The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Author: Constanza Rodriguez
Best Cybersecurity Certifications online
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Azure DevOps Security Guide
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Awesome Bugbounty Writeups
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Awesome SOC
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Awesome Azure Penetration Testing
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Defending Azure Active Directory
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
WEEKLYCYBER SECURITY BRIEFING
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Application Container Security Guide
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
API Security Checklist
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
API Security: Threats, Best Practices,Challenges, and Way forward usingAI
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Antes, durantey después de ira la NubeRespuesta ante Incidentes
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Ransomware Hostage Rescue Manual
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Anonymous Logins for Pentesters
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
An Introduction to Information Security
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
ISO/IEC 27701Privacy Information Management – Your implementation guide
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Futureof FirewallsIs Software – Rethink Your Firewalls to Meet the Needs of Digital Transformation
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Network Segmentationand Microsegmentationin Modern EnterpriseEnvironments
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
5 Steps to Ransomware Defense – How to strengthen your defenses beyond the perimeter
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
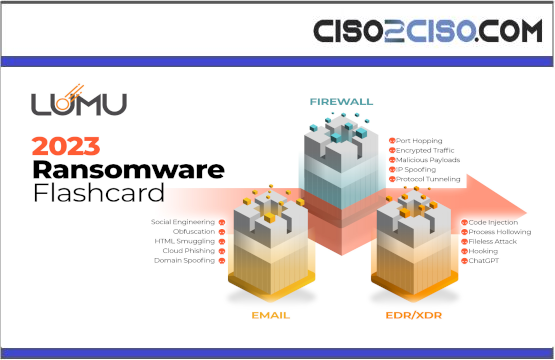
2023 Ransomware Flashcard Analysis and Overview
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Q2-2023Ransomware Report
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Ransomware Hostage Rescue Manual
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Ransomware Investigation osint and hunting Overview PT1
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
ISACA Ransomware Incident Response -23
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Detecting and Responding to Ransomware
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Stop Ransomware Guide May 2023
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A Review Ransomware Intrusion
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Splunk Queries for SOC Analyst
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
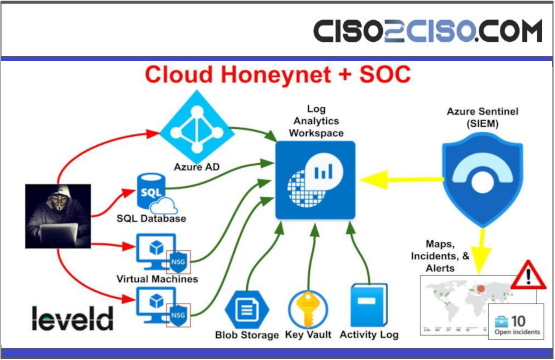
Building a SOC Honeynet in Azure
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Becoming a SOC analyst V1
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...