Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Citizen Lab discovered two no-click zero-day vulnerabilities while checking an unidentified individual’s device, which was delivering mercenary...
Author: admin
Rwanda Launches Smart-City Investment Program – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Rwanda plans to modernize its infrastructure with a series of smart-city deployments that experts warn will...
Security for Multicloud and Hybrid Cloud Environments – Source: www.darkreading.com
Source: www.darkreading.com – Author: Anton Chuvakin, Security Advisor at Office of the CISO, Google Cloud No matter the industry, multicloud and hybrid cloud environments are an...
NFL Security Chief: Generative AI Threats a Concern as New Season Kicks Off – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Generative AI-enabled phishing attacks and deepfake videos are among the many threats that Tomás Maldonado will...
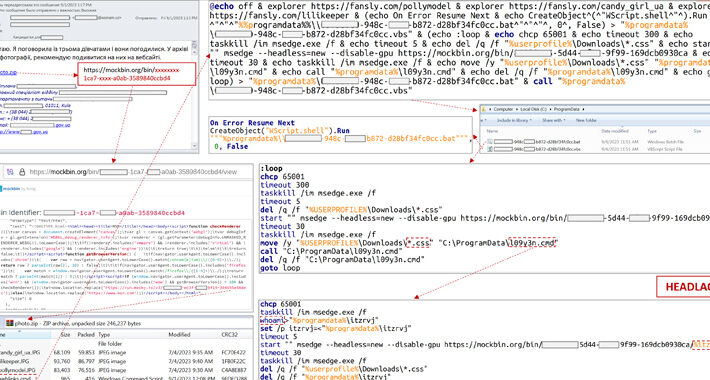
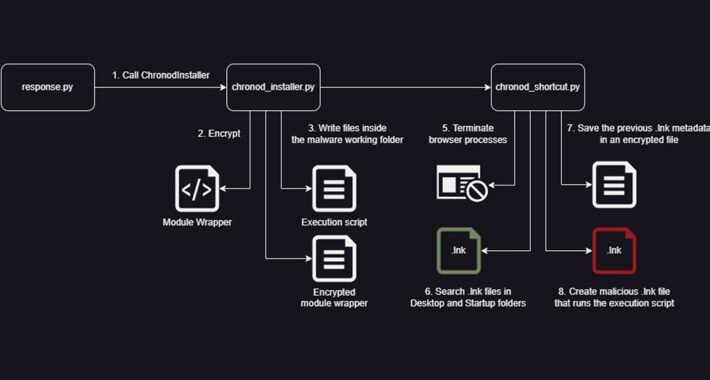
Weaponized Windows Installers Target Graphic Designers in Crypto Heist – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Attackers are targeting 3D modelers and graphic designers with malicious versions of a legitimate Windows installer tool...
Peril vs. Promise: Companies, Developers Worry Over Generative AI Risk – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading The vast majority of developers believe that using generative AI systems will be necessary to increase...
Does Generative AI Comply With Asimov’s 3 Laws of Robotics? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Martin Lee, Technical Lead of Security Research & EMEA Lead, Cisco Talos Newly developed generative artificial intelligence (AI) tools that can generate...
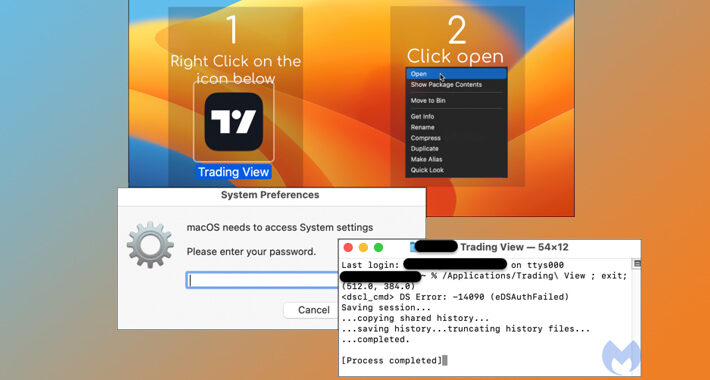
Mac Users Beware: Malvertising Campaign Spreads Atomic Stealer macOS Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 07, 2023THNMalvertising / Endpoint Security A new malvertising campaign has been observed distributing an updated version of a macOS stealer...
The State of the Virtual CISO Report: MSP/MSSP Security Strategies for 2024 – Source:thehackernews.com
Source: thehackernews.com – Author: . By the end of 2024, the number of MSPs and MSSPs offering vCISO services is expected to grow by almost 5...
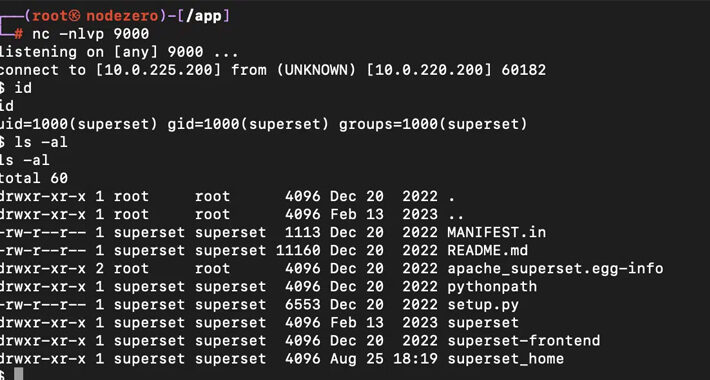
Alert: Apache Superset Vulnerabilities Expose Servers to Remote Code Execution Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 07, 2023THNServer Security / Vulnerability Patches have been released to address two new security vulnerabilities in Apache Superset that could...
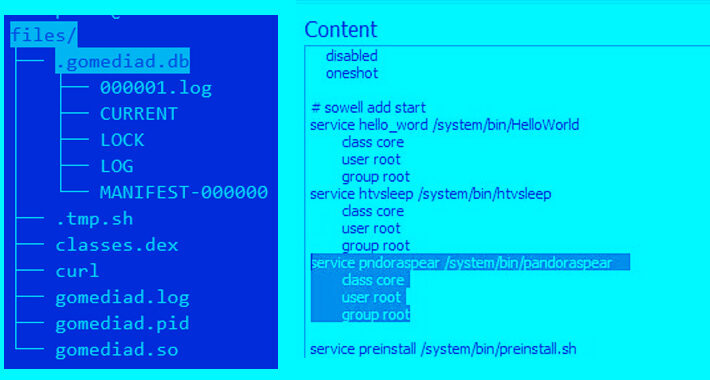
Mirai Botnet Variant ‘Pandora’ Hijacks Android TVs for Cyberattacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 07, 2023THNBotnet / Cyber Threat A Mirai botnet variant called Pandora has been observed infiltrating inexpensive Android-based TV sets and...
Outlook Breach: Microsoft Reveals How a Crash Dump Led to a Major Security Breach – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 07, 2023THNCyber Attack / Email Hacking Microsoft on Wednesday revealed that a China-based threat actor known as Storm-0558 acquired the...
Cybersecurity Builds Trust in Critical Infrastructure – Source: www.darkreading.com
Source: www.darkreading.com – Author: Leo Simonovich, VP & Global Head, Industrial Cyber and Digital Security, Siemens Energy In 2021, a ransomware attack shut down Colonial Pipeline...
W3LL Gang Compromises Thousands of Microsoft 365 Accounts – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading A sprawling phishing empire from a threat actor known as W3LL is spreading globally, successfully...
AtlasVPN Linux Zero-Day Disconnects Users, Reveals IP Addresses – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading A security researcher has published exploit code for AtlasVPN for Linux, which could enable anybody to...
MinIO Cyberattack Showcases Fresh Corporate Cloud Vector – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading A brand-new attack vector has emerged in the cloud, allowing cybercriminals to remotely execute code and take...
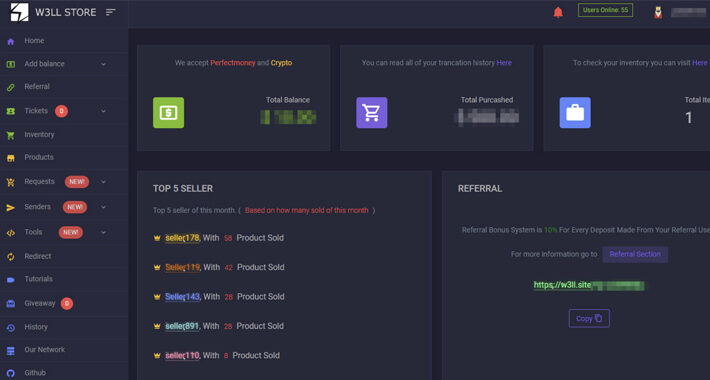
Russia’s ‘Fancy Bear’ APT Targets Ukrainian Energy Facility – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Earlier this week, infamous Russian cyberespionage group Fancy Bear (aka APT28, Strontium, or Sofacy) was caught attacking...
Google’s Souped-up Chrome Store Review Process Foiled by Data-Stealer – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Malicious yet legitimate-looking Google Chrome browser extensions that steal people’s passwords and other sensitive data can still...
Zero-Day Alert: Latest Android Patch Update Includes Fix for Newly Actively Exploited Flaw – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 06, 2023THNZero Day / Mobile Security Google has rolled out monthly security patches for Android to address a number of...
Alert: Phishing Campaigns Deliver New SideTwist Backdoor and Agent Tesla Variant – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 06, 2023THNCyber Threat / Malware The Iranian threat actor tracked as APT34 has been linked to a new phishing attack...
Three CISOs Share How to Run an Effective SOC – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 06, 2023The Hacker NewsSecurity Operations Center (SOC) The role of the CISO keeps taking center stage as a business enabler:...
Researchers Discover Critical Vulnerability in PHPFusion CMS – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Security researchers have discovered what they described as a critical vulnerability in the relatively widely used...
LockBit Leaks Documents Filched From UK Defense Contractor – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Last month, a British perimeter security company was breached by the LockBit group. Despite only accessing...
GhostSec Leaks Source Code of Alleged Iranian Surveillance Tool – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Hacker group GhostSec is disclosing the source code of the various software packages, alleging them to...
Peiter ‘Mudge’ Zatko Lands Role as CISA Senior Technical Adviser – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Former Twitter security chief and “executive in residence” at cybersecurity firm Rapid7, Peiter “Mudge” Zatko, has landed...
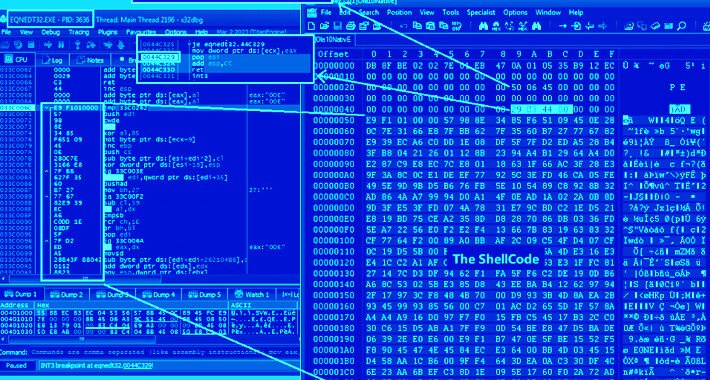
9 Alarming Vulnerabilities Uncovered in SEL’s Power Management Products – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 06, 2023THNVulnerability / ICS Nine security flaws have been disclosed in electric power management products made by Schweitzer Engineering Laboratories...
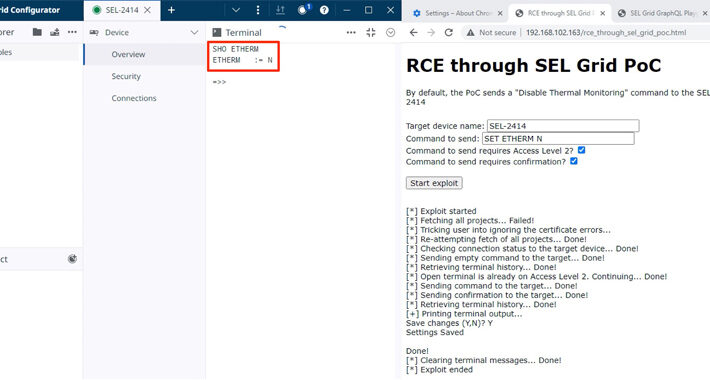
W3LL Store: How a Secret Phishing Syndicate Targets 8,000+ Microsoft 365 Accounts – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 06, 2023THNCyber Crime / Email Security A previously undocumented “phishing empire” has been linked to cyber attacks aimed at compromising...
Ukraine’s CERT Thwarts APT28’s Cyberattack on Critical Energy Infrastructure – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 06, 2023THNCyber Attack / Critical Infrastructure The Computer Emergency Response Team of Ukraine (CERT-UA) on Tuesday said it thwarted a...
New BLISTER Malware Update Fuelling Stealthy Network Infiltration – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 05, 2023THNCyber Threat / Malware An updated version of a malware loader known as BLISTER is being used as part...
New Python Variant of Chaes Malware Targets Banking and Logistics Industries – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 05, 2023THNCyber Threat / Malware Banking and logistics industries are under the onslaught of a reworked variant of a malware...