Source: www.darkreading.com - Author: Ericka Chickowski, Contributing Writer The biggest vulnerabilities may lie at the boundaries...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Dark Reading Security
Source: www.darkreading.com - Author: Nate Nelson, Contributing Writer TAG-150 is running a multifaceted and relatively successful...
Source: www.darkreading.com - Author: Nate Nelson, Contributing Writer It's called "grokking," and gives spammers a way...
Source: www.darkreading.com - Author: Arielle Waldman The nonprofit training organization's new program addresses digital forensics, incident...
Source: www.darkreading.com - Author: Bruce Johnson Programs like student-run SOCs can expand our cybersecurity workforce and...
Source: www.darkreading.com - Author: Robert Lemos, Contributing Writer Cyberattackers target local and state agencies, a problem...
Source: www.darkreading.com - Author: Dark Reading Staff The addition of Black Duck's application security testing offering...
Source: www.darkreading.com - Author: Rob Wright The vulnerability marks the latest example of threat actors weaponizing...
Source: www.darkreading.com - Author: Kristina Beek Reports of disruptions at North American plants emerged earlier this...
Source: www.darkreading.com - Author: Jai Vijayan, Contributing Writer New threat actor "GhostRedirector" is using a malicious...
Source: www.darkreading.com - Author: Arielle Waldman The Nonprofit organization launched the Threat Handling Foundations Certificate amid...
Source: www.darkreading.com - Author: Elizabeth Montalbano, Contributing Writer What's believed to be a global phishing-as-a-service enterprise...
Source: www.darkreading.com - Author: Alexander Culafi Czech cyber agency NÚKIB warned of the risks of using...
Source: www.darkreading.com - Author: Alexander Culafi Many high-profile Salesloft Drift customers have disclosed data breaches as...
Source: www.darkreading.com - Author: Robert Lackey The more you hunt, the more you learn. Original Post...
Source: www.darkreading.com - Author: Andrada Fiscutean The digital refuge: Abortion clinics, activist groups, and other organizations...
Source: www.darkreading.com - Author: Alex Zaslavsky, SafeLogic This Tech Tip outlines how organizations can make the...
Source: www.darkreading.com - Author: Kristina Beek It's the equivalent of watching more than 9,350 full-length HD...
Source: www.darkreading.com - Author: Nate Nelson, Contributing Writer The Homeland Justice APT tried spying on countries...
Source: www.darkreading.com - Author: Robert Lemos, Contributing Writer With the continued success of North Korea's IT...
Source: www.darkreading.com - Author: Rob Wright The notorious Russian state-sponsored hacking unit, also known as Fancy...
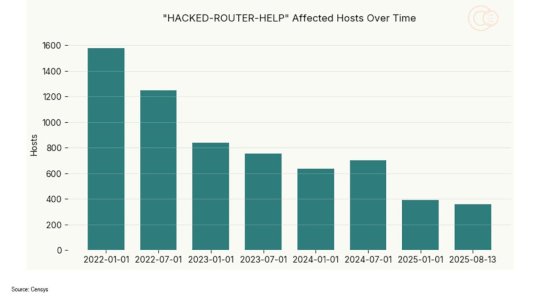
Source: www.darkreading.com - Author: Fahmida Y. Rashid While trawling Internet scan data for signs of compromised...
Source: www.darkreading.com - Author: Elizabeth Montalbano, Contributing Writer A "sophisticated" attack that also exploits an Apple...
Source: www.darkreading.com - Author: Jeffrey Schwartz Varonis plans to integrate SlashNext's advanced phishing, BEC, and social...
Source: www.darkreading.com - Author: Kristina Beek The initiative will be tailored to students and their growth...
Source: www.darkreading.com - Author: Jai Vijayan, Contributing Writer A group linked to Russian intelligence services redirected...
Source: www.darkreading.com - Author: Rob Wright Vulnerable and malicious plug-ins are giving threat actors the ability...
Source: www.darkreading.com - Author: Alexander Culafi Two major security firms suffered downstream compromises as part of...
Source: www.darkreading.com - Author: Kristina Beek The luxury automaker said its retail and production activities have...
Source: www.darkreading.com - Author: Ensar Seker You can't negotiate with hackers from a place of fear...