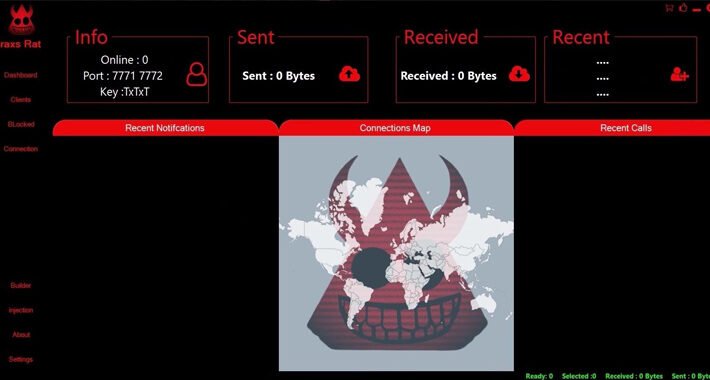
Source: thehackernews.com – Author: . Aug 23, 2023THNMobile Security / Cyber Crime A Syrian threat actor named EVLF has been outed as the creator of malware...
Author: admin
Agile Approach to Mass Cloud Credential Harvesting and Crypto Mining Sprints Ahead – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 23, 2023The Hacker NewsMalware / Cybersecurity Developers are not the only people who have adopted the agile methodology for their...
Electronic Communication Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: This policy provides guidelines for the appropriate use of electronic communications. It covers topics such as privacy, confidentiality and security; ensures electronic...
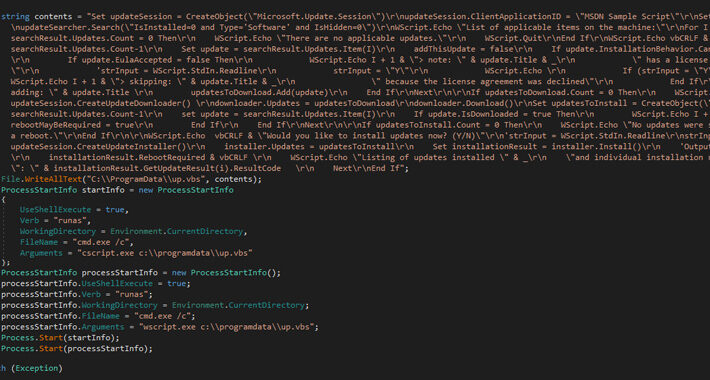
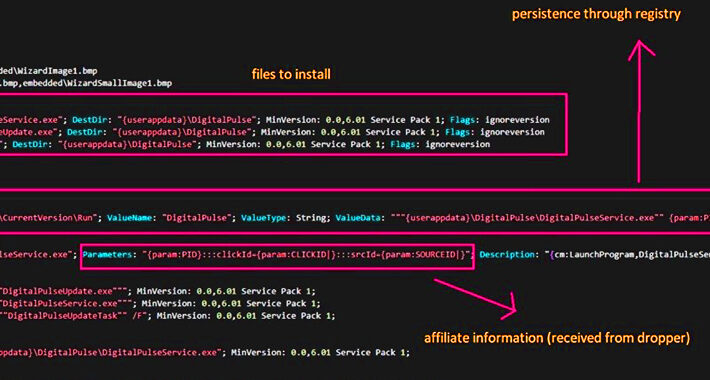
Spacecolon Toolset Fuels Global Surge in Scarab Ransomware Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 23, 2023THNRansomware / Malware A malicious toolset dubbed Spacecolon is being deployed as part of an ongoing campaign to spread...
Over a Dozen Malicious npm Packages Target Roblox Game Developers – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 23, 2023THNSoftware Security / Malware More than a dozen malicious packages have been discovered on the npm package repository since...
More Than Half of Browser Extensions Pose Security Risks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Many browser extensions that organizations permit employees to use when working with SaaS apps such as...
Adobe Patches Critical Deserialization Vulnerability, but Exploits Persist – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading CISA has added a vulnerability — cataloged as CVE-2023-26359 — to the Known Exploited Vulnerabilities Catalog with a CVSS...
Controversial Cybercrime Law Passes in Jordan – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading The Jordanian government has passed a new cybercrime law despite global criticism over its content and...
Newer, Better XLoader Signals a Dangerous Shift in macOS Malware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading A new Mac-oriented variant of the XLoader infostealer spread widely in the wild last month, signaling...
Software Makers May Face Greater Liability in Wake of MOVEit Lawsuit – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading A nationwide class-action suit filed against Progress Software in the wake of the massive MOVEit breach could...
When Leadership Style Is a Security Risk – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tyler Farrar, CISO, Exabeam Effective leaders have the power to motivate, inspire, encourage, and guide their teams. While C-suite leadership may receive...
Innovation Hides in Plain Sight and Openly Delights – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Smart spaces bring together universal connectivity, security, and intelligence to modernize the workspace experience. But what are technology leaders saying about this...
Reimagining Your Video Data Strategy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Did you know that about 99% of surveillance video goes unviewed? What if you could use that video data to simplify operations,...
Chinese APT Targets Hong Kong in Supply Chain Attack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading An emerging China-backed advanced persistent threat (APT) group targeted organizations in Hong Kong in a supply chain...
Ivanti Issues Fix for Critical Vuln In Its Sentry Gateway Technology – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Organizations using almost any version of the Ivanti Sentry security gateway product might want to immediately...
Tesla Data Breach Investigation Reveals Inside Job – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Tesla acknowledged In a filing with Maine’s attorney general that a recent data breach it experienced affecting...
Fed Warning: US Space Industry Subject To Foreign Spying, Disruptions – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer, Dark Reading Foreign adversaries are waging cyber espionage campaigns against the US space industry, according to a joint...
Energy One Investigates Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Wholesale energy software software provider Energy One reported on Friday a cyberattack had affected “certain corporate systems”...
Carderbee Attacks: Hong Kong Organizations Targeted via Malicious Software Updates – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 22, 2023THNSoftware Supply Chain / Malware A previously undocumented threat cluster has been linked to a software supply chain attack...
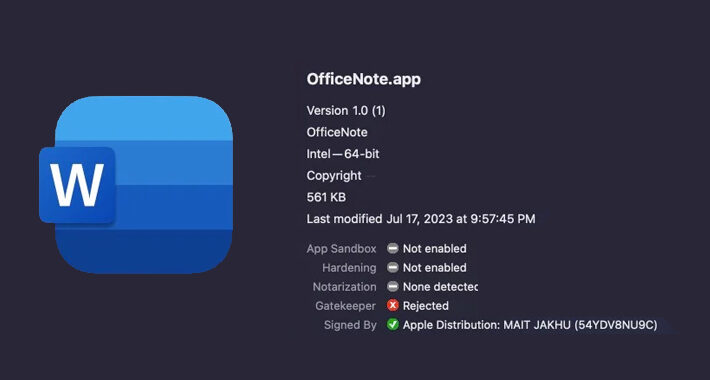
New Variant of XLoader macOS Malware Disguised as ‘OfficeNote’ Productivity App – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 22, 2023THNMalware / Endpoint Security A new variant of an Apple macOS malware called XLoader has surfaced in the wild,...
Ivanti Warns of Critical Zero-Day Flaw Being Actively Exploited in Sentry Software – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 22, 2023THNZero-Day / Software Security Software services provider Ivanti is warning of a new critical zero-day flaw impacting Ivanti Sentry...
Critical Adobe ColdFusion Flaw Added to CISA’s Exploited Vulnerability Catalog – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 22, 2023THNVulnerability / Cyber Threat The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a critical security flaw in...
New WinRAR Vulnerability Could Allow Hackers to Take Control of Your PC – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 21, 2023THNVulnerability / Cyber Threat A high-severity security flaw has been disclosed in the WinRAR utility that could be potentially...
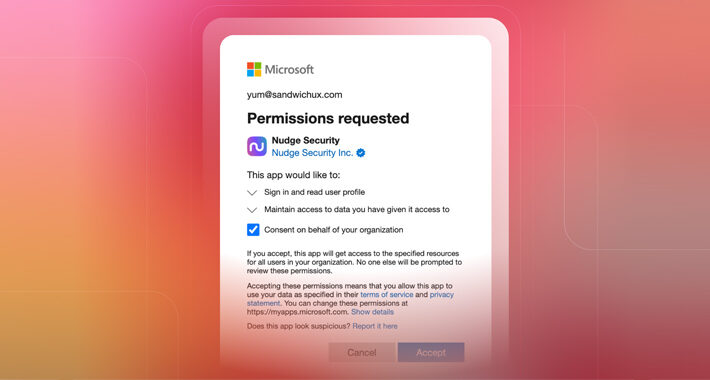
How to Investigate an OAuth Grant for Suspicious Activity or Overly Permissive Scopes – Source:thehackernews.com
Source: thehackernews.com – Author: . From a user’s perspective, OAuth works like magic. In just a few keystrokes, you can whisk through the account creation process...
DEF CON’s AI Village Pits Hackers Against LLMs to Find Flaws – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading DEF CON 2023 — Las Vegas — DEF CON’s most buzzed-about event, the AI Village, let thousands...
This Malware Turned Thousands of Hacked Windows and macOS PCs into Proxy Servers – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 21, 2023THNMalware / Privacy Threat actors are leveraging access to malware-infected Windows and macOS machines to deliver a proxy server...
HiatusRAT Malware Resurfaces: Taiwan Firms and U.S. Military Under Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 21, 2023THNCyber Threat / Malware The threat actors behind the HiatusRAT malware have returned from their hiatus with a new...
‘Play’ Ransomware Group Targeting MSPs Worldwide in New Campaign – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading The fast-rising Play ransomware group that targeted the City of Oakland earlier this year is now...
Cyber Defenders Lead the AI Arms Race for Now – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Cyber defenders so far are winning the war over artificial intelligence: AI tools have yet to...
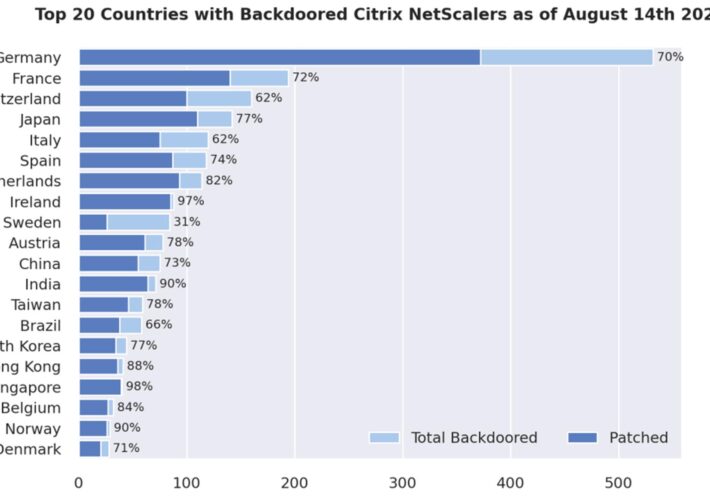
Citrix ADC, Gateways Still Backdoored, Even After Being Patched – Source: www.darkreading.com
Source: www.darkreading.com – Author: Edge Editors, Dark Reading Nearly 1,900 Citrix networking products around the world have been backdoored as part of a large-scale automated campaign...