Travellers are being told to be wary when plugging their smartphones and laptops into USB chargers. On Thursday last week, the official Twitter account of the...
Author:
Ukrainian hackers spend $25,000 of pro-Russian blogger’s money on sex toys
Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s. View all...
A fireside chat with four CISOs about how they secure their cybersecurity firms from attack
On Tuesday 11 April, I’ll be joined by the CISOs of security firms Wiz, Rubrik, Noname, and Abnormal, for a friendly chat about how they protect...
Own a Nexx “smart” alarm or garage door opener? Get rid of it, or regret it
Nexx is a manufacturer of “smart” devices – plus, alarms, garage door openers, that kind of thing. Unfortunately their response to vulnerabilities is not-so-smart. According to...
Smashing Security podcast #316: Of Musk and Afroman
An Elon Musk-worshipping college principal gets schooled, and rapper Afroman turns the tables after armed police raid his house. All this and much more is discussed...
That ticking noise is your end users’ laptops
Graham Cluley Security News is sponsored this week by the folks at Kolide. Thanks to the great team there for their support! Here’s an uncomfortable fact:...
The hidden danger to zero trust: Excessive cloud permissions
Graham Cluley Security News is sponsored this week by the folks at Sysdig. Thanks to the great team there for their support! What is one of...
aCropalypse now! Cropped and redacted images suffer privacy fail on Google Pixel smartphones
Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s. View all...
Free decryptor released for Conti-based ransomware following data leak
Security researchers have released a new decryption tool that should come to the rescue of some victims of a modified version of the Conti ransomware, helping...
Android phones can be hacked just by someone knowing your phone number
Well, this isn’t good. Google has issued a warning that some Android phones can be hacked remotely, without the intended victim having to click on anything....
Smashing Security podcast #313: Tesla twins and deepfake dramas
The twisted tale of the two Teslas, and a deepfake sandwich. All this and more is discussed in the latest edition of the “Smashing Security” podcast...
Microsoft has another go at closing security hole exploited by Magniber ransomware
Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s. View all...
Software supply chain attacks are on the rise — are you at risk?
Graham Cluley Security News is sponsored this week by the folks at Sysdig. Thanks to the great team there for their support! Attacks targeting the software...
STALKER 2 hacker demands Ukrainian game developer reinstates Russian language support, or else…
“STALKER 2: Heart of Chornobyl” is an action-packed video game for Windows, which sees players pitted against violent mutants and greedy thugs against a backdrop of...
FBI reveals that more money is lost to investment fraud than ransomware and business email compromise combined
Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s. View all...
WhatsApp and UK government on collision course, as app vows not to remove end-to-end encryption
Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s. View all...
Hack the Pentagon website promotes the benefits of bug bounties to US Military
Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s. View all...
Clipboard-injecting malware disguises itself as Tor browser, steals cryptocurrency
Imagine you live in Russia and want to use the Tor browser to anonymise your browsing of the web. There’s a problem. Many people in Russia...
US sends million-dollar scammer to prison for four years
Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s. View all...
Smashing Security podcast #315: Crypto hacker hijinks, government spyware, and Utah social media shocker
A cryptocurrency hack leads us down a maze of twisty little passages, Joe Biden’s commercial spyware bill, and Utah gets tough on social media sites. All...
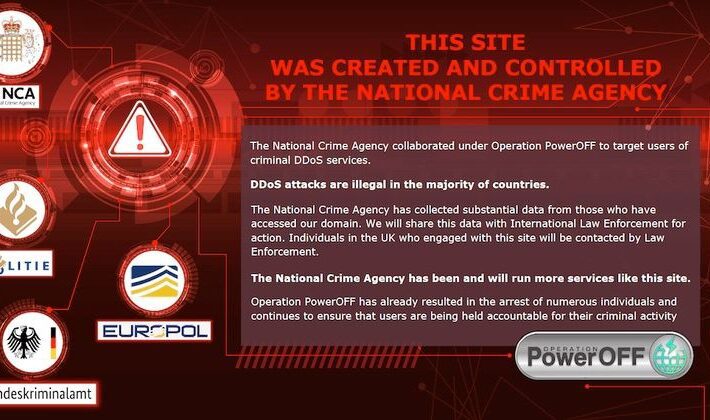
UK police reveal they are running fake DDoS-for-hire sites to collect details on cybercriminals
Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s. View all...
Can zero trust be saved?
Graham Cluley Security News is sponsored this week by the folks at Kolide. Thanks to the great team there for their support! Right now, “Zero Trust”...
Danger USB! Journalists sent exploding flash drives
Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s. View all...
Europe’s transport sector terrorised by ransomware, data theft, and denial-of-service attacks
A new report from ENISA, the European Union Agency for Cybersecurity, looking at cyberattacks targeting the European transport network over a period of almost two years,...
Fake GPT Chrome extension steals Facebook session cookies, breaks into accounts
The world has gone ChatGPT bonkers. Just about everyone is talking about it, and if you’re not talking about it then that’s because you’re too busy...
Smashing Security podcast #314: Photo cropping bombshell, TikTok debates, and real estate scams
It could be a case of aCropalypse now for Google Pixel users, there’s a warning for house buyers, and just why is TikTok being singled out...
Hack the Pentagon website promotes the benefits of bug bounties to US Military
Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s. View all...