Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading As operational technology (OT) gets more networked, these industrial networks are more prone to ransomware and supply...
Author: admin
Cribl, Exabeam Partner on Threat Detection, Investigation, and Response – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Abby Strong of Cribl and Chris Cesio of Exabeam talk about their companies’ recent partnership designed to...
Interpres: Getting the Most Out of Threat Intelligence Resources – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Nick Lantuh of Interpres talks about the shortcomings of the threat intel industry and how security pros...
Qualys Offers Threat Forecast For Cloud, and Tips For Reducing Cloud Risks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Sumedh Thakar of Qualys talks about how security vendors must translate cloud customer needs into effective solutions,...
Normalyze: How Focusing on Data Can Improve Cloud Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Normalyze’s Ravi Ithal deconstructs data security posture management (DPSM), how it differs from conventional data security management,...
White House Orders Federal Agencies to Bolster Cyber Safeguards – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The White House has ordered federal agencies to get their cybersecurity safeguards up to date as they...
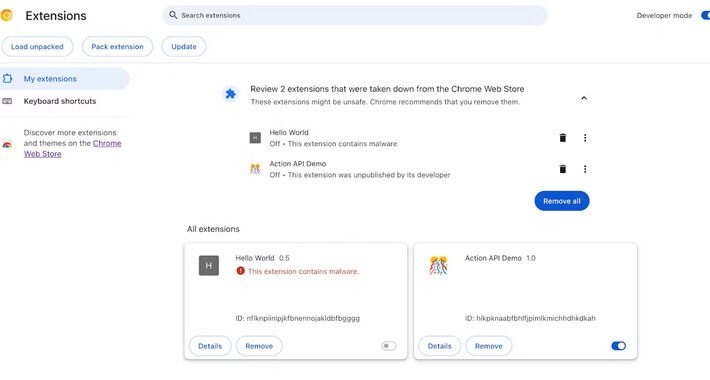
Google Chrome’s New Feature Alerts Users About Auto-Removal of Malicious Extensions – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 18, 2023THNBrowser Security / Malware Google has announced plans to add a new feature in the upcoming version of its...
WordPress Security Checklist – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Stories of virus and malware infections, data loss, system compromises and unauthorized access dominate headlines, and your WordPress website may be contributing...
Quick Glossary: Cybersecurity Countermeasures – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Cybersecurity attacks are inevitable for modern businesses. Therefore, it is vital that businesses deploy countermeasures to mitigate the damage these attacks cause....
Sophos: ‘Royal’ Is Trying to Make Itself the King of Ransomware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading John Shier of Sophos shares findings of a company report on “Royal,” a dangerous new variation of...
Intelligent Vigilance: Empowering Security with Threat Intel’s CoPilot AI – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Cybersixgill’s Michael-Angelo Zummo talks about the impact of artificial intelligence, and the issues and questions it creates...
Cisco: Bringing More Intelligence to Bear on the Threat Landscape – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Cisco’s Nick Biasini describes how attackers’ tactics, techniques, and procedures continue to increase in sophistication, and what...
How to Protect Against Nation-State APT Attackers Leveraging Mobile Users – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Justin Albrecht of Lookout takes on the phenomenon of nation-state-sponsored attackers targeting mobile users with advanced persistent...
CrowdSec: What the ‘Network Effect’ Brings to the Cybersecurity Table – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The value of a utility increases as more people use it —and Philippe Humeau of CrowdSec shows...
Securing Critical Infrastructure in the Face of Evolving Cyber Threats – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Benny Czarny of OPSWAT outlines the threat landscape affecting critical infrastructure sectors, and how those organizations can...
Bitsight Leverages SPM to Bolster External Attack Surface Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Bitsight’s Greg Keshian checks the status of external attack surface management and how the emerging discipline of...
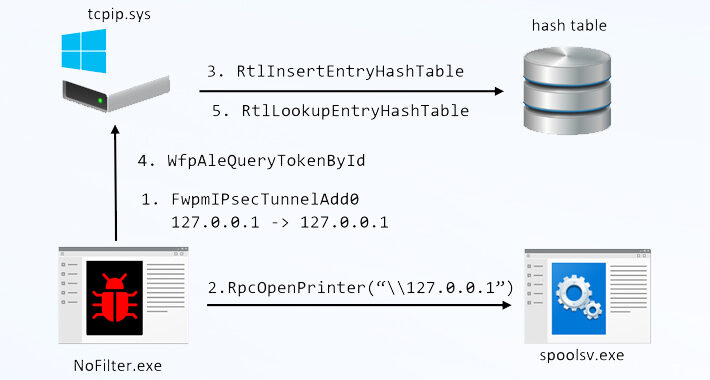
NoFilter Attack: Sneaky Privilege Escalation Method Bypasses Windows Security – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 17, 2023THNEndpoint Security / Vulnerability A previously undetected attack method called NoFilter has been found to abuse the Windows Filtering...
China-Linked Bronze Starlight Group Targeting Gambling Sector with Cobalt Strike Beacons – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 17, 2023THNCyber Attack / Malware An ongoing cyber attack campaign originating from China is targeting the Southeast Asian gambling sector...
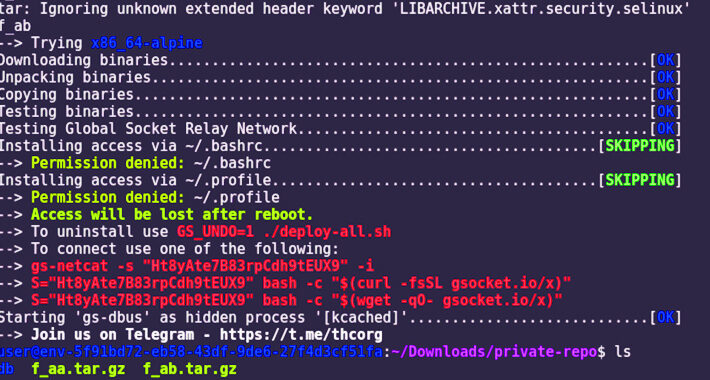
New LABRAT Campaign Exploits GitLab Flaw for Cryptojacking and Proxyjacking Activities – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 17, 2023THNCryptojacking / Proxyjacking A new, financially motivated operation dubbed LABRAT has been observed weaponizing a now-patched critical flaw in...
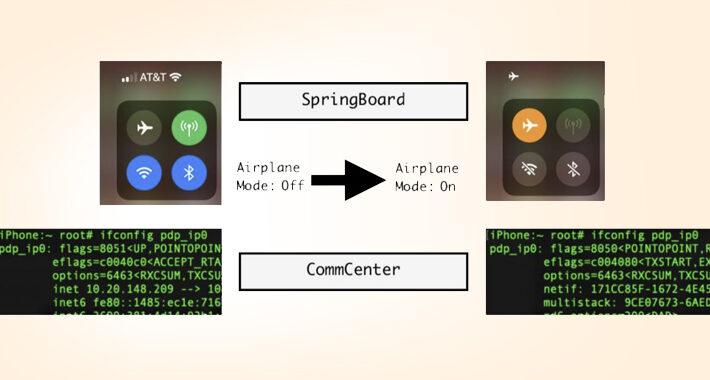
New Apple iOS 16 Exploit Enables Stealthy Cellular Access Under Fake Airplane Mode – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 17, 2023THNMobile Security / Vulnerability Cybersecurity researchers have documented a novel post-exploit persistence technique on iOS 16 that could be...
Why You Need Continuous Network Monitoring? – Source:thehackernews.com
Source: thehackernews.com – Author: . Changes in the way we work have had significant implications for cybersecurity, not least in network monitoring. Workers no longer sit...
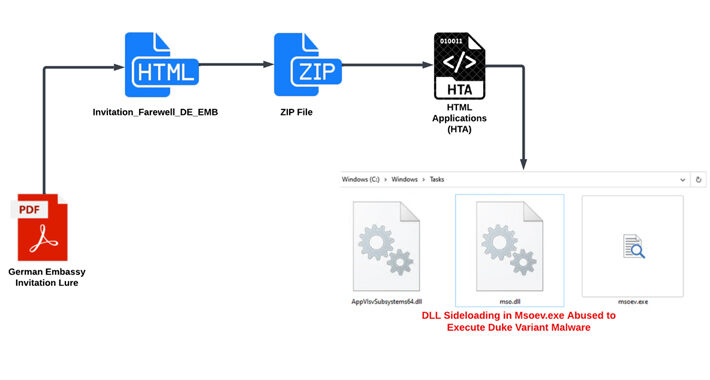
Russian Hackers Use Zulip Chat App for Covert C&C in Diplomatic Phishing Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 17, 2023THNCyber Espionage / Malware An ongoing campaign targeting ministries of foreign affairs of NATO-aligned countries points to the involvement...
CISA Adds Citrix ShareFile Flaw to KEV Catalog Due to In-the-Wild Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 17, 2023THNVulnerability / Enterprise Security The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a critical security flaw in...
Data Classification Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: In many ways, data has become the primary currency of modern organizations. It doesn’t matter whether you are a large business enterprise,...
PowerShell Gallery Prone to Typosquatting, Other Supply Chain Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Microsoft’s PowerShell Gallery presents a software supply chain risk because of its relatively weak protections against...
Researchers Harvest, Analyze 100K Cybercrime Forum Credentials – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Cybersecurity researchers running a sprawling information-stealer campaign collected credentials, autofill data, and system information that tied back...
Insurance Data Breach Victims File Class-Action Suit Against Law Firm – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Victims of a March data breach have filed a class-action suit against law firm Orrick, Herrington and...
Mirai Common Attack Methods Remain Consistent, Effective – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading The Mirai botnet continues to break records for driving the biggest and most disruptive distributed denial of...
What’s the State of Credential theft in 2023? – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 16, 2023The Hacker News At a little overt halfway through 2023, credential theft is still a major thorn in the...
Experts Uncover Weaknesses in PowerShell Gallery Enabling Supply Chain Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 16, 2023THNWindows Security / Supply Chain Active flaws in the PowerShell Gallery could be weaponized by threat actors to pull...