Royal Ransomware Targets US HealthcareRequested ransom payment demands ranged from $250,000 to over $2mLeer másRequested ransom payment demands ranged from $250,000 to over $2m
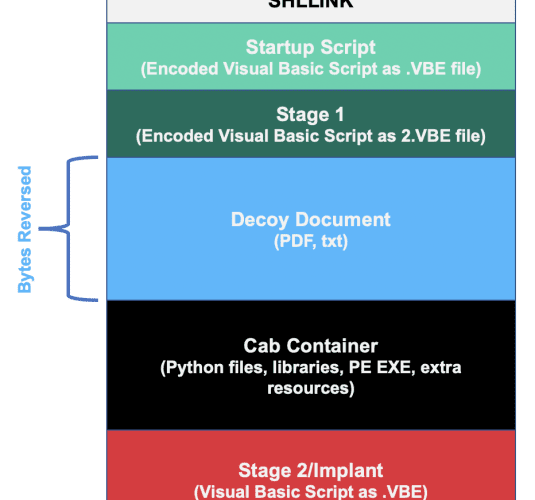
Evilnum group targets legal entities with a new Janicab variant
Evilnum group targets legal entities with a new Janicab variantA hack-for-hire group dubbed Evilnum is targeting travel and financial entities with the new Janicab malware variant. Kaspersky...
Transitive Dependencies Account for 95% of Bugs
Transitive Dependencies Account for 95% of BugsEndor Labs warns of dangerous complexities in open sourceLeer másEndor Labs warns of dangerous complexities in open source
HSE Cyber-Attack Costs Ireland $83m So Far
HSE Cyber-Attack Costs Ireland $83m So FarA total of roughly 100,000 people had their personal data stolen during the cyber-attackLeer másA total of roughly 100,000 people...
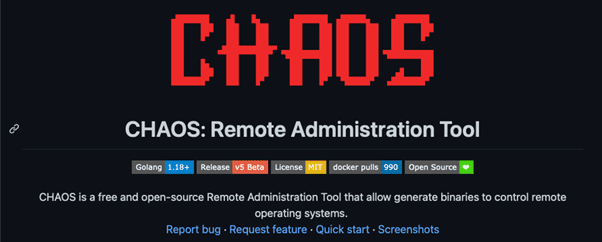
Cryptomining campaign targets Linux systems with Go-based CHAOS Malware
Cryptomining campaign targets Linux systems with Go-based CHAOS MalwareResearchers spotted a cryptocurrency mining campaign targeting Linux users with Go-based CHAOS malware (Trojan.Linux.CHAOSRAT). In November 2022, Trend...
Chaos RAT Used to Enhance Linux Cryptomining Attacks
Chaos RAT Used to Enhance Linux Cryptomining AttacksThe main downloader script and further payloads were hosted in different locationsLeer másThe main downloader script and further payloads...
Diamond Industry Attacked by Iranian Hackers with Data-Wiping Malware
Diamond Industry Attacked by Iranian Hackers with Data-Wiping MalwareA series of data wiper assaults targeting the diamond industry in South Africa, Israel, and Hong Kong have...
Zero Standing Privileges (ZSP) for Organizations: Less Privileges, More Security
Zero Standing Privileges (ZSP) for Organizations: Less Privileges, More SecurityIn complex environments, the need for privilege solutions has grown. Typically, companies with network infrastructure or critical...
Educational Institutions, the Favorite Targets of Vice Society Ransomware in 2022
Educational Institutions, the Favorite Targets of Vice Society Ransomware in 2022Vice Society ransomware seemed to favor educational institutions in their attacks in 2022. The Cybercrime group...
CommonSpirit Health Breached, Over 623,000 Patients’ Data Exposed
CommonSpirit Health Breached, Over 623,000 Patients’ Data ExposedFollowing an October ransomware attack, CommonSpirit Health confirmed that malicious actors accessed the personal information of 623,774 patients. This...
Fortinet urges customers to fix actively exploited FortiOS SSL-VPN bug
Fortinet urges customers to fix actively exploited FortiOS SSL-VPN bugFortinet fixed an actively exploited FortiOS SSL-VPN flaw that could allow a remote, unauthenticated attacker to execute arbitrary code...
What Is DNS Propagation and How to Keep Safe from DNS Attacks
What Is DNS Propagation and How to Keep Safe from DNS AttacksChanging your website’s hosting is the closest you’ll ever get to magic in cybersecurity. It’s...
Security Requirements as an Engineering Challenge
Security Requirements as an Engineering ChallengeBy Milica D. Djekic Independent researcher, Subotica, The Republic of Serbia Abstract Engineering challenges have appeared throughout time […] The post...
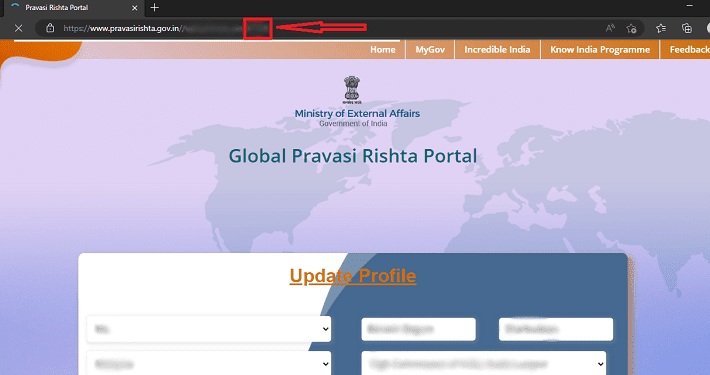
Indian foreign ministry’s Global Pravasi Rishta portal leaks expat passport details
Indian foreign ministry’s Global Pravasi Rishta portal leaks expat passport detailsThe Cybernews research team reported that India’s government platform Global Pravasi Rishta Portal was leaking sensitive...
AI for Cyber Threat Intelligence – Challenges and Mitigation Approaches
AI for Cyber Threat Intelligence – Challenges and Mitigation ApproachesBy Uday Kiran Pulleti, Senior Director – AI, Cyble The internet as we know it is a...
MuddyWater Threat Group Behind Email Phishing Attacks
MuddyWater Threat Group Behind Email Phishing AttacksA malicious group associated to Iran’s Ministry of Intelligence and Security (MOIS), MuddyWater, was reported responsible for delivering phishing messages...
Typosquatting Explained: Definition, Threats, and Safety Tips
Typosquatting Explained: Definition, Threats, and Safety TipsCybercriminals pray on our online mistakes, learning how to transform them into money better and faster. And one of the...
Clop Ransomware Uses Viral ‘Truebot’ Malware to Access Networks
Clop Ransomware Uses Viral ‘Truebot’ Malware to Access NetworksSecurity researchers recently noticed a surge in new devices infected with the Truebot malware downloader. This is created...
SMB Cyber Insurance: The End of Innocence
SMB Cyber Insurance: The End of InnocenceBy Nadav Arbel, Co-Founder & CEO, CYREBRO The cyber insurance landscape has changed dramatically in recent years – […] The...
Ransomware 101: What Is Targeted Ransomware and How Does It Work
Ransomware 101: What Is Targeted Ransomware and How Does It WorkTo understand what targeted ransomware is and to know the difference between opportunistic and targeted ransomware,...
Cloud Patch Management Explained: What Is It and Why Is It Important?
Cloud Patch Management Explained: What Is It and Why Is It Important?Cloud patch management is one of the most important and often overlooked, aspects of cloud...
Unpatched Vulnerabilities Cause Pulse Connect Secure Hosts to Be at Risk
Unpatched Vulnerabilities Cause Pulse Connect Secure Hosts to Be at RiskResearchers have found more than 4,000 vulnerable Pulse Connect Secure hosts being exposed to the internet....
Data Breach Gives Threat Actors Complete Information about Vevor Clients
Data Breach Gives Threat Actors Complete Information about Vevor ClientsA multi-terabyte database belonging to Vevor was left open to the public this year starting July 12th...
Rackspace Warns Clients About Phishing Risks After Suffering a Ransomware Attack
Rackspace Warns Clients About Phishing Risks After Suffering a Ransomware AttackFollowing a ransomware attack that affected its hosted Microsoft Exchange environment, cloud computing firm Rackspace issued...
The Art and Science of Building a Cyber Security Tech Stack
The Art and Science of Building a Cyber Security Tech StackHow companies should approach assessing risk and vulnerabilities and build cybersecurity tech stacks that address their...
COVID-bit: A New Attack Method That Can Breach Air-gapped PCs
COVID-bit: A New Attack Method That Can Breach Air-gapped PCsCOVID-bit is a new assault strategy that uses electromagnetic waves to breach air-gapped computers, and it has...
The Data Problem
The Data ProblemToday, data is essential to companies’ success, yet, at the same time, it is incumbent on them to […] The post The Data Problem...
Man Arrested for Hacking NY Hair Salon’s POS Provider and Stealing $400K
Man Arrested for Hacking NY Hair Salon’s POS Provider and Stealing $400KA man from Arizona was detained and charged for hacking into a hair salon chain...
The Remote Workforce is Here to Stay
The Remote Workforce is Here to StayHow this Impacts Security By Metin Kortak, Chief Information Security Officer, Rhymetec As the post-pandemic business recovery continues, […] The...
AppleJeus Malware Detection: North Korea-Linked Lazarus APT Spreads Malicious Strains Masquerading as Cryptocurrency Apps
AppleJeus Malware Detection: North Korea-Linked Lazarus APT Spreads Malicious Strains Masquerading as Cryptocurrency Apps A notorious North Korea-backed APT group, Lazarus, continuously broadens its attack surface,...