Source: www.bleepingcomputer.com – Author: Sergiu Gatlan

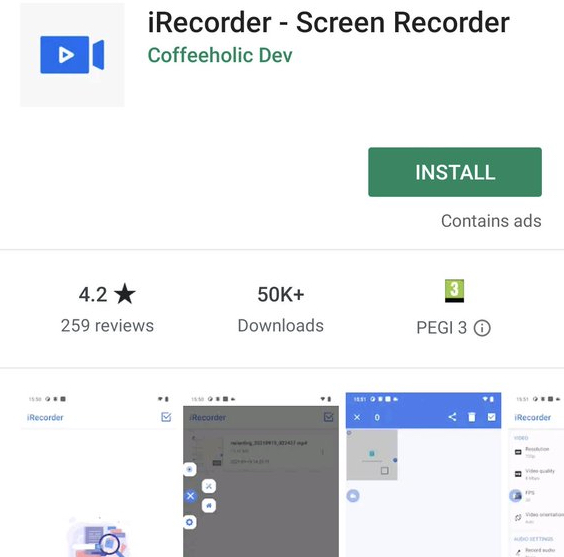
ESET malware researchers found a new remote access trojan (RAT) on the Google Play Store, hidden in an Android screen recording app with tens of thousands of installs.
While first added to the store in September 2021, the ‘iRecorder – Screen Recorder’ app was likely trojanized via a malicious update released almost a year later, in August 2022.
The app’s name made it easier to ask permission to record audio and access files on the infected devices since the request matched the expected capabilities of a screen recording tool.
Before its removal, the app amassed over 50,000 installations on the Google Play Store, exposing users to malware infections.
“Following our notification regarding iRecorder’s malicious behavior, the Google Play security team removed it from the store,” ESET malware researcher Lukas Stefanko said.
“However, it is important to note that the app can also be found on alternative and unofficial Android markets. The iRecorder developer also provides other applications on Google Play, but they don’t contain malicious code.”
The malware in question, named AhRat by ESET, is based on an open-source Android RAT known as AhMyth.
It has a wide range of capabilities, including but not limited to tracking infected devices’ location, stealing call logs, contacts, and text messages, sending SMS messages, taking pictures, and recording background audio.
Upon closer examination, ESET found that the malicious screen recording app itself only used a subset of the RAT’s capabilities as it was used only to create and exfiltrate ambient sound recordings and to steal files with specific extensions, hinting at potential espionage activities.
This isn’t the first instance of AhMyth-based Android malware infiltrating the Google Play store. ESET also published details in 2019 on another AhMyth-trojanized app that tricked Google’s app-vetting process twice by masquerading as a radio streaming app.
“Previously, the open-source AhMyth was employed by Transparent Tribe, also known as APT36, a cyberespionage group known for its extensive use of social engineering techniques and targeting government and military organizations in South Asia,” Stefanko said.
“Nevertheless, we cannot ascribe the current samples to any specific group, and there are no indications that they were produced by a known advanced persistent threat (APT) group.”
Original Post URL: https://www.bleepingcomputer.com/news/security/new-ahrat-android-malware-hidden-in-app-with-50-000-installs/
Category & Tags: Security – Security
Views: 1