Rackspace warns of phishing risks following ransomware attackCloud computing provider Rackspace warned customers on Thursday of increased risks of phishing attacks following a ransomware attack affecting...
Australia arrests ‘Pig Butchering’ suspects for stealing $100 million
Australia arrests 'Pig Butchering' suspects for stealing $100 millionThe Australian Federal Police (AFP) have arrested four suspected members of a financial investment scam syndicate estimated to...
Hackers earn $989,750 for 63 zero-days exploited at Pwn2Own Toronto
Hackers earn $989,750 for 63 zero-days exploited at Pwn2Own TorontoPwn2Own Toronto 2022 has ended with competitors earning $989,750 for 63 zero-day exploits (and multiple bug collisions) targeting...
The Week in Ransomware – December 9th 2022 – Wide Impact
The Week in Ransomware - December 9th 2022 - Wide ImpactThis week has been filled with research reports and news of significant attacks having a wide...
Clop ransomware uses TrueBot malware for access to networks
Clop ransomware uses TrueBot malware for access to networksSecurity researchers have noticed a spike in devices infected with the TrueBot malware downloader created by a Russian-speaking...
7 step checklist to avoid common cloud security misconfigurations
7 step checklist to avoid common cloud security misconfigurationsEXECUTIVE SUMMARY: Cloud computing provides a flexible and cost-effective way to access almost limitless compute power and data...
Microsoft adds screen recording to Windows 11 Snipping Tool
Microsoft adds screen recording to Windows 11 Snipping ToolMicrosoft is adding a built-in screen recorder to the Windows 11 Snipping Tool that will enable users to...
Air-gapped PCs vulnerable to data theft via power supply radiation
Air-gapped PCs vulnerable to data theft via power supply radiationA new attack method named COVID-bit uses electromagnetic waves to transmit data from air-gapped systems isolated from...
Cloudflare’s Zero Trust suite now available for free to at-risk groups
Cloudflare's Zero Trust suite now available for free to at-risk groupsCloudflare has made its 'Cloudflare One Zero Trust' security suite free to public interest groups, election...
Twitter confirms recent user data leak is from 2021 breach
Twitter confirms recent user data leak is from 2021 breachTwitter confirmed today that the recent leak of millions of members' profiles, including private phone numbers and...
Uber suffers new data breach after attack on vendor, info leaked online
Uber suffers new data breach after attack on vendor, info leaked onlineUber has suffered a new data breach after a threat actor leaked employee email addresses,...
Fortinet says SSL-VPN pre-auth RCE bug is exploited in attacks
Fortinet says SSL-VPN pre-auth RCE bug is exploited in attacksFortinet urges customers to patch their appliances against an actively exploited FortiOS SSL-VPN vulnerability that could allow unauthenticated...
Cyberattacks, ransomware incidents expected to rise in 2023
Cyberattacks, ransomware incidents expected to rise in 2023Contenido de la entradaLeer másProofpoint News Feed
Top AWS cloud security tips to secure your environment
Top AWS cloud security tips to secure your environmentEXECUTIVE SUMMARY: Remember when CodeSpaces was forced out of business within 12 hours after attackers compromised their AWS...
New Python malware backdoors VMware ESXi servers for remote access
New Python malware backdoors VMware ESXi servers for remote accessA previously undocumented Python backdoor targeting VMware ESXi servers has been spotted, enabling hackers to execute commands...
How to boost healthcare cyber security in 2023
How to boost healthcare cyber security in 2023Contributed by George Mack, Content Marketing Manager, Check Point Software. Hackers have made healthcare a top target. As a...
Q&A with Lucia Milică, vice president and global resident CISO at Proofpoint
Q&A with Lucia Milică, vice president and global resident CISO at ProofpointContenido de la entradaLeer másProofpoint News Feed
25+ cyber security experts, driving the security conversation…
25+ cyber security experts, driving the security conversation…EXECUTIVE SUMMARY: In cyber security, change is always coming. The question is, are you ready? This year, CyberTalk.org asked...
Systemic Risk Threatens Every Organization
Systemic Risk Threatens Every OrganizationContenido de la entradaLeer másProofpoint News Feed
Perspectives from the field: Optimizing your cloud security
Perspectives from the field: Optimizing your cloud securityKonstantina Koukou is a well-rounded, tech-savvy electrical engineering graduate with a specialization in Information and Telecommunication Systems and has...
Proofpoint Signs Definitive Agreement to Acquire Illusive
Proofpoint Signs Definitive Agreement to Acquire IllusiveContenido de la entradaLeer másProofpoint News Feed
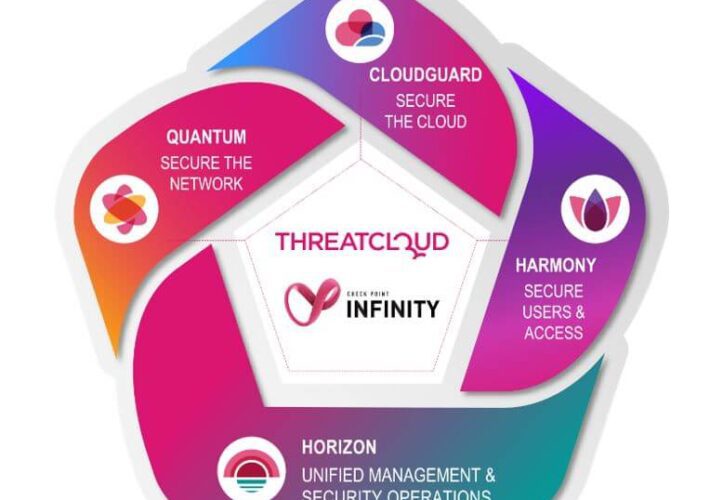
Is cloud native security good enough?
Is cloud native security good enough?By Deryck Mitchelson, Field CISO EMEA, Check Point Software Technologies. Global organizations are digitally transforming via cloud native applications and services....
Artificial intelligence driving high-performance cloud security transformations
Artificial intelligence driving high-performance cloud security transformationsEXECUTIVE SUMMARY: Migrating to the cloud can afford organizations a broad range of new opportunities and can confer numerous business...
K24359631: Intel BIOS firmware vulnerability CVE-2022-21198
K24359631: Intel BIOS firmware vulnerability CVE-2022-21198Intel BIOS firmware vulnerability CVE-2022-21198 Security Advisory Security Advisory Description Time-of-check time-of-use race condition in the BIOS firmware for some Intel(R)...
MY TAKE: The role of semiconductors in bringing the ‘Internet of Everything’ into full fruition
MY TAKE: The role of semiconductors in bringing the ‘Internet of Everything’ into full fruitionThe Internet of Everything (IoE) is on the near horizon. Related: Raising...
GUEST ESSAY: Here’s how and why ‘trust’ presents an existential threat to cybersecurity
GUEST ESSAY: Here’s how and why ‘trust’ presents an existential threat to cybersecurityOver the years, bad actors have started getting more creative with their methods of...
Previewing Black Hat Europe 2022 in London: 12 Hot Sessions
Previewing Black Hat Europe 2022 in London: 12 Hot SessionsCollective DDoS Defense, Rethinking Internet Defense, Zero-Day Harvesting and MoreBlack Hat Europe returns to London, offering deep...
Apple announces new security and privacy measures amid surge in cyber-attacks
Apple announces new security and privacy measures amid surge in cyber-attacksEncryption of iCloud storage means the information will be safeguarded from hackers as well as government...
Clare O’Neil warns counter-terror laws may need to change to better handle rightwing extremism
Clare O’Neil warns counter-terror laws may need to change to better handle rightwing extremismHome affairs minister says government preparing program to counter foreign interference and youth...
A Plan to Address Future Healthcare Cyber Challenges
A Plan to Address Future Healthcare Cyber ChallengesThe Health Sector Coordinating Council is embarking on a five-year strategic plan to help the healthcare and public health...