Source: www.databreachtoday.com - Author: 1 Artificial Intelligence & Machine Learning , Governance & Risk Management ,...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Data Breach Today
Source: www.databreachtoday.com - Author: 1 Cloud Security , Next-Generation Technologies & Secure Development , Security Operations...
Source: www.databreachtoday.com - Author: 1 3rd Party Risk Management , AI-Based Attacks , Artificial Intelligence &...
Source: www.databreachtoday.com - Author: 1 3rd Party Risk Management , Cybercrime , Fraud Management & Cybercrime...
Source: www.databreachtoday.com - Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development...
Source: www.databreachtoday.com - Author: 1 Thank you for registering with ISMG Complete your profile and stay...
Source: www.databreachtoday.com - Author: 1 Fraud Management & Cybercrime , Ransomware Is LockBit a Kremlin Sock...
Source: www.databreachtoday.com - Author: 1 Organizations and their employees are using hundreds of SaaS applications every...
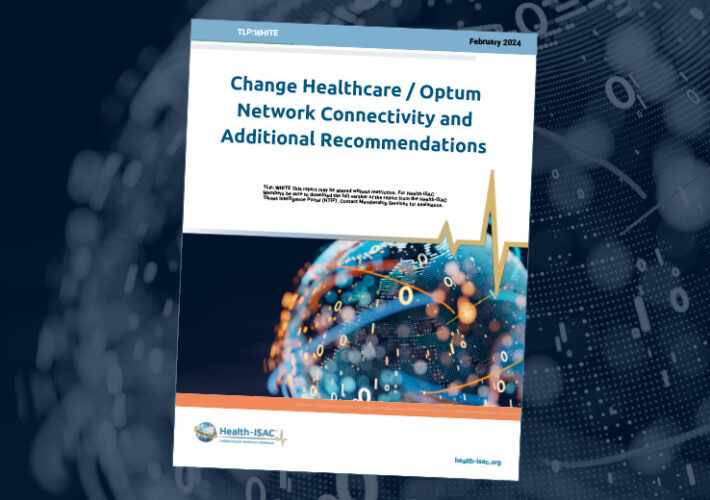
Source: www.databreachtoday.com - Author: 1 The Change Healthcare mega hack has taken nearly 120 of the...
Source: www.databreachtoday.com - Author: 1 Endpoint Security , Governance & Risk Management , Patch Management Gateway...
Source: www.databreachtoday.com - Author: 1 Chris Poulin Director of Technology and Strategy and Deputy CTO, Bitsight...
Source: www.databreachtoday.com - Author: 1 Joe Nicastro Field CTO, Legit Security Joe Nicastro is a seasoned...
Source: www.databreachtoday.com - Author: 1 Multi-factor & Risk-based Authentication , Security Operations Calls Grow to Block...
Source: www.databreachtoday.com - Author: 1 Governance & Risk Management , Operational Technology (OT) , Video Rami...
Source: www.databreachtoday.com - Author: 1 Governance & Risk Management , Network Firewalls, Network Access Control ,...
Source: www.databreachtoday.com - Author: 1 Identity & Access Management , Security Operations Credential Stuffing Plummets, More...
Source: www.databreachtoday.com - Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Training...
Source: www.databreachtoday.com - Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Next-Generation...
Source: www.databreachtoday.com - Author: 1 Cloud Security , Device Identification , Endpoint Security Presented by DigiCert...
Source: www.databreachtoday.com - Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Distributed Denial-of-Service...
Source: www.databreachtoday.com - Author: 1 Fraud Management & Cybercrime , Healthcare , Industry Specific Feds Issue...
Source: www.databreachtoday.com - Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development...
Source: www.databreachtoday.com - Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Next-Generation...
Source: www.databreachtoday.com - Author: 1 Cyberwarfare / Nation-State Attacks , Endpoint Security , Fraud Management &...
Source: www.databreachtoday.com - Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development...
Source: www.databreachtoday.com - Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Government...
Source: www.databreachtoday.com - Author: 1 Encryption & Key Management , Governance & Risk Management , Operational...
Source: www.databreachtoday.com - Author: 1 3rd Party Risk Management , Fraud Management & Cybercrime , Governance...
Source: www.databreachtoday.com - Author: 1 Critical Infrastructure Security , Governance & Risk Management New CSF Adds...
Source: www.databreachtoday.com - Author: 1 Fraud Management & Cybercrime , Ransomware LockBit Leader Vows to Continue...