Source: securityaffairs.com – Author: Pierluigi Paganini

Huntress reports active exploitation of Gladinet CVE-2025-30406 in the wild, affecting seven organizations and 120 endpoints.
Security researchers at Huntress warn of attacks in the wild exploiting a critical vulnerability, tracked as CVE-2025-30406, in Gladinet CentreStack and Triofox software.
The vulnerability CVE-2025-30406 (CVSS score 9.0) is a deserialization issue due to the CentreStack portal’s hardcoded machineKey use. Threat actors exploited the flaw in March attacks.
The vulnerability has been addressed in version 16.4.10315.56368 released on April 3, 2025.
“The application uses a hardcoded or improperly protected machineKey in the IIS web.config file, which is responsible for securing ASP.NET ViewState data. If an attacker obtains or predicts the machineKey, they can forge ViewState payloads that pass integrity checks. In some scenarios, this can result in ViewState deserialization attacks, potentially leading to remote code execution (RCE) on the web server. Exploitation has been observed in the wild.” reads the advisory. “We strongly recommend updating to the patched version, which improves key management and mitigates exposure. For customers who cannot update immediately, rotating the machineKey values is a recommended interim mitigation.”
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the flaw to its Known Exploited Vulnerabilities (KEV) catalog in April 2025.
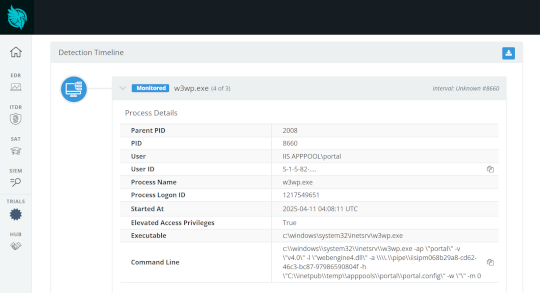
On April 11, 2025, Huntress detected suspicious activity linked to Gladinet CentreStack, tied to CVE-2025-30406. At least seven organizations were compromised by exploiting this zero-day.

The researchers pointed out that a few hundred vulnerable servers exposed to the Internet are at risk.
The CVE-2025-30406 flaw in Gladinet CentreStack and Triofox stems from hardcoded keys in web.config files, enabling ViewState deserialization attacks. If unpatched, this allows remote code execution and full server compromise. Both root and portal configs must be secured to prevent exploitation.
“This weakness can be leveraged to abuse the ASPX ViewState, a mechanism used to preserve the state of a web page and its controls between multiple HTTP requests. The hardcoded keys open the door for a very standard and well-researched attack technique with ViewState deserialization.” reads the report published by cybersecurity firm Huntress. “If a Gladinet CentreStack or Triofox server is exposed to the Internet with these hardcoded keys, it is in immediate danger and needs to be patched or have the machineKey values changed as soon as possible. CVE-2025-30406 is known to be actively exploited by threat actors, and this 9.0 critical severity issue has no “prerequisites” other than knowing the default key values.”
Exploiting CVE-2025-30406 allows remote code execution as IISAPPPOOLportaluser, with easy privilege escalation to SYSTEM. Huntress demonstrated the risk with a working proof-of-concept exploit targeting Triofox web.config files.
“We don’t have any intentions of sharing the proof-of-concept to embolden other adversaries, but once an external exploit is shared publicly we will update this blog to include the technical details of recreating the attack script.” continues the report. “We can confirm the Gladinet CentreStack and Triofox patches are effective in stopping exploitation from our tested proof-of-concept.”
In one attack, Huntress spotted an encoded PowerShell command used to download and run a DLL, the experts noticed that the technique was also seen in recent CrushFTP vulnerability exploits.
The researchers observed the threat actors using lateral movement to install MeshCentral remote access tools. On the second host, attackers executed Impacket commands, MeshAgent, and Centre.exe.
Huntress found approximately 120 endpoints running vulnerable Gladinet CentreStack software and is urging partners to patch CVE-2025-30406. The company released detection tools and Sigma rules.
Gradient addressed the flaw and confirmed that the issue is actively exploited.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Gladinet)
Original Post URL: https://securityaffairs.com/176552/hacking/gladinet-flaw-cve-2025-30406-actively-exploited-in-the-wild.html
Category & Tags: Breaking News,Hacking,Security,CVE-2025-30406,Gladinet,hacking news,information security news,IT Information Security,Pierluigi Paganini,Security Affairs,Security News – Breaking News,Hacking,Security,CVE-2025-30406,Gladinet,hacking news,information security news,IT Information Security,Pierluigi Paganini,Security Affairs,Security News
Views: 4