Source: www.govinfosecurity.com - Author: 1 API Security Flaws That Give Back-End Access to an Object Can...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
govinfosecurity.com
Source: www.govinfosecurity.com - Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development...
Source: www.govinfosecurity.com - Author: 1 Governance & Risk Management , IT Risk Management Ilya Sachkov Sentenced...
Source: www.govinfosecurity.com - Author: 1 Fraud Management & Cybercrime , Ransomware Ransomware-Building Group Lost Royal-Organized Competition,...
Source: www.govinfosecurity.com - Author: 1 Governance & Risk Management , SASE , Security Operations Privatise Will...
Source: www.govinfosecurity.com - Author: 1 Email Threat Protection , Fraud Management & Cybercrime , Healthcare Academic...
Source: www.govinfosecurity.com - Author: 1 Incident & Breach Response , Security Operations Wuhan Earthquake Monitoring Center...
Source: www.govinfosecurity.com - Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development...
Source: www.govinfosecurity.com - Author: 1 Application Security , Cloud Security , Next-Generation Technologies & Secure Development...
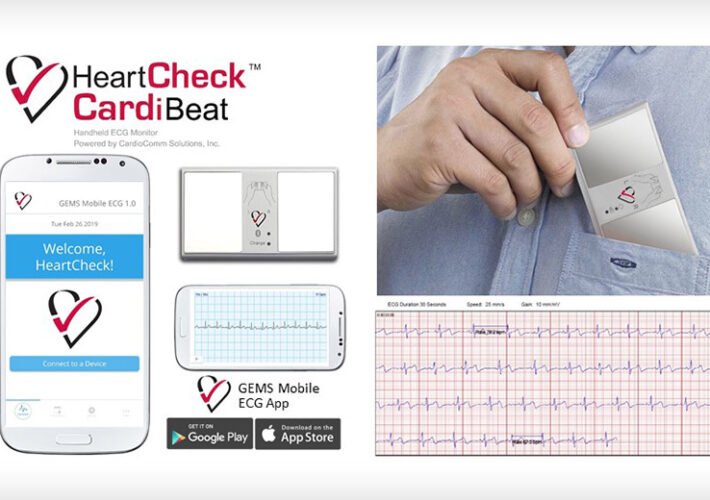
Source: www.govinfosecurity.com - Author: 1 Fraud Management & Cybercrime , Healthcare , Industry Specific CardioComm Says...
Source: www.govinfosecurity.com - Author: 1 Thank you for registering with ISMG Complete your profile and stay...
Source: www.govinfosecurity.com - Author: 1 Paul Shaver Global Practice Leader, Mandiant Mr. Shaver is the Global...
Source: www.govinfosecurity.com - Author: 1 Healthcare , Industry Specific Paramedics Can’t Access NHS Patient Records, Resort...
Source: www.govinfosecurity.com - Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development...
Source: www.govinfosecurity.com - Author: 1 Encryption & Key Management , Security Operations TETRA Algorithms Can Be...
Source: www.govinfosecurity.com - Author: 1 Incident & Breach Response , Security Operations Healthcare Sector Spends Most...
Source: www.govinfosecurity.com - Author: 1 While patient safety risks posed by unpatched security vulnerabilities in legacy...
Source: www.govinfosecurity.com - Author: 1 Security Awareness Programs & Computer-Based Training , Training & Security Leadership...
Source: www.govinfosecurity.com - Author: 1 Cloud Security , Security Operations , Video Cado Security's James Campbell...
Source: www.govinfosecurity.com - Author: 1 3rd Party Risk Management , Governance & Risk Management , Patch...
Source: www.govinfosecurity.com - Author: 1 Security Awareness Programs & Computer-Based Training , Training & Security Leadership...
Source: www.govinfosecurity.com - Author: 1 Fraud Management & Cybercrime , Ransomware Clop's Zero-Day Mass Exploitation and...
Source: www.govinfosecurity.com - Author: 1 Finance & Banking , Fraud Management & Cybercrime , Fraud Risk...
Source: www.govinfosecurity.com - Author: 1 Governance & Risk Management , GRC , Privacy Vendor Cuts Valuation...
Source: www.govinfosecurity.com - Author: 1 HIPAA/HITECH , Standards, Regulations & Compliance Client Files Breached Included Data...
Source: www.govinfosecurity.com - Author: 1 Cryptocurrency Fraud , Finance & Banking , Fraud Management & Cybercrime...
Source: www.govinfosecurity.com - Author: 1 3rd Party Risk Management , Cryptocurrency Fraud , Cyberwarfare / Nation-State...
Source: www.govinfosecurity.com - Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Healthcare...
Source: www.govinfosecurity.com - Author: 1 Thank you for registering with ISMG Complete your profile and stay...
Source: www.govinfosecurity.com - Author: 1 Breach Notification , Fraud Management & Cybercrime , Ransomware Tampa General...