Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Vampire Power Adapter • April 1, 2024 11:37...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Schneier on Security
Source: www.schneier.com - Author: Bruce Schneier Ross Anderson Ross Anderson unexpectedly passed away Thursday night in,...
Source: www.schneier.com - Author: Bruce Schneier New York Times op-ed on the Chinese dominance of the...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Carl Engelbrecht • March 29, 2024 7:53 AM...
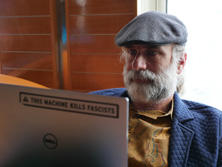
Source: www.schneier.com - Author: B. Schneier About Bruce SchneierI am a public-interest technologist, working at the...
Source: www.schneier.com - Author: Bruce Schneier It’s yet another hardware side-channel attack: The threat resides in...
Source: www.schneier.com - Author: Bruce Schneier It’s pretty devastating: Today, Ian Carroll, Lennert Wouters, and a...
Source: www.schneier.com - Author: Bruce Schneier Andrew Appel shepherded a public comment—signed by twenty election cybersecurity...
Source: www.schneier.com - Author: Bruce Schneier Licensing AI Engineers The debate over professionalizing software engineers is...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Friday Squid Blogging: New Species of Squid Discovered A...
Source: www.schneier.com - Author: Bruce Schneier BleepingComputer has the details. It’s $2M less than in 2022,...
Source: www.schneier.com - Author: Bruce Schneier This mini-essay was my contribution to a round table on...
Source: www.schneier.com - Author: Bruce Schneier The Wall Street Journal is reporting on a variety of...
Source: www.schneier.com - Author: Bruce Schneier Oh, how the mighty have fallen. A decade ago, social...
Source: www.schneier.com - Author: Bruce Schneier Fascinating analysis of the use of drones on a modern...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments This message will be deleted... • March 15,...
Source: www.schneier.com - Author: Bruce Schneier Improving C++ C++ guru Herb Sutter writes about how we...
Source: www.schneier.com - Author: Bruce Schneier Kasmir Hill has the story: Modern cars are internet-enabled, allowing...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Jan Doggen • March 13, 2024 7:26 AM...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Peter A. • March 12, 2024 9:07 AM...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Flerfer • March 11, 2024 9:56 AM I’ve...
Source: www.schneier.com - Author: Bruce Schneier Newly discovered plant looks like a squid. And it’s super...
Source: www.schneier.com - Author: Bruce Schneier The Ash Center has posted a series of twelve essays...
Source: www.schneier.com - Author: Bruce Schneier With the world’s focus turning to misinformation, manipulation, and outright...
Source: www.schneier.com - Author: Bruce Schneier Researchers ran a global prompt hacking competition, and have documented...
Source: www.schneier.com - Author: Bruce Schneier The Washington Post is reporting on the FBI’s increasing use...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog The Insecurity of Video Doorbells Consumer Reports has analyzed...
Source: www.schneier.com - Author: Bruce Schneier Researchers have demonstrated a worm that spreads through prompt injection....
Source: www.schneier.com - Author: Bruce Schneier Paleontologists have discovered a 183-million-year-old species of vampire squid. Prior...
Source: www.schneier.com - Author: Bruce Schneier NIST has released version 2.0 of the Cybersecurity Framework: The...