Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Hardware-based authentication company Yubico is now a publicly traded company on the Nasdaq First North Growth Market...
Author: admin
Fake WinRAR PoC Exploit Conceals VenomRAT Malware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading In a new twist on the cybercrime penchant for trojanizing things, a threat actor recently...
FBI, CISA Issue Joint Warning on ‘Snatch’ Ransomware-as-a-Service – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Cybersecurity advisories from the FBI and the US Cybersecurity and Infrastructure Security Agency (CISA) are usually...
China Accuses U.S. of Decade-Long Cyber Espionage Campaign Against Huawei Servers – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 21, 2023THNCyber Espionage / Spyware China’s Ministry of State Security (MSS) has accused the U.S. of breaking into Huawei’s servers,...
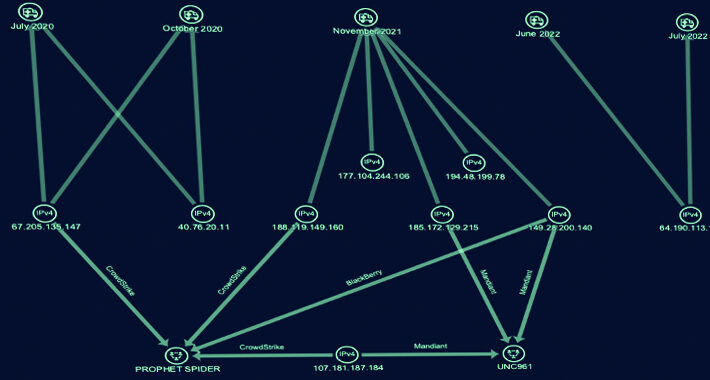
Cyber Group ‘Gold Melody’ Selling Compromised Access to Ransomware Attackers – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 21, 2023THNCyber Threat / Ransomware A financially motivated threat actor has been outed as an initial access broker (IAB) that...
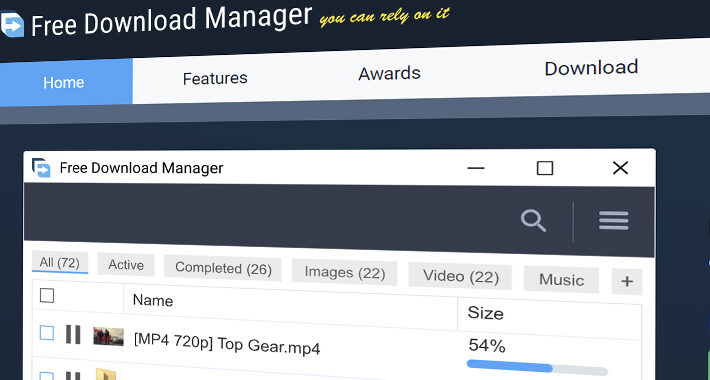
Ukrainian Hacker Suspected to be Behind “Free Download Manager” Malware Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 21, 2023THNSupply Chain / Malware The maintainers of Free Download Manager (FDM) have acknowledged a security incident dating back to...
Beware: Fake Exploit for WinRAR Vulnerability on GitHub Infects Users with Venom RAT – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 21, 2023THNVulnerability / Exploit A malicious actor released a fake proof-of-concept (PoC) exploit for a recently disclosed WinRAR vulnerability on...
Secure Equipment Repair Policy and Confidentiality Agreement – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Organizations must frequently work with third parties to repair laptops, desktops, tablets, smartphones, servers and other IT equipment. This policy from TechRepublic...
Finnish Authorities Dismantle Notorious PIILOPUOTI Dark Web Drug Marketplace – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 20, 2023THNCyber Crime / Dark Web Finnish law enforcement authorities have announced the takedown of PIILOPUOTI, a dark web marketplace...
Critical Security Flaws Exposed in Nagios XI Network Monitoring Software – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 20, 2023THNNetwork Security / Vulnerability Multiple security flaws have been disclosed in the Nagios XI network monitoring software that could...
Do You Really Trust Your Web Application Supply Chain? – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 20, 2023The Hacker NewsWeb Application Security Well, you shouldn’t. It may already be hiding vulnerabilities. It’s the modular nature of...
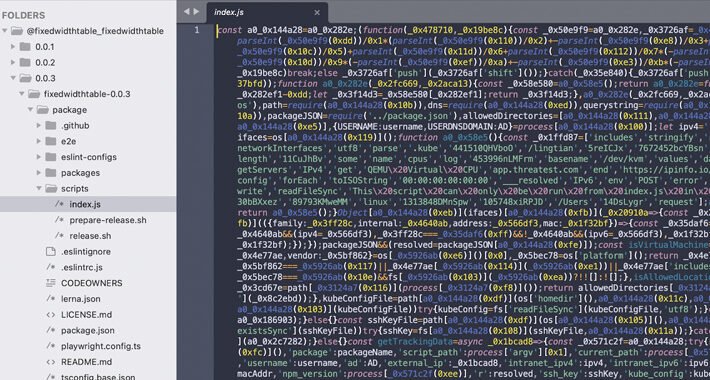
Fresh Wave of Malicious npm Packages Threaten Kubernetes Configs and SSH Keys – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 20, 2023THNKubernetes / Supply Chain Attack Cybersecurity researchers have discovered a fresh batch of malicious packages in the npm package...
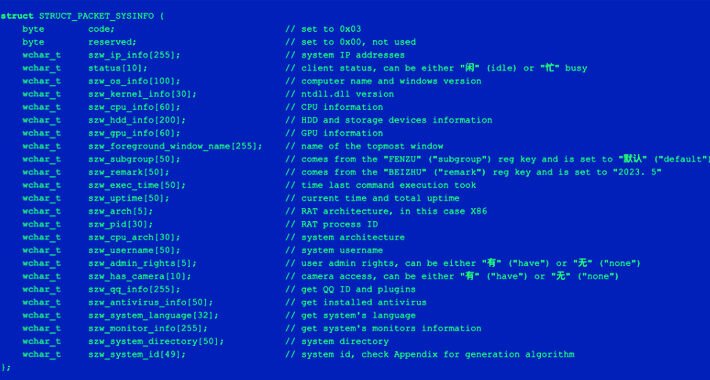
Sophisticated Phishing Campaign Targeting Chinese Users with ValleyRAT and Gh0st RAT – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 20, 2023THNMalware Attack / Cyber Threat Chinese-language speakers have been increasingly targeted as part of multiple email phishing campaigns that...
International Criminal Court Suffers Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The International Criminal Court (ICC) revealed that it suffered a cyberattack last week and is investigating the...
How Choosing Authentication Is a Business-Critical Decision – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kevin Reed, CISO, Acronis The COVID-19 pandemic prompted organizations to operate remotely, and many of them do not intend to return to...
‘Culturestreak’ Malware Lurks Inside GitLab Python Package – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading In what’s becoming an all-too-common occurrence in the current threat landscape, security researchers have found yet another...
Changing Role of the CISO: A Holistic Approach Drives the Future – Source: www.darkreading.com
Source: www.darkreading.com – Author: Graeme Payne, Senior Director of Strategy, Risk, and Compliance & Identity Protection, Kudelski Security In the modern enterprise, the responsibility for security...
Pro-Iranian Attackers Target Israeli Railroad Network – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The pro-Iranian Cyber Avengers cyberattack group has hit yet another Israeli public service, revealing information about the...
Signal Messenger Introduces PQXDH Quantum-Resistant Encryption – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 20, 2023THNEncryption / Privacy Encrypted messaging app Signal has announced an update to the Signal Protocol to add support for...
GitLab Releases Urgent Security Patches for Critical Vulnerability – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 20, 2023THNVulnerability / Software Security GitLab has shipped security patches to resolve a critical flaw that allows an attacker to...
Trend Micro Releases Urgent Fix for Actively Exploited Critical Security Vulnerability – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 20, 2023THNZero Day / Vulnerability Cybersecurity company Trend Micro has released patches and hotfixes to address a critical security flaw...
macOS Tune-Up Checklist – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Macs, like Windows computers, benefit from routine maintenance. Regular tune-ups help protect Macs, both desktop and laptop models, from potential data loss,...
China-Linked Actor Taps Linux Backdoor in Forceful Espionage Campaign – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading “Earth Lusca,” a China-linked cyber espionage actor that’s been actively targeting government organizations in Asia, Latin...
Trend Micro Patches Zero-Day Endpoint Vulnerability – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Trend Micro has released an advisory covering a critical zero-day flaw — tracked as CVE-2023-41179 — that...
MGM, Caesars Face Regulatory, Legal Maze After Cyber Incidents – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading In the wake of the new Securities and Exchange Commission (SEC) regulatory requirements to disclose “material” cyber...
Qatar Cyber Chiefs Warn on Mozilla RCE Bugs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The National Cyber Security Agency in Qatar is warning Adobe users to urgently apply patches following the...
Name That Toon: Somewhere in Sleepy Hollow – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Klossner, Cartoonist Harken, readers! ‘Tis you we love! Come up with a clever cybersecurity-related caption for the cartoon, above! (Our favorite...
Clorox Sees Product Shortages Amid Cyberattack Cleanup – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading The Clorox Company is starting to feel the pinch of product shortages after a recent...
CapraRAT Impersonates YouTube to Hijack Android Devices – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading A known Pakistan-linked threat actor is dangling romance-based content lures to spread Android-based spyware that mimics YouTube...
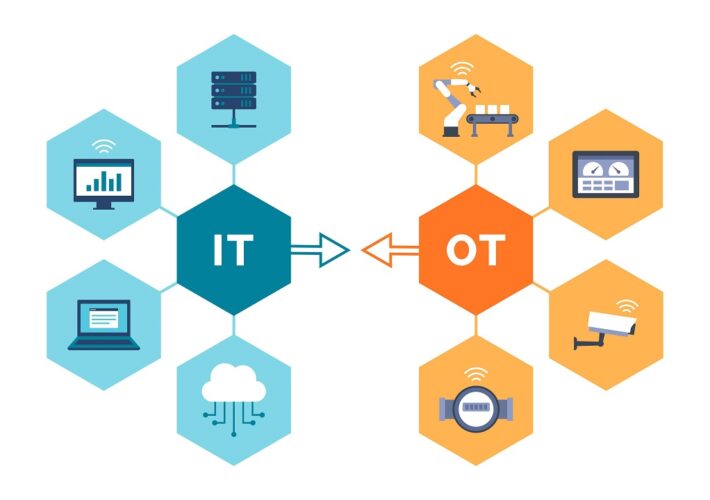
Engineering-Grade OT Protection – Source: www.darkreading.com
Source: www.darkreading.com – Author: Andrew Ginter, Vice President of Industrial Security, Waterfall Security Solutions The following are excerpts from a book set to be launched Nov....