Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Government agencies and cybersecurity firms are on being more vigilant after the US Department of Health and...
Author: admin
CISA: ‘Whirlpool’ Backdoor Sends Barracuda ESG Security Down the Drain – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading The US Cybersecurity and Infrastructure Security Agency (CISA) this week issued yet another alert related to...
Dell Credentials Bug Opens VMWare Environments to Takeover – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Hardcoded credentials in the Dell Compellent storage array service could enable attackers to take over enterprise...
Cyber Insurance Experts Make a Case for Coverage, Protection – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading BLACK HAT USA – Las Vegas – Wednesday, Aug. 9 — Cybersecurity and insurance continued their awkward...
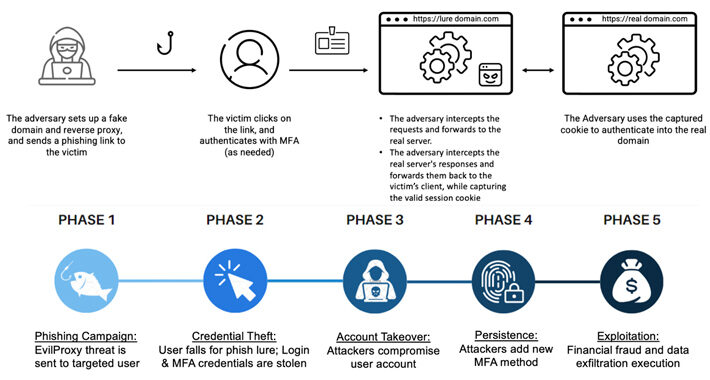
EvilProxy Cyberattack Flood Targets Execs via Microsoft 365 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Attackers have unleashed an EvilProxy phishing campaign to target thousands of Microsoft 365 user accounts worldwide, sending...
The Hard Realities of Setting AI Risk Policy – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ericka Chickowski, Contributing Writer, Dark Reading BLACK HAT USA – Las Vegas – Thursday, Aug. 10 – Here’s some good news for...
New Attack Alert: Freeze[.]rs Injector Weaponized for XWorm Malware Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 10, 2023THNMalware / Cyber Threat Malicious actors are using a legitimate Rust-based injector called Freeze[.]rs to deploy a commodity malware...
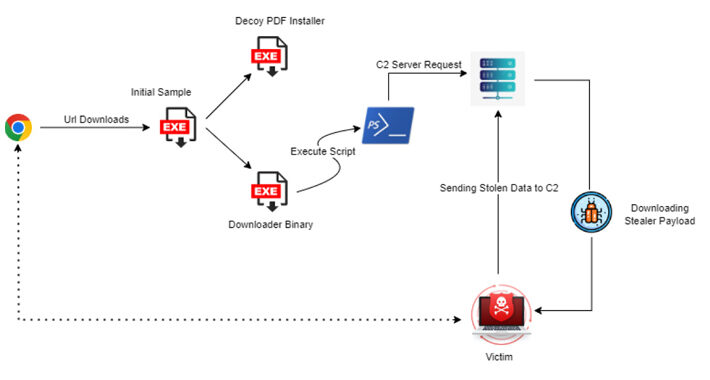
New Statc Stealer Malware Emerges: Your Sensitive Data at Risk – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 10, 2023THNMalware / Cyber Threat A new information malware strain called Statc Stealer has been found infecting devices running Microsoft...
Encryption Flaws in Popular Chinese Language App Put Users’ Typed Data at Risk – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 10, 2023THNPrivacy / Encryption A widely used Chinese language input app for Windows and Android has been found vulnerable to...
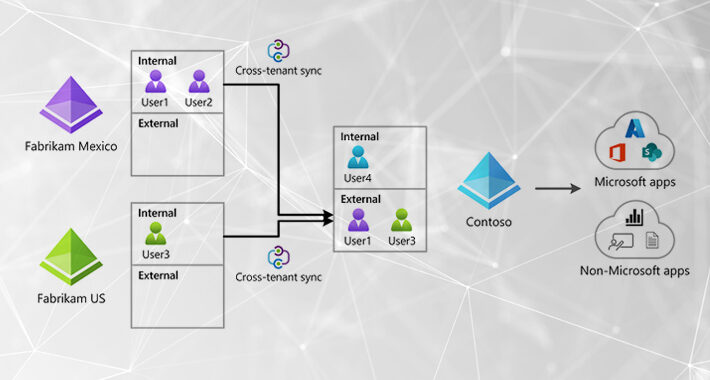
Emerging Attacker Exploit: Microsoft Cross-Tenant Synchronization – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 10, 2023The Hacker NewsThreat Detection / Attack Signal Attackers continue to target Microsoft identities to gain access to connected Microsoft...
Quick Glossary: Cybersecurity Attack Response and Mitigation – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Your computer network is under constant attack. The hard reality is that one of those cyberattacks will succeed, and you had better...
‘MoustachedBouncer’ APT Spies on Embassies, Likely via ISPs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading BLACK HAT USA – Las Vegas – Thursday, Aug. 10 — A Belarus-linked APT spied on...
DARPA Launches 2-Year Contest to Build AI Tools to Fix Vulnerabilities – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading BLACK HAT USA – Las Vegas – Wednesday, Aug. 9 — The Defense Advanced Research Projects...
Blockchain Signing Bug Cracks Open Crypto Investors’ Wallets Worldwide – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading BLACK HAT USA — Las Vegas – Wednesday, Aug. 9 Vulnerabilities in protocols used by major cryptocurrency...
Black Hat Opens With Call to Steer AI from Predictions to Policy – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading BLACK HAT USA – Las Vegas – Wednesday, Aug. 9 – A lot has changed, “but...
Windows Defender-Pretender Attack Dismantles Flagship Microsoft EDR – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading BLACK HAT USA – Las Vegas – Wednesday, Aug. 9: Among the 97 CVEs that Microsoft patched...
Disposed-of Gadgets Can Lead to Wi-Fi Network Hacks, Kaspersky Says – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading When disposing of old technology — such as old phones, computers, printers, and smartwatches — it’s essential...
Cybercriminals Increasingly Using EvilProxy Phishing Kit to Target Executives – Source:thehackernews.com
Source: thehackernews.com – Author: . Threat actors are increasingly using a phishing-as-a-service (PhaaS) toolkit dubbed EvilProxy to pull off account takeover attacks aimed at high-ranking executives...
Interpol Busts Phishing-as-a-Service Platform ’16Shop,’ Leading to 3 Arrests – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 10, 2023THNCyber Crime / Hacking Interpol has announced the takedown of a phishing-as-a-service (PhaaS) platform called 16Shop, in addition to...
Collide+Power, Downfall, and Inception: New Side-Channel Attacks Affecting Modern CPUs – Source:thehackernews.com
Source: thehackernews.com – Author: . Cybersecurity researchers have disclosed details of a trio of side-channel attacks that could be exploited to leak sensitive data from modern...
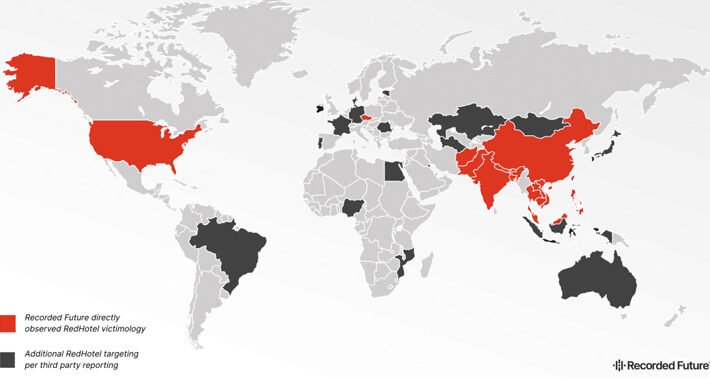
China-Linked Hackers Strike Worldwide: 17 Nations Hit in 3-Year Cyber Campaign – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 09, 2023THNCyber Espionage / Cyber Attacks Hackers associated with China’s Ministry of State Security (MSS) have been linked to attacks...
Continuous Security Validation with Penetration Testing as a Service (PTaaS) – Source:thehackernews.com
Source: thehackernews.com – Author: . Validate security continuously across your full stack with Pen Testing as a Service. In today’s modern security operations center (SOC), it’s...
EU General Data Protection Regulation Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: The EU General Data Protection Regulation is a comprehensive set of rules designed to keep the personal data of all EU citizens...
C-Suite Cybersecurity Sign-off Hinges on Customer Trust, Digital Opps – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading BLACK HAT USA – Las Vegas – Wednesday, Aug. 9 Security teams looking to justify more cyber...
OWASP Lead Flags Gaping Hole in Software Supply Chain Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading BLACK HAT USA – Las Vegas – Wednesday, Aug. 9 The founder and lead of the open-source OWASP‘s...
Sweet Security Debuts Runtime Management for Cloud – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Israeli cloud security startup Sweet Security has introduced its first product, Cloud Runtime Security Suite. Founded by...
Interpol Shuts Down African Cybercrime Group, Seizes $2 Million – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading A cross-border investigation into West African cybercriminal groups has resulted in 103 arrests and the seizure of...
RedHotel Checks in as Dominant China-Backed Cyberspy Group – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading An advanced persistent threat (APT) is pulling ahead in a crowded field of China state-sponsored actors as...
AI Risk Database Tackles AI Supply Chain Risks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ericka Chickowski, Contributing Writer, Dark Reading An emerging free tool that analyzes artificial intelligence (AI) models for risk has set a path...
Why Shellshock Remains a Cybersecurity Threat After 9 Years – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jeremy Ventura, Director, Security Strategy, Field CISO, @ThreatX The Shellshock vulnerability got a lot of attention when it was first disclosed in...







![new-attack-alert:-freeze[]rs-injector-weaponized-for-xworm-malware-attacks-–-source:thehackernews.com](https://ciso2ciso.com/wp-content/uploads/2023/08/73456/new-attack-alert-freezers-injector-weaponized-for-xworm-malware-attacks-sourcethehackernews-com-710x380.jpg)