6 Examples of the Evolution of a Scam SiteExamining some key examples of recently found fraud sites that target the lucrative retail shoe industry helps us...
Cyberattack on Fintech Firm Disrupts Derivatives Trading Globally
Cyberattack on Fintech Firm Disrupts Derivatives Trading GloballyThe Russia-linked LockBit ransomware group claims to be behind the attack that fouled automated transactions for dozens of clients...
Korelock Launches IOT Smart Lock Technology Company
Korelock Launches IOT Smart Lock Technology CompanyDenver-based business secures Series A Funding through partnerships with Iron Gate Capital and Kozo Keikaku Engineering.Read MoreDark ReadingDenver-based business secures...
Hornetsecurity Combats QR Code Phishing With Launch of New Technology
Hornetsecurity Combats QR Code Phishing With Launch of New TechnologyPost ContentRead MoreDark Reading
MITRE Releases Tool to Design Cyber-Resilient Systems
MITRE Releases Tool to Design Cyber-Resilient SystemsEngineers can use the Cyber Resiliency Engineering Framework Navigator to visuzalize their cyber-resiliency capabilities.Read MoreDark ReadingEngineers can use the Cyber...
How the Cloud Is Shifting CISO Priorities
How the Cloud Is Shifting CISO PrioritiesThe greatly expanding attack surface created by the cloud needs to be protected.Read MoreDark ReadingThe greatly expanding attack surface created...
Scores of Redis Servers Infested by Sophisticated Custom-Built Malware
Scores of Redis Servers Infested by Sophisticated Custom-Built MalwareAt least 1,200 Redis servers worldwide have been infected with "HeadCrab" cryptominers since 2021.Read MoreDark ReadingAt least 1,200...
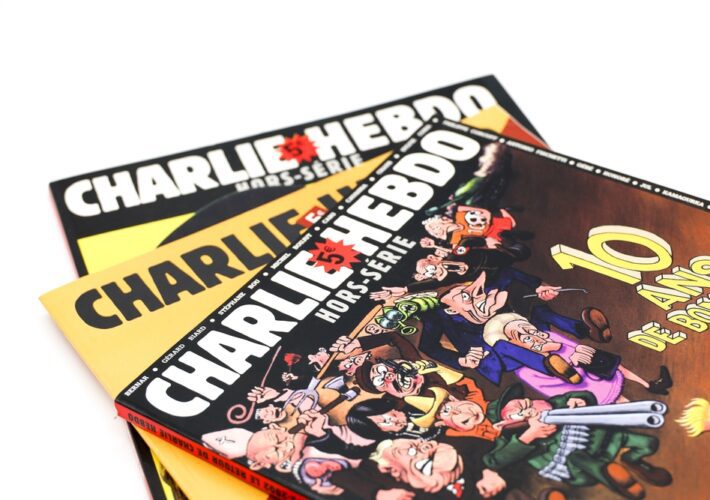
Iran-Backed Actor Behind ‘Holy Souls’ Cyberattack on Charlie Hebdo, Microsoft Says
Iran-Backed Actor Behind 'Holy Souls' Cyberattack on Charlie Hebdo, Microsoft SaysThe January attack was in retaliation for the satirical French magazine's decision to launch a cartoon...
What CISOs Can Do About Brand Impersonation Scam Sites
What CISOs Can Do About Brand Impersonation Scam SitesApply these nine tips to proactively fight fraudulent websites that use your brand to rip people off.Read MoreDark...
Name That Edge Toon: For the Birds
Name That Edge Toon: For the BirdsCome up with a clever caption, and our panel of experts will reward the winner with a $25 Amazon gift...
How Cybercriminals Are Operationalizing Money Laundering and What to Do About It
How Cybercriminals Are Operationalizing Money Laundering and What to Do About ItIt's time to share threat intelligence and prioritize digital literacy and cyber hygiene to stem...
Crypto’s Decentralized Finance Security Problem
Crypto's Decentralized Finance Security ProblemAuditing Itself Can;t Ensure SecurityHolding cryptocurrencies in anything but a memory drive inside a box shielded with a Faraday cage was seemingly...
Notorious Finnish Hacker ‘Zeekill’ Busted by French Police
Notorious Finnish Hacker 'Zeekill' Busted by French PoliceAleksanteri Kivimaki Charged With Mental Health Patient Data Breach and ExtortionFrench police arrested hacker Aleksanteri Kivimäki, 25, who's suspected...
Discussion: Mitigating Risks to Customer Account Integrity
Discussion: Mitigating Risks to Customer Account IntegrityTeleSign's Seth Gilpin on Fraud and Risk Management in Customer Account and Device Security.Digital transformation we all have experienced over...
Rising ‘Firebrick Ostrich’ BEC Group Launches Industrial-Scale Cyberattacks
Rising 'Firebrick Ostrich' BEC Group Launches Industrial-Scale CyberattacksThe group's wanton attacks demonstrate that business email compromise is everything a hacker can want in one package: low...
Rising ‘Firebrick Ostrich’ BEC Group Launches Industrial-Scale Cyberattacks
Rising 'Firebrick Ostrich' BEC Group Launches Industrial-Scale CyberattacksThe group's wanton attacks demonstrate that business email compromise is everything a hacker can want in one package: low...
Rising ‘Firebrick Ostrich’ BEC Group Launches Industrial-Scale Cyberattacks
Rising 'Firebrick Ostrich' BEC Group Launches Industrial-Scale CyberattacksThe group's wanton attacks demonstrate that business email compromise is everything a hacker can want in one package: low...
Massive Ransomware Campaign Targets VMware ESXi Servers
Massive Ransomware Campaign Targets VMware ESXi ServersVulnerability Patched in 2021 Still Haunts Admins at Over 300 OrganizationsA massive automated ransomware campaign is targeting VMware ESXi hypervisors...
Rising ‘Firebrick Ostrich’ BEC Group Launches Industrial-Scale Cyberattacks
Rising 'Firebrick Ostrich' BEC Group Launches Industrial-Scale CyberattacksThe group's wanton attacks demonstrate that business email compromise is everything a hacker can want in one package: low...
Rising ‘Firebrick Ostrich’ BEC Group Launches Industrial-Scale Cyberattacks
Rising 'Firebrick Ostrich' BEC Group Launches Industrial-Scale CyberattacksThe group's wanton attacks demonstrate that business email compromise is everything a hacker can want in one package: low...
Cyber Insurer Sees Remote Access, Cloud Databases Under Fire
Cyber Insurer Sees Remote Access, Cloud Databases Under FireReminder: Real-World Attacks Often Focus on Small Subset of Known VulnerabilitiesCriminals lately have been prioritizing two types of...
Indian Official Highlights Djvu Ransomware as Threat
Indian Official Highlights Djvu Ransomware as ThreatDjvu Camouflages Itself as Cracked SoftwareAn Indian cybersecurity official highlighted Djvu ransomware as a threat, saying that "maximum companies" are...
IBM Security GM on Seeing a Target Through the Hacker’s Eyes
IBM Security GM on Seeing a Target Through the Hacker's EyesMary O'Brien on How External Attack Surface Management Finds Internet-Facing IssuesCompanies can be blinded by their...
Hackers Posing as Ukrainian Ministry Deploy Info Stealers
Hackers Posing as Ukrainian Ministry Deploy Info StealersSpoofed Polish Police Websites Also FoundUkrainian and Polish cyber defenders are warning against a slew of phishing websites that...
¿Es segura tu estación de carga EV? Nuevas vulnerabilidades de seguridad descubiertas
¿Es segura tu estación de carga EV? Nuevas vulnerabilidades de seguridad descubiertasDos nuevas debilidades de seguridad descubiertas en varios sistemas de carga de vehículos eléctricos (EV)...
CrowdStrike CEO on Why It’s Tough to Defend Sensitive Assets
CrowdStrike CEO on Why It's Tough to Defend Sensitive AssetsGeorge Kurtz on How Reposify Helps Customers Locate and Safeguard Priority AssetsOrganizations today struggle with both new...
Nuevas vulnerabilidades de alta gravedad descubiertas en los productos Cisco IOx y F5 BIG-IP
Nuevas vulnerabilidades de alta gravedad descubiertas en los productos Cisco IOx y F5 BIG-IPF5 advirtió sobre una falla de alta gravedad que afecta a los dispositivos...
Rising ‘Firebrick Ostrich’ BEC Group Launches Industrial-Scale Cyberattacks
Rising 'Firebrick Ostrich' BEC Group Launches Industrial-Scale CyberattacksThe group's wanton attacks demonstrate that business email compromise is everything a hacker can want in one package: low...
Webinar | 6 Ways to Cut Costs with a Zero Trust Architecture
Webinar | 6 Ways to Cut Costs with a Zero Trust ArchitecturePost ContentRead MoreDataBreachToday.com RSS Syndication
ISMG Editors: Does US Takedown Mark Hive Group’s Demise?
ISMG Editors: Does US Takedown Mark Hive Group's Demise?Also: Russian DDoS Attacks Target US Hospitals; Data Breach Reports Lack DetailsIn the latest weekly update, ISMG editors...