Happy birthday Security Affairs … 11 years together!Happy BirthDay Security Affairs! Eleven years together! I launched Security Affairs for passion in November 2011 and since then...
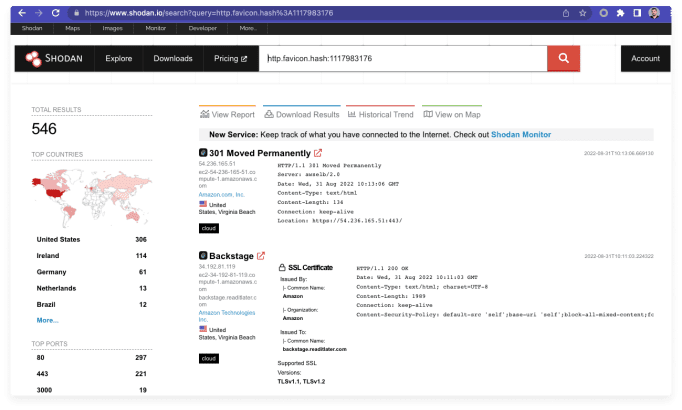
Experts found critical RCE in Spotify’s Backstage
Experts found critical RCE in Spotify’s BackstageResearchers discovered a critical vulnerability impacting Spotify’s Backstage Software Catalog and Developer Platform. Researchers from the security firm Oxeye discovered...
State-Backed APT Group Activity Continuing Apace
State-Backed APT Group Activity Continuing ApaceThe report outlines recent APT group activity from Russia, China, Iran and North KoreaLeer másThe report outlines recent APT group activity...
Beginning 2023 Google plans to rollout the initial Privacy Sandbox Beta
Beginning 2023 Google plans to rollout the initial Privacy Sandbox BetaGoogle announced it will roll out the Privacy Sandbox system for Android in beta to a...
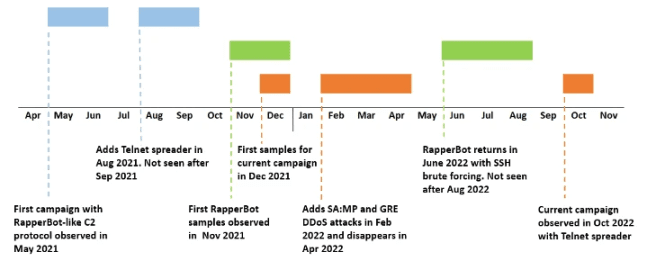
New RapperBot Campaign targets game servers with DDoS attacks
New RapperBot Campaign targets game servers with DDoS attacksFortinet researchers discovered new samples of RapperBot used to build a botnet to launch Distributed DDoS attacks against...
Malicious For-Profit Group Impersonates Brands to Scam Users
Malicious For-Profit Group Impersonates Brands to Scam Users“Fangxiao,” a malicious for-profit company, has created a vast network of over 42,000 domains that imitate well-known companies to...
Billbug Threat Group Ongoing Campaign Unveiled
Billbug Threat Group Ongoing Campaign UnveiledThe threat actor called Billbug (a.k.a. Thrip, Lotus Blossom, Spring Dragon) is responsible for a campaign that targeted a certificate authority,...
High-Severity Flaw Reported in Spotify’s Backstage
High-Severity Flaw Reported in Spotify’s BackstageBackstage, the open-source developer portal from Spotify, has been discovered as vulnerable to a high-severity security flaw that could grant threat actors the...
New RapperBot Campaign Aims to Launch DDoS Attacks on Game Servers
New RapperBot Campaign Aims to Launch DDoS Attacks on Game ServersThe “RapperBot” malware group has been rapidly expanding since mid-June 2022. Researchers discovered new samples of...
Thales Global Tech Company Data Released by Lockbit Ransomware Gang
Thales Global Tech Company Data Released by Lockbit Ransomware GangThe Lockbit 3.0 ransomware group began leaking a 9.5 Gb archive file that is presumably stolen information...
It’s time. Delete your Twitter DMs
It’s time. Delete your Twitter DMsTwitter is in chaos. I'd rather delete my Direct Messages one-by-one than one day find that they are in the hands...
Healthcare sector warned of Venus ransomware attacks
Healthcare sector warned of Venus ransomware attacksHealthcare organisations in the United States are being warned to be on their guard once again, this time against a...
Russian Software Company Pretending to Be American
Russian Software Company Pretending to Be AmericanComputer code developed by a company called Pushwoosh is in about 8,000 Apple and Google smartphone apps. The company pretends...
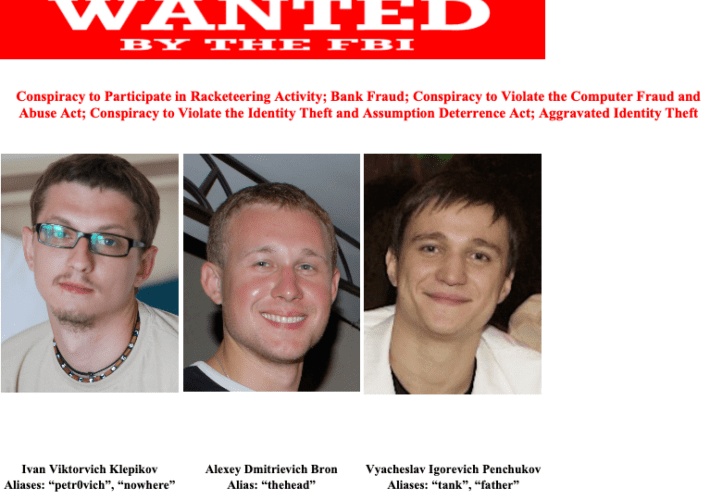
Top Zeus Botnet Suspect “Tank” Arrested in Geneva
Top Zeus Botnet Suspect “Tank” Arrested in GenevaVyacheslav “Tank” Penchukov, the accused 40-year-old Ukrainian leader of a prolific cybercriminal group that stole tens of millions of...
The Medibank Data Breach – Steps You Can Take to Protect Yourself
The Medibank Data Breach – Steps You Can Take to Protect Yourself Hackers have posted another batch of stolen health records on the dark web—following a...
Bitwarden vs 1Password: Password manager comparison
Bitwarden vs 1Password: Password manager comparisonWith password hacks and attacks on the rise, the myriad passwords deployed by companies and individuals can't just be inscrutable, they...
Get instant malware filtering with Gryphon Guardian
Get instant malware filtering with Gryphon GuardianTechRepublic readers can get this tiny mesh router that blocks security threats for only $79. The post Get instant malware...
Data encryption as a crucial step to manage data access and security
Data encryption as a crucial step to manage data access and securityWith data breaches on the rise, encryption has never been more important for protecting companies...
Instagram, Facebook, Twitter, YouTube suspended in Turkey after blast
Instagram, Facebook, Twitter, YouTube suspended in Turkey after blastFollowing yesterday's deadly blast on İstiklal Avenue in Istanbul, Turkish authorities began restricting access to social media including Instagram,...
Top cybersecurity threats for 2023
Top cybersecurity threats for 2023Next year, cybercriminals will be as busy as ever. Are IT departments ready? The post Top cybersecurity threats for 2023 appeared first...
Researchers release exploit details for Backstage pre-auth RCE bug
Researchers release exploit details for Backstage pre-auth RCE bugOlder versions of the Spotify Backstage development portal builder are vulnerable to a critical (CVSS score: 9.8) unauthenticated...
MFA Fatigue attacks are putting your organization at risk
MFA Fatigue attacks are putting your organization at riskA common threat targeting businesses is MFA fatigue attacks—a technique where a cybercriminal attempts to gain access to a...
Windows 10 KB5020030 preview update released with ten improvements
Windows 10 KB5020030 preview update released with ten improvementsMicrosoft has released this month's optional KB5020030 Preview cumulative update for all editions of Windows 10 20H2, 21H1,...
Google to roll out Privacy Sandbox on Android 13 starting early 2023
Google to roll out Privacy Sandbox on Android 13 starting early 2023Google announced today that they will begin rolling out the Privacy Sandbox system on a...
Top 5 email newsletters that will make you smarter in the digital age
Top 5 email newsletters that will make you smarter in the digital ageContributed by George Mack, Content Marketing Manager, Check Point Software. Every day, we are...
The Harris Center for Mental Health & IDD ISO shares perspectives on cyber security
The Harris Center for Mental Health & IDD ISO shares perspectives on cyber securityWes Farris is the Director of Information Security and Enterprise Architecture at The...
What are eavesdropping attacks? Everything you need to know
What are eavesdropping attacks? Everything you need to knowEXECUTIVE SUMMARY: Eavesdropping attacks are easy to execute and exploit inherently insecure or vulnerable networks. Are your network...
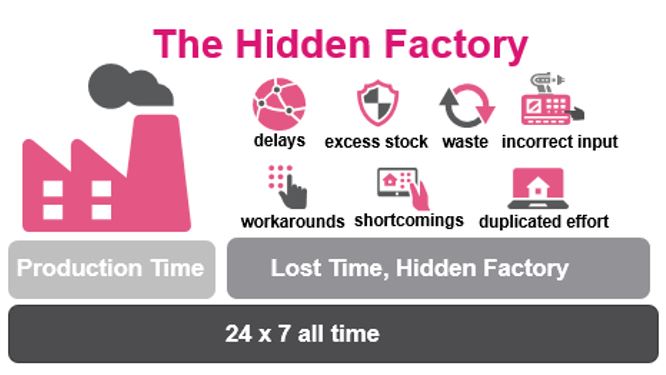
How addressing “Hidden Factory” can boost the transition to “Green Factory”
How addressing “Hidden Factory” can boost the transition to “Green Factory”Antoinette Hodes is a Check Point Solution Architect for the EMEA region and an Evangelist with...
North Korean hackers target European orgs with updated malware
North Korean hackers target European orgs with updated malwareNorth Korean hackers are using a new version of the DTrack backdoor to attack organizations in Europe and...
10 secrets for successful digital transformations
10 secrets for successful digital transformationsEXECUTIVE SUMMARY: Digitize to survive and thrive? Digital transformations account for 40% of all business technology spending, and the digital transformation...