Source: www.darkreading.com – Author: Ericka Chickowski, Contributing Writer, Dark Reading Keep up with the latest cybersecurity threats, newly-discovered vulnerabilities, data breach information, and emerging trends. Delivered...
Author: admin
QR Code Phishing Campaign Targets Top US Energy Company – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Attackers targeted a major US energy company with a phishing campaign that overall sent more than 1,000...
Iran and the Rise of Cyber-Enabled Influence Operations – Source: www.darkreading.com
Source: www.darkreading.com – Author: Microsoft Security, Microsoft Iranian state actors have another weapon in their arsenal. Since June 2022, multiple Iranian state groups have deployed a...
Mandiant Releases Scanner to Identify Compromised NetScaler ADC, Gateway – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading With thousands of Citrix networking products vulnerable to a critical vulnerability still unpatched and exposed on the...
App Security Posture Management Improves Software Security, Synopsys Says – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Jim Ivers and Natasha Gupta of Synopsys discuss customer challenges with application security. They talk about consolidation...
Cyderes Dives In On Working Safely With AI and Upping Your IAM Game – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading John Ayers and Mike Wyatt weigh in on how artificial intelligence has already been weaponized against businesses...
Tel Aviv Stock Exchange CISO: Making Better Use of Your SIEM – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading For Gil Shua, getting the most out of the security information event management (SIEM) system for...
Time To Address What’s Undermining SaaS Security, AppOmni Says – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading SaaS security is battling numerous excesses, according to AppOmni CEO Brendan O’Connor: entitlement inflation, over-provisioned accounts, and...
PKI Maturity Model Aims to Improve Crypto Infrastructure – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading Creating and deploying public key infrastructure is notoriously difficult. However, a group of encryption vendors, consultancies,...
African Cybercrime Operations Shut Down in Law Enforcement Operation – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading In a months-long joint operation by Interpol and Afripol, 14 suspected cybercriminals have been arrested and more...
Researchers Trick an iPhone Into Faking Airplane Mode – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Researchers have figured out how to manipulate the iPhone user interface to feign airplane mode, while...
LinkedIn Suffers ‘Significant’ Wave of Account Hacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Hackers are on a spree of hijacking LinkedIn accounts, in some cases monetizing the attacks by demanding...
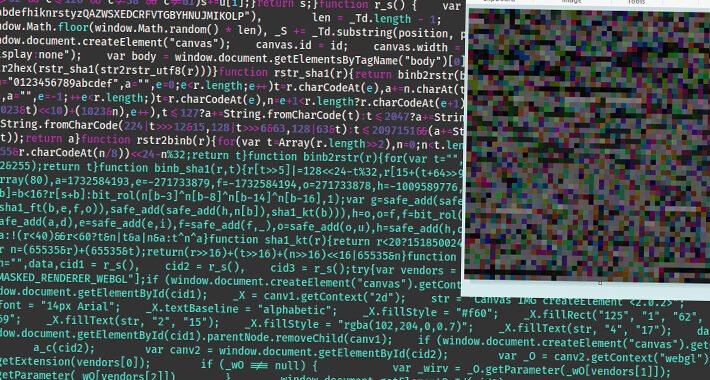
WoofLocker Toolkit Hides Malicious Codes in Images to Run Tech Support Scams – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 19, 2023THNMalvertising / Website Security Cybersecurity researchers have detailed an updated version of an advanced fingerprinting and redirection toolkit called...
Phishing Attack Targets Hundreds of Zimbra Customers in 4 Continents – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Despite its simplicity, a phishing campaign targeting customers of the Zimbra Collaboration software suite has spread...
CISA Committee Tackles Remote Monitoring and Management Protections – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Just two years after Cybersecurity and Infrastructure Security Agency (CISA) Director Jen Easterly unveiled the Joint Cyber...
Bugcrowd Unleashes Hacker Ingenuity for Proactive, Crowdsourced Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Casey Ellis and Dave Gerry of Bugcrowd stress the importance of crowdsourced threat intelligence, and also detail...
Hubble Urges Customers, Security Pros to Return to Infosec Basics – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Hubble CEO Tom Parker has been encouraging a “back to basics” approach to cybersecurity for at least...
Comcast: How to Wrap Enterprise Cybersecurity In the Data Fabric – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Comcast’s Noopur Davis discusses how big data is reshaping the fundamentals around security management, along with the...
Securonix: Making Sense of AI’s Rapid Acceleration in Cybersecurity – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Nayaki Nayyar of Securonix and Chris Inglis, former US National Cyber Director in the Biden administration, take...
Fortra Joins With Microsoft, Health-ISAC to Combat Cobalt Blue Fraud – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Bob Erdman of Fortra joins Dark Reading’s News Desk to talk about why his company teamed with...
New Juniper Junos OS Flaws Expose Devices to Remote Attacks – Patch Now – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 19, 2023THNNetwork Security / Vulnerability Networking hardware company Juniper Networks has released an “out-of-cycle” security update to address multiple flaws...
Thousands of Android Malware Apps Using Stealthy APK Compression to Evade Detection – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 19, 2023THNMobile Security / Malware Threat actors are using Android Package (APK) files with unknown or unsupported compression methods to...
14 Suspected Cybercriminals Arrested Across Africa in Coordinated Crackdown – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 18, 2023THNCyber Crime / Hacking News A coordinated law enforcement operation across 25 African countries has led to the arrest...
The Vulnerability of Zero Trust: Lessons from the Storm 0558 Hack – Source:thehackernews.com
Source: thehackernews.com – Author: . While IT security managers in companies and public administrations rely on the concept of Zero Trust, APTS (Advanced Persistent Threats) are...
New Wave of Attack Campaign Targeting Zimbra Email Users for Credential Theft – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 18, 2023THNEmail Seucrity / Cyber Attack A new “mass-spreading” social engineering campaign is targeting users of the Zimbra Collaboration email...
New BlackCat Ransomware Variant Adopts Advanced Impacket and RemCom Tools – Source:thehackernews.com
Source: thehackernews.com – Author: . Microsoft on Thursday disclosed that it found a new version of the BlackCat ransomware (aka ALPHV and Noberus) that embeds tools...
Unveiling the Hidden Risks of Routing Protocols – Source: www.darkreading.com
Source: www.darkreading.com – Author: Daniel dos Santos, Head of Security Research, Forescout’s Vedere Labs Routing protocols play a critical role in the functioning of the Internet...
Fastly Launches Certainly CA – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Edge cloud platform provider Fastly has announced the general availability of Certainly, its publicly trusted Transport Layer...
Confusion Surrounds SEC’s New Cybersecurity Material Rule – Source: www.darkreading.com
Source: www.darkreading.com – Author: Evan Schuman, Contributing Writer, Dark Reading One of the aims of the new cybersecurity disclosure rules approved by the Securities Exchange Commission...
Infoblox Blows Whistle On ‘Decoy Dog,’ Advocates For Better DNS Monitoring – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Renée Burton of Infoblox unveils the inner workings of Decoy Dog/Pupy, the RAT toolkit that uses the...