Continental, the Newest Victim of LockBit RansomwareLockBit, one of the most notorious ransomware gangs around, is claiming responsibility for a cyberattack that hit the German auto...
Robin Banks phishing-as-a-service platform continues to evolve
Robin Banks phishing-as-a-service platform continues to evolveThe phishing-as-a-service (PhaaS) platform Robin Banks migrated its infrastructure to DDoS-Guard, a Russian bulletproof hosting service. The phishing-as-a-service (PhaaS) platform Robin...
American and Israeli Water Sectors Are Unprepared for Cyber Attacks
American and Israeli Water Sectors Are Unprepared for Cyber AttacksFormer Israeli Air Force captain Ariel Stern warns that the US and Israel are currently unprepared to...
Black Basta Ransomware Attack Detection: Recent Malicious Campaigns Using New Custom Tools Attributed to the FIN7 Group
Black Basta Ransomware Attack Detection: Recent Malicious Campaigns Using New Custom Tools Attributed to the FIN7 Group The Black Basta ransomware group emerged in the cyber...
Medibank refuses to pay ransom after 9.7 million health insurance customers have their data stolen
Medibank refuses to pay ransom after 9.7 million health insurance customers have their data stolenEmbattled Australian health insurer Medibank says that it will not pay a...
The Conviction of Uber’s Chief Security Officer
The Conviction of Uber’s Chief Security OfficerI have been meaning to write about Joe Sullivan, Uber’s former Chief Security Officer. He was convicted of crimes related...
Mastodon now has over 1 million users amid Twitter tensions
Mastodon now has over 1 million users amid Twitter tensionsMastodon, the free, open-source, decentralized micro-blogging social media platform, has surpassed a million monthly active users for...
How Cyberbullying Looks In Australia in 2022
How Cyberbullying Looks In Australia in 2022 There’s no doubt that cyber bullying ranks towards the top of most parents ‘worry list’. As a mum of...
Ransomware gang threatens to release stolen Medibank data
Ransomware gang threatens to release stolen Medibank dataA ransomware gang that some believe is a relaunch of REvil and others track as BlogXX has claimed responsibility...
Massive Phishing Campaigns Target India Banks’ Clients
Massive Phishing Campaigns Target India Banks’ ClientsWe found five banking malware families targeting customers of seven banks in India to steal personal and credit card information...
Maple Leaf Foods suffers outage following weekend cyberattack
Maple Leaf Foods suffers outage following weekend cyberattackMaple Leaf Foods confirmed on Sunday that it experienced a cybersecurity incident causing a system outage and disruption of...
Microsoft WinGet package manager failing due to CDN issues
Microsoft WinGet package manager failing due to CDN issuesMicrosoft's WinGet package manager is currently having problems installing or upgrading packages due to the Azure Content Delivery Network...
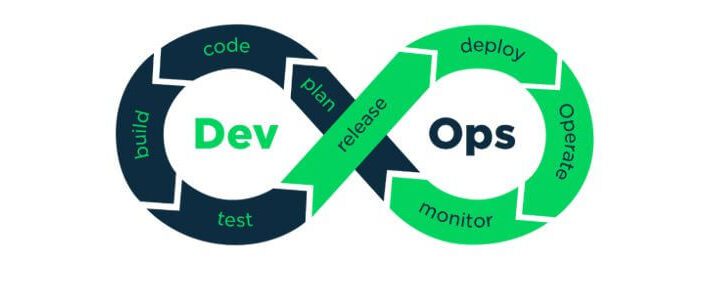
Key challenges of shift-left tactics
Key challenges of shift-left tacticsBy Musa Nadir Sani. Software development has continued to evolve over the years, with developers pushing to release applications in the shortest...
Endpoint Protection is Key When it Comes to Cyber Insurance
Endpoint Protection is Key When it Comes to Cyber InsuranceWhy is endpoint detection and response (EDR) considered non-negotiable for companies seeking catastrophic coverage for cyber incidents...
Live Webinar | Identity Security as a Transformation Accelerant in the Insurance Sector
Live Webinar | Identity Security as a Transformation Accelerant in the Insurance SectorContenido de la entradaLeer másDataBreachToday.com RSS Syndication
Getting Started with NSX Application Platform (NAPP)
Getting Started with NSX Application Platform (NAPP)Introducing the platform The NSX Application Platform (NAPP) is a high-performance security analytics platform that hosts microservices-based applications (Figure 1.1)....
Medibank Says No to Paying Hacker’s Extortion Demand
Medibank Says No to Paying Hacker's Extortion DemandGroup Claiming Affiliation With REvil Threatens to Release DataEmbattled Australian private health insurer Medibank says it won't pay hackers'...
Medibank says it won’t pay ransom for customer data stolen in cyber-attack
Medibank says it won’t pay ransom for customer data stolen in cyber-attack‘Limited chance’ such a move would result in return of data or prevent it being...
SHARED INTEL: The non-stop advance and diversification of ransomware extortion tactics
SHARED INTEL: The non-stop advance and diversification of ransomware extortion tacticsCybercriminals are becoming more creative as cybersecurity analysts adapt quickly to new ransomware strategies. Related: How...
6 ways to reduce your IoT attack surface
6 ways to reduce your IoT attack surfaceAs attackers target the ever-growing IoT attack surface, companies can reduce their risks with these six security best practices....
A Guide to Remove Malware From Your iPhone
A Guide to Remove Malware From Your iPhone Malicious software, or “malware,” refers to any program designed to infect and disrupt computer systems and networks. The...
What Is Encrypted DNS Traffic?
What Is Encrypted DNS Traffic?Encrypted DNS traffic is a type of DNS traffic secured in a way that no third party can intervene during a DNS...
Twitter $8 Fee Exploited by Cybercriminals
Twitter $8 Fee Exploited by CybercriminalsAs Elon Musk took charge of Twitter`s management, there have been some controversial changes implemented, one of them being the $8 a...
RomCom RAT campaigns abuses popular brands like KeePass and SolarWinds NPM
RomCom RAT campaigns abuses popular brands like KeePass and SolarWinds NPMA new campaign spreading RomCom RAT impersonates popular software brands like KeePass, and SolarWinds. The threat...
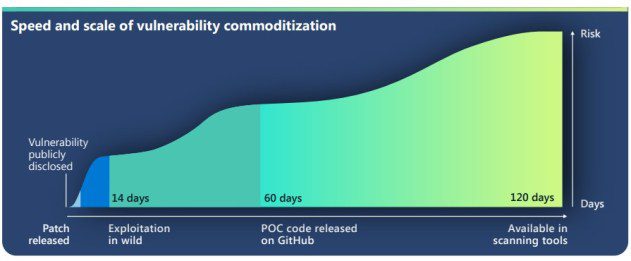
Zero-day are exploited on a massive scale in increasingly shorter timeframes
Zero-day are exploited on a massive scale in increasingly shorter timeframesMicrosoft warns of an uptick among threat actors increasingly using publicly-disclosed zero-day exploits in their attacks....
The Role of Cybersecurity in Accounting
The Role of Cybersecurity in AccountingIt comes as no surprise that cybersecurity is one of the most important topics in this hacker-prone Internet era. A large...
29 malicious PyPI packages spotted delivering the W4SP Stealer
29 malicious PyPI packages spotted delivering the W4SP StealerCybersecurity researchers discovered 29 malicious PyPI packages delivering the W4SP stealer to developers’ systems. Cybersecurity researchers have discovered...
All UK Hosted Internet Devices Will be Scanned by the British Government
All UK Hosted Internet Devices Will be Scanned by the British GovernmentThe United Kingdom’s National Cyber Security Centre (NCSC), the government agency leading UK’s cybersecurity mission,...
A cyberattack blocked the trains in Denmark
A cyberattack blocked the trains in DenmarkAt the end of October, a cyber attack caused the trains to stop in Denmark, the attack hit a third-party...
Robin Banks Relocated to a Russian Server
Robin Banks Relocated to a Russian ServerThe cybercriminals behind Robin Bank have relocated the phishing-as-a-service (PhaaS) platform to a Russian hosting service. DDoS-Guard takes over from...