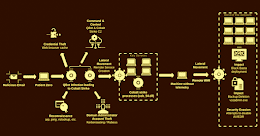
Threat Analysis: Active C2 Discovery Using Protocol Emulation Part4 (Dacls, aka MATA)Dacls, aka MATA, is a cross-platform RAT used by the DPRK-linked Lazarus Group and the...
Setting the Record Straight on XDR at VMware Explore Europe
Setting the Record Straight on XDR at VMware Explore EuropeThere seems to be a bit of confusion as to what constitutes XDR (extended detection and response)....
K82567234: NodeJS vulnerability CVE-2022-32215
K82567234: NodeJS vulnerability CVE-2022-32215NodeJS vulnerability CVE-2022-32215 Security Advisory Security Advisory Description The llhttp parser <v14.20.1, <v16.17.1 and <v18.9.1 in the http module in Node.js does not...
Addressing the Shortage of Medical Device Cyber Talent
Addressing the Shortage of Medical Device Cyber TalentThe shortage of cybersecurity professionals in the United States includes a scarcity of expertise in medical device security, says...
MEPs’ spyware inquiry targeted by disinformation campaign, say experts
MEPs’ spyware inquiry targeted by disinformation campaign, say expertsEuropean parliament is investigating Pegasus, a powerful surveillance tool used by governments around the world Victims of spyware...
Gangs of cybercriminals are expanding across Africa, investigators say
Gangs of cybercriminals are expanding across Africa, investigators sayOnline scams such as banking and credit card fraud are the most prevalent cyberthreat, says Interpol Police and...
Ransomware Group Zeppelin’s Costly Encryption Mistake
Ransomware Group Zeppelin's Costly Encryption MistakeThe latest edition of the ISMG Security Report discusses how the profits of ransomware group Zeppelin have been smashed by security...
Ontario Teachers’ Data Stolen in Ransomware Attack
Ontario Teachers’ Data Stolen in Ransomware AttackVictims Notified of Ransomware Attack Six Months After the IncidentA cyberattack on a Canadian teachers’ union gave thieves access to...
Multiple Arrests in Coordinated African Cyber Operation
Multiple Arrests in Coordinated African Cyber OperationLaw Enforcement Agencies Also Took Down 200,000 Cyber Infrastructure CrooksA 27-nation joint investigation in Africa led to the arrest of...
Cyber Resilience Minimizes Risks for Digital Services
Cyber Resilience Minimizes Risks for Digital ServicesResiliency Leader Kris Lovejoy on the Convergence of Security and Disaster RecoveryCyber resilience extends beyond cyberattacks and encompasses the convergence...
SharkBot Trojan Spread Via Android File Manager Apps
SharkBot Trojan Spread Via Android File Manager AppsNow-Removed Apps Have 10K Downloads, Target Victims in the UK, ItalyThe operators behind the banking Trojan SharkBot are targeting...
Millones de dispositivos Android aún no tienen parches para fallas en la GPU de Mali
Millones de dispositivos Android aún no tienen parches para fallas en la GPU de MaliUn conjunto de cinco fallas de seguridad de gravedad media en el...
Dispositivos Dell, HP y Lenovo encontrados con versiones de OpenSSL obsoletas
Dispositivos Dell, HP y Lenovo encontrados con versiones de OpenSSL obsoletasUn análisis de imágenes de firmware en dispositivos de Dell, HP y Lenovo reveló la presencia...
Microsoft Azure launches DDoS IP protection for SMBs
Microsoft Azure launches DDoS IP protection for SMBsMicrosoft is extending the Azure DDoS Protection family with a new product focusing on small and medium-size businesses (SMBs)....
How to reset a Kerberos password and get ahead of coming updates
How to reset a Kerberos password and get ahead of coming updatesDo you recall when you last reset your Kerberos password? Hopefully that was not the...
Luna Moth Is Making Big Money on Callback Phishing Campaigns
Luna Moth Is Making Big Money on Callback Phishing CampaignsThreat actor Luna Moth is committed nowadays to targeting businesses with callback phishing campaigns, from which he...
Online retailers should prepare for a holiday season spike in bot-operated attacks
Online retailers should prepare for a holiday season spike in bot-operated attacksWith the holiday shopping season in full swing, retail websites can expect a spike in...
Google Ads Used to Distribute Royal Ransomware in Malvertising Campaign
Google Ads Used to Distribute Royal Ransomware in Malvertising CampaignMicrosoft Security Threat Intelligence research team warn about a threat actor identified as DEV-0569, which has been...
This Malware Installs Malicious Browser Extensions to Steal Users’ Passwords and Cryptos
This Malware Installs Malicious Browser Extensions to Steal Users' Passwords and CryptosA malicious extension for Chromium-based web browsers has been observed to be distributed via a...
Nighthawk Likely to Become Hackers’ New Post-Exploitation Tool After Cobalt Strike
Nighthawk Likely to Become Hackers' New Post-Exploitation Tool After Cobalt StrikeA nascent and legitimate penetration testing framework known as Nighthawk is likely to gain threat actors'...
UK finalizes first independent post-Brexit data transfer deal with South Korea
UK finalizes first independent post-Brexit data transfer deal with South KoreaThe UK has finalized its first independent data adequacy decision since leaving the European Union (EU)...
Meta Takes Down Fake Facebook and Instagram Accounts Linked to Pro-U.S. Influence Operation
Meta Takes Down Fake Facebook and Instagram Accounts Linked to Pro-U.S. Influence OperationMeta Platforms on Tuesday said it took down a network of accounts and pages...
Donut Extortion Group Targets Victims with Double-Extortion Ransomware Attacks
Donut Extortion Group Targets Victims with Double-Extortion Ransomware AttacksThe Donut extortion group has been confirmed by cybersecurity experts to deploy ransomware in double-extortion attacks on organizations....
Top Cyber Threats Facing E-Commerce Sites This Holiday Season
Top Cyber Threats Facing E-Commerce Sites This Holiday SeasonDelivering a superior customer experience is essential for any e-commerce business. For those companies, there's a lot at...
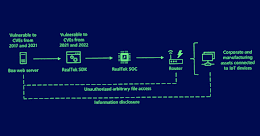
Hackers Exploiting Abandoned Boa Web Servers to Target Critical Industries
Hackers Exploiting Abandoned Boa Web Servers to Target Critical IndustriesMicrosoft on Tuesday disclosed the intrusion activity aimed at Indian power grid entities earlier this year likely...
34 Russian Cybercrime Groups Stole Over 50 Million Passwords with Stealer Malware
34 Russian Cybercrime Groups Stole Over 50 Million Passwords with Stealer MalwareAs many as 34 Russian-speaking gangs distributing information-stealing malware under the stealer-as-a-service model stole no...
Ducktail Malware Operation Evolves with New Malicious Capabilities
Ducktail Malware Operation Evolves with New Malicious CapabilitiesThe operators of the Ducktail information stealer have demonstrated a "relentless willingness to persist" and continued to update their...
Black Basta Ransomware Gang Actively Infiltrating U.S. Companies with Qakbot Malware
Black Basta Ransomware Gang Actively Infiltrating U.S. Companies with Qakbot MalwareCompanies based in the U.S. have been at the receiving end of an "aggressive" Qakbot malware...
The Biden administration has racked up a host of cybersecurity accomplishments
The Biden administration has racked up a host of cybersecurity accomplishmentsWhen it comes to hitting the ground running on cybersecurity, the Biden administration has engaged in...
This Android File Manager App Infected Thousands of Devices with SharkBot Malware
This Android File Manager App Infected Thousands of Devices with SharkBot MalwareThe Android banking fraud malware known as SharkBot has reared its head once again on...