The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Hack on Sony Group Pictures Entertainment
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
SOC sin SIEM
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
SOC AUDIT REPORT TYPE 1 AND TYPE 2
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
SME Guide on Information Security Controls
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Six essential ingredients of a modern Security Operations Center (SOC)
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Chemical Sector Cyber Tabletop Exercise
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Signs of a Data Breach
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Shell code development
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
SHARPENING TECHNIQUES WITH IMPACKET
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Security of digital products and services: Reducing vulnerabilities and secure design
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
An interview with CISO Mardecia Bell, a storied career – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: In this edited interview excerpt from the CISO’s Secrets podcast, CISO Mardecia Bell unpacks what it’s like to serve...
MY TAKE: How decentralizing IoT could help save the planet — by driving decarbonization – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Byron V. Acohido The Internet of Things (IoT) is on the threshold of ascending to become the Internet of Everything...
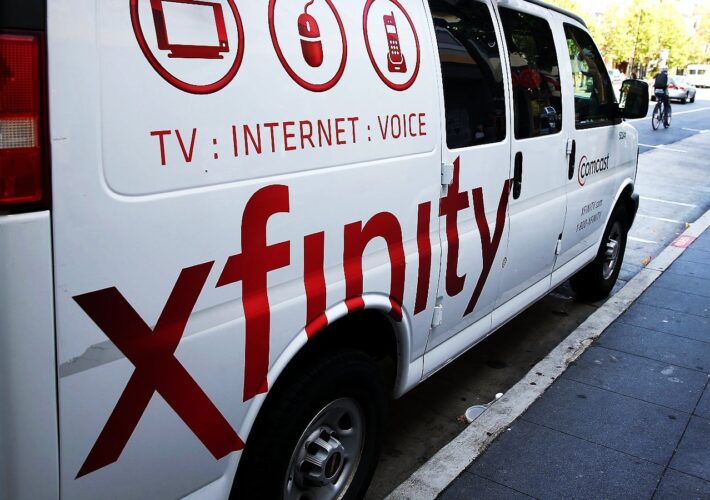
Xfinity discloses data breach after recent Citrix server hack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Comcast Cable Communications, doing business as Xfinity, disclosed on Monday that attackers who breached one of its Citrix servers in...
December’s Windows 11 KB5033375 update breaks Wi-Fi connectivity – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The KB5033375 cumulative update released during the December 2023 Patch Tuesday causes Wi-Fi connectivity issues on some Windows 11 devices....
Microsoft discovers critical RCE flaw in Perforce Helix Core Server – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Four vulnerabilities, one of which is rated critical, have been discovered in the Perforce Helix Core Server, a source code...
Vans and North Face owner VF Corp hit by ransomware attack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas American global apparel and footwear giant VF Corporation, the owner of brands like Supreme, Vans, Timberland, and The North Face,...
Microsoft fixes Windows printer issues with new troubleshooter – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft has released a new troubleshooter tool to fix an issue where the HP Smart app would automatically install on...
FBI: Play ransomware breached 300 victims, including critical orgs – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The Federal Bureau of Investigation (FBI) says the Play ransomware gang has breached roughly 300 organizations worldwide between June 2022...
Former IT manager pleads guilty to attacking high school network – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Conor LaHiff, a former IT manager for a New Jersey public high school, has admitted to committing a cyberattack against...
Mortgage giant Mr. Cooper data breach affects 14.7 million people – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Mr. Cooper is sending data breach notifications warning that a recent cyberattack has exposed the data of 14.7 million customers...
Security by Design Framework
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
SECURITY PLANNING WORKBOOK
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
SECURE INNOVATION
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
AI-POWERED CYBERSECURITY AND EVOLVING AI THREATS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Securing the Software Supply Chain: Recommended Practices for Software Bill of Materials Consumption
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
SECURING IDENTITY ACCESS MANAGEMENT (IAM) PLATFORMS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The ransomware attack on Westpole is disrupting digital services for Italian public administration – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The ransomware attack on Westpole is disrupting digital services for Italian public administration Pierluigi Paganini December 19, 2023 An alleged...
Info stealers and how to protect against them – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Info stealers and how to protect against them Pierluigi Paganini December 18, 2023 Info stealers, the type of malware with...
Pro-Israel Predatory Sparrow hacker group disrupted services at around 70% of Iran’s fuel stations – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Pro-Israel Predatory Sparrow hacker group disrupted services at around 70% of Iran’s fuel stations Pierluigi Paganini December 18, 2023 A...