Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Hijacking opensource software packages to insert malicious code has become a popular way for attackers to spread...
Author: admin
Cybersecurity Skills Gap: Roadies & Gamers Are Untapped Talent – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jim Broome, President & CTO, DirectDefense In the world of cybersecurity, innovation often comes from unexpected sources. As organizations grapple with the...
Recent Rhysida Attacks Show Focus on Healthcare by Ransomware Actors – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading The threat group behind the fast-growing Rhysida ransomware-as-a-service operation has claimed credit for an Aug. 19...
Alert: New Kubernetes Vulnerabilities Enable Remote Attacks on Windows Endpoints – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 13, 2023THNKubernetes / Cloud Security Three interrelated high-severity security flaws discovered in Kubernetes could be exploited to achieve remote code...
Researchers Detail 8 Vulnerabilities in Azure HDInsight Analytics Service – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 13, 2023THNVulnerability / Data Security More details have emerged about a set of now-patched cross-site scripting (XSS) flaws in the...
Webinar: Identity Threat Detection & Response (ITDR) – Rips in Your Identity Fabric – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 13, 2023The Hacker NewsThreat Detection / SaaS Security In today’s digital age, SaaS applications have become the backbone of modern...
Rust-Written 3AM Ransomware: A Sneak Peek into a New Malware Family – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 13, 2023THNRansomware / Malware A new ransomware family called 3AM has emerged in the wild after it was detected in...
How Cyberattacks Are Transforming Warfare – Source:thehackernews.com
Source: thehackernews.com – Author: . There is a new battlefield. It is global and challenging to defend. What began with a high-profile incident back in 2007,...
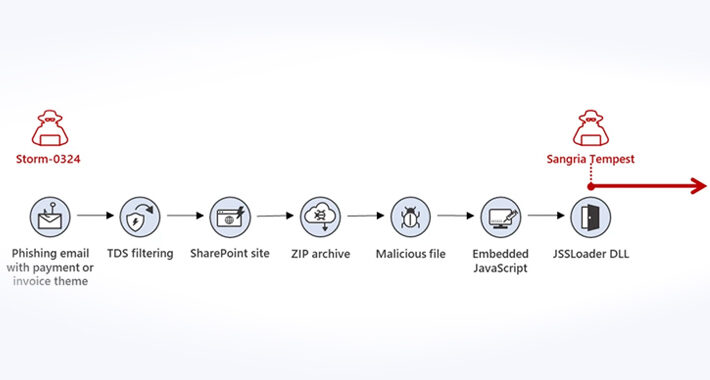
Microsoft Warns of New Phishing Campaign Targeting Corporations via Teams Messages – Source:thehackernews.com
Source: thehackernews.com – Author: . Microsoft is warning of a new phishing campaign undertaken by an initial access broker that involves using Teams messages as lures...
Microsoft Releases Patch for Two New Actively Exploited Zero-Days Flaws – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 13, 2023THNEndpoint Security / Zero Day Microsoft has released software fixes to remediate 59 bugs spanning its product portfolio, including...
Update Adobe Acrobat and Reader to Patch Actively Exploited Vulnerability – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 13, 2023THNVulnerability / Zero Day Adobe’s Patch Tuesday update for September 2023 comes with a patch for a critical actively...
Mozilla Rushes to Patch WebP Critical Zero-Day Exploit in Firefox and Thunderbird – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 13, 2023THNVulnerability / Browser Security Mozilla on Tuesday released security updates to resolve a critical zero-day vulnerability in Firefox and...
Microsoft Patches a Pair of Actively Exploited Zero-Days – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Microsoft addressed five critical security vulnerabilities in its September Patch Tuesday update, along with two...
China’s Winnti APT Compromises National Grid in Asia for 6 Months – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading A Chinese threat actor managed to breach the national power grid in an unnamed Asian country...
Critical Google Chrome Zero-Day Bug Exploited in the Wild – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading A zero-day vulnerability with critical severity has been discovered in Google Chrome, and has been patched in an...
Israeli Hospital Hit By Ransomware Attack, 1TB Data Stolen – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Cyber attackers who hit an Israeli hospital have begun releasing sensitive data that it collected in the...
IBM Adds Data Security Broker to Encrypt Data in Multiclouds – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jeffrey Schwartz, Contributing Writer, Dark Reading Encrypting personally identifiable information (PII) in distributed multicloud environments is a complex endeavor, with enterprise security...
MGM Resorts Cyberattack Hobbles Las Vegas Strip Operations – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading MGM Resorts is battling to recover its systems following a Sept. 10 cyberattack that left its hotel...
ChatGPT Jailbreaking Forums Proliferate in Dark Web Communities – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading The weaponization of generative AI tools like ChatGPT that everybody has been waiting for is slowly, slowly beginning...
Millions of Facebook Business Accounts Bitten by Python Malware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Attackers are targeting millions of Facebook business accounts with malicious messages, sent via Facebook Messenger from a botnet of...
‘Anonymous Sudan’ Sets Its Sights on Telegram in DDoS Attack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading After Telegram — the free, encrypted, cloud-based messaging service — initiated a suspension of hacker group Anonymous...
Critical GitHub Vulnerability Exposes 4,000+ Repositories to Repojacking Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 12, 2023THNSoftware Security / Vulnerability A new vulnerability disclosed in GitHub could have exposed thousands of repositories at risk of...
IT Staff Systems and Data Access Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: IT professionals, such as system and network administrators, help desk staff, management personnel and sometimes external vendor representatives, are routinely provided full...
Iran’s Charming Kitten Pounces on Israeli Exchange Servers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading In the last two years, an Iranian state-backed threat actor has breached 32 Israeli organizations running...
Being Flexible Can Improve Your Security Posture – Source: www.darkreading.com
Source: www.darkreading.com – Author: Joshua Goldfarb, Security and Fraud Architect, F5 Recently, I was working on a specific task. About an hour into the task, I...
‘Steal-It’ Campaign Uses OnlyFans Models as Lures – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading A sophisticated cyber campaign is using images of OnlyFans models and geofencing to target specific victims across...
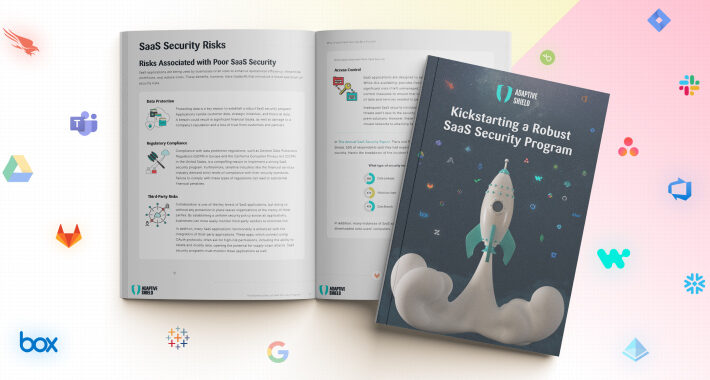
7 Steps to Kickstart Your SaaS Security Program – Source:thehackernews.com
Source: thehackernews.com – Author: . SaaS applications are the backbone of modern businesses, constituting a staggering 70% of total software usage. Applications like Box, Google Workplace,...
Chinese Redfly Group Compromised a Nation’s Critical Grid in 6-Month ShadowPad Campaign – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 12, 2023THNCritical Infrastructure Security A threat actor called Redfly has been linked to a compromise of a national grid located...
Sophisticated Phishing Campaign Deploying Agent Tesla, OriginBotnet, and RedLine Clipper – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 12, 2023THNEndpoint Security / Malware A sophisticated phishing campaign is using a Microsoft Word document lure to distribute a trifecta...
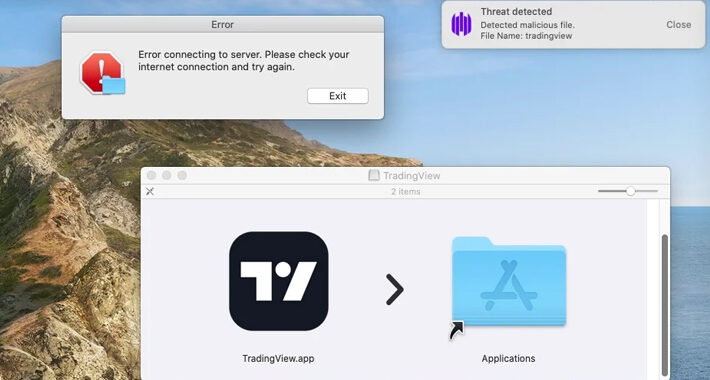
Beware: MetaStealer Malware Targets Apple macOS in Recent Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 12, 2023THNEndpoint Security / Data Security A new information stealer malware called MetaStealer has set its sights on Apple macOS,...