Source: www.schneier.com - Author: Bruce Schneier A couple of months ago, a new paper demonstrated some...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Schneier on Security
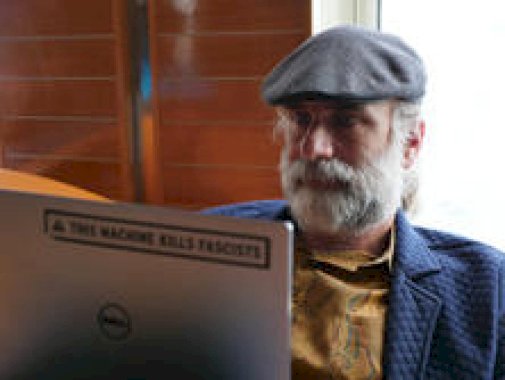
Source: www.schneier.com - Author: Bruce Schneier About Bruce SchneierI am a public-interest technologist, working at the...
Source: www.schneier.com - Author: Bruce Schneier Just a few months after Elon Musk’s retreat from his...
Source: www.schneier.com - Author: Bruce Schneier New research (paywalled): Editor’s summary: Cephalopods are one of the...
Source: www.schneier.com - Author: Bruce Schneier I am pleased to announce the imminent publication of my...
Source: www.schneier.com - Author: Bruce Schneier Interesting experiment: To design their experiment, the University of Pennsylvania...
Source: www.schneier.com - Author: Bruce Schneier Anthropic reports on a Claude user: We recently disrupted a...
Source: www.schneier.com - Author: Bruce Schneier Really good research on practical attacks against LLM agents. “Invitation...
Source: www.schneier.com - Author: Bruce Schneier In the early 1960s, National Security Agency cryptanalyst and cryptanalysis...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Anonymous • August 29, 2025 7:33 PM https://www.yahoo.com/news/articles/identical-twin-convicted-rape-cold-175405227.html...
Source: www.schneier.com - Author: Bruce Schneier I just heard about this: There’s a travel scam warning...
Source: www.schneier.com - Author: Bruce Schneier the hatter • August 28, 2025 10:01 AM @tfb I’m...
Source: www.schneier.com - Author: Bruce Schneier Nice indirect prompt injection attack: Bargury’s attack starts with a...
Source: www.schneier.com - Author: Bruce Schneier I wrote about this in 2023. Here’s the story: Three...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments ThemePro • August 25, 2025 8:07 AM Why...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments ResearcherZero • August 22, 2025 10:14 PM @Name...
Source: www.schneier.com - Author: Bruce Schneier This academic year, I am taking a sabbatical from the...
Source: www.schneier.com - Author: Bruce Schneier Think of the Web as a digital territory with its...
Source: www.schneier.com - Author: Bruce Schneier Well, this is interesting: The auction, which will include other...
Source: www.schneier.com - Author: Bruce Schneier In this input integrity attack against an AI system, researchers...
Source: www.schneier.com - Author: Bruce Schneier A zero-day vulnerability in WinRAR is being exploited by at...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Clive Robinson • August 18, 2025 11:23 AM...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments not important • August 15, 2025 7:23 PM...
Source: www.schneier.com - Author: Bruce Schneier Porn sites are hiding code in .svg files: Unpacking the...
Source: www.schneier.com - Author: Bruce Schneier Here’s an interesting story about a failure being introduced by...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Gadi Evrom • August 13, 2025 1:39 PM...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Clive Robinson • August 13, 2025 8:31 AM...
Source: www.schneier.com - Author: Bruce Schneier A few years ago, scammers invented a new phishing email....
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments Safety first • August 11, 2025 7:28 AM...
Source: www.schneier.com - Author: Bruce Schneier HomeBlog Comments finagle • August 9, 2025 6:47 AM I...