Source: securityaffairs.com – Author: Pierluigi Paganini Apple fixed a vulnerability discovered by Microsoft researchers that lets attackers with root privileges bypass System Integrity Protection (SIP). Researchers...
Author:
PyPI enforces 2FA authentication to prevent maintainers’ account takeover – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini PyPI is going to enforce two-factor authentication (2FA) for all project maintainers by the end of this year over security...
A database containing 478,000 RaidForums members leaked online – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The database of the popular RaidForums hacking forum has been leaked on a new hacking forum, 478,000 members exposed. A...
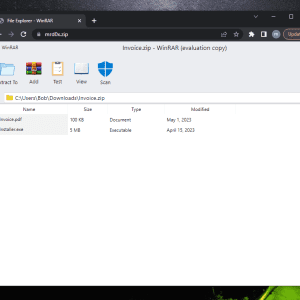
Beware of the new phishing technique “file archiver in the browser” that exploits zip domains – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini “file archiver in the browser” is a new phishing technique that can be exploited by phishers when victims visit a...
BrutePrint Attack allows to unlock smartphones with brute-forcing fingerprint – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Researchers devised an attack technique, dubbed BrutePrint Attack, that allows brute-forcing fingerprints on smartphones to bypass authentication. Researchers have devised...
Lockbit ransomware attack on MCNA Dental impacts 8.9M individuals – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Managed Care of North America (MCNA) Dental disclosed a data breach that impacted more than 8.9 million individuals. Managed Care...
New Go-written GobRAT RAT targets Linux Routers in Japan – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A new Golang remote access trojan (RAT), tracked as GobRAT, is targeting Linux routers in Japan, the JPCERT Coordination Center warns....
Researchers analyzed the PREDATOR spyware and its loader Alien – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Cisco Talos and the Citizen Lab researchers have published a technical analysis of the powerful Android spyware Predator. Security researchers...
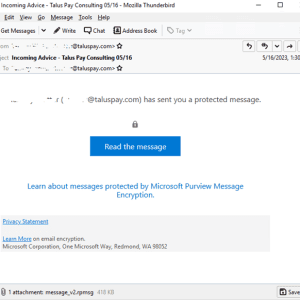
Attackers use encrypted RPMSG messages in Microsoft 365 targeted phishing attacks – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Experts warn of phishing attacks that are combining the use of compromised Microsoft 365 accounts and .rpmsg encrypted emails. Trustwave...
Industrial automation giant ABB disclosed data breach after ransomware attack – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Swiss electrification and automation technology giant ABB confirmed it has suffered a data breach after a ransomware attack. ABB has...
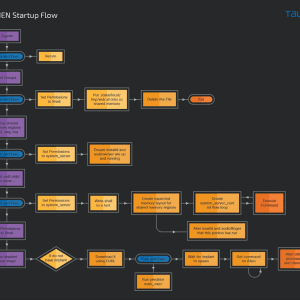
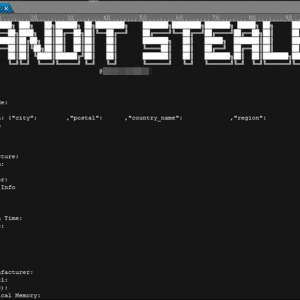
New Bandit Stealer targets web browsers and cryptocurrency wallets – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Bandit Stealer is a new stealthy information stealer malware that targets numerous web browsers and cryptocurrency wallets. Trend Micro researchers...
CISA adds recently patched Barracuda zero-day to its Known Exploited Vulnerabilities catalog – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini US CISA added recently patched Barracuda zero-day vulnerability to its Known Exploited Vulnerabilities catalog. US Cybersecurity and Infrastructure Security Agency...
Security Affairs newsletter Round 421 by Pierluigi Paganini – International edition – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Privacy Overview This website uses cookies to improve your experience while you navigate through the website. Out of these cookies,...
Is the BlackByte ransomware gang behind the City of Augusta attack? – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The city of Augusta in Georgia, U.S., admitted that the recent IT system outage was caused by a cyber attack. While...
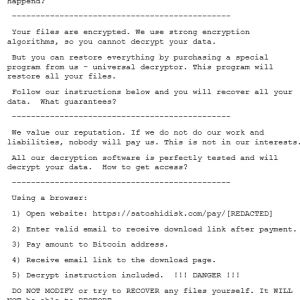
New Buhti ransomware operation uses rebranded LockBit and Babuk payloads – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The recently identified Buhti operation targets organizations worldwide with rebranded LockBit and Babuk ransomware variants. Researchers from Symantec discovered a...
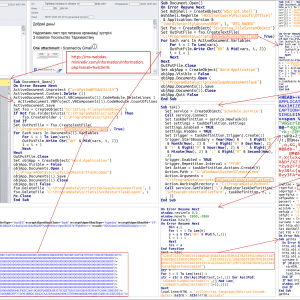
New PowerExchange Backdoor linked to an Iranian APT group – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini An alleged Iran-linked APT group targeted an organization linked to the United Arab Emirates (U.A.E.) with the new PowerExchange backdoor....
Dark Frost Botnet targets the gaming sector with powerful DDoS – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Researchers spotted a new botnet dubbed Dark Frost that is used to launch distributed denial-of-service (DDoS) attacks against the gaming industry. Researchers...
New CosmicEnergy ICS malware threatens energy grid assets – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Experts detailed a new piece of malware, named CosmicEnergy, that is linked to Russia and targets industrial control systems (ICS). Researchers...
D-Link fixes two critical flaws in D-View 8 network management suite – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini D-Link fixed two critical flaws in its D-View 8 network management suite that could lead to authentication bypass and arbitrary...
Zyxel firewall and VPN devices affected by critical flaws – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Zyxel fixed two critical flaws in multiple firewall and VPN products that can lead to remote code execution or cause a...
China-linked APT Volt Typhoon targets critical infrastructure organizations – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A China-linked APT group, tracked as Volt Typhoon, breached critical infrastructure organizations in the U.S. and Guam without being detected....
North Korea-linked Lazarus APT targets Microsoft IIS servers to deploy malware – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini North Korea-linked APT group Lazarus actor has been targeting vulnerable Microsoft IIS servers to deploy malware. AhnLab Security Emergency response...
Iran-linked Tortoiseshell APT behind watering hole attacks on shipping and logistics Israeli websites – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Iran-linked threat actor Tortoiseshell targeted shipping, logistics, and financial services companies in Israel with watering hole attacks. ClearSky Cyber Security...
Barracuda Email Security Gateway (ESG) hacked via zero-day bug – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Barracuda warned customers that some of its Email Security Gateway (ESG) appliances were breached exploiting a zero-day vulnerability. Network security...
The US government sanctioned four entities and one individual for supporting cyber operations conducted by North Korea – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The US Department of the Treasury sanctioned four entities and one individual for their role in cyber operations conducted by...
Ukraine’s CERT-UA warns of espionage activity conducted by UAC-0063 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The Computer Emergency Response Team of Ukraine (CERT-UA) warns of a cyberespionage campaign targeting state bodies in the country. The...
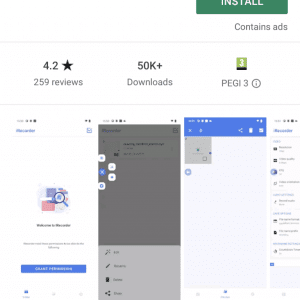
AhRat Android RAT was concealed in iRecorder app in Google Play – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini ESET found a new remote access trojan (RAT), dubbed AhRat, on the Google Play Store that was concealed in an...
The previously undocumented GoldenJackal APT targets Middle East, South Asia entities – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A previously undocumented APT group tracked as GoldenJackal has been targeting government and diplomatic entities in the Middle East and...
Google announced its Mobile VRP (vulnerability rewards program) – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Google introduced Mobile VRP (vulnerability rewards program), a new bug bounty program for reporting vulnerabilities in its mobile applications. Google...
German arms manufacturer Rheinmetall suffered Black Basta ransomware attack – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The German automotive and arms manufacturer Rheinmetall announced it was victim of a Black Basta ransomware attack that took place last month. Rheinmetall...