schneier Molly White—of “Web3 is Going Just Great” fame—reviews Chris Dixon’s...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Matt • February 12, 2024 12:39 PM Nice...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Anonymous • February 9, 2024 8:39 PM “Philadelphia...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog No, Toothbrushes Were Not Used in a Massive DDoS...
Source: www.schneier.com - Author: Bruce Schneier On Software Liabilities Over on Lawfare, Jim Dempsey published a...
Source: www.schneier.com - Author: Bruce Schneier Interesting research: “Sleeper Agents: Training Deceptive LLMs that Persist Through...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Clive Robinson • February 6, 2024 3:23 PM...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments B.J. Herbison • February 5, 2024 11:36 AM...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Friday Squid Blogging: Illex Squid in Argentina Waters Argentina...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments sam • February 2, 2024 5:18 PM I...
Source: www.schneier.com - Author: Bruce Schneier In 2009, I wrote: There are several ways two people...
Source: www.schneier.com - Author: Bruce Schneier Consumer Reports is reporting that Facebook has built a massive...
Source: www.schneier.com - Author: Bruce Schneier In October, the Consumer Financial Protection Bureau (CFPB) proposed a...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments tfb • January 30, 2024 5:05 PM I...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments whoops • January 30, 2024 7:58 AM The...