Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer, Dark Reading As QR codes have become ubiquitous, their proliferation has given rise to new and emerging security...
Author: admin
How the Okta Cross-Tenant Impersonation Attacks Succeeded – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nigel Douglas, Senior Technical Manager, Detection & Response, Sysdig A series of highly sophisticated attacks have sparked significant concerns among organizations that...
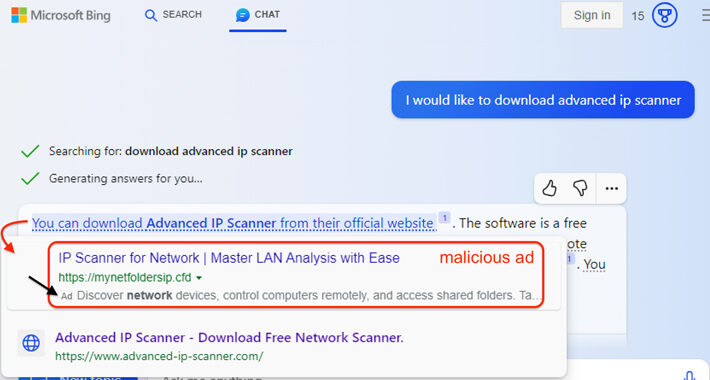
Microsoft’s AI-Powered Bing Chat Ads May Lead Users to Malware-Distributing Sites – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 29, 2023THNArtificial Intelligence / Malware Malicious ads served inside Microsoft Bing’s artificial intelligence (AI) chatbot are being used to distribute...
Progress Software Releases Urgent Hotfixes for Multiple Security Flaws in WS_FTP Server – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 29, 2023THNServer Security / Vulnerability Progress Software has released hotfixes for a critical security vulnerability, alongside seven other flaws, in...
Cisco Warns of Vulnerability in IOS and IOS XE Software After Exploitation Attempts – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 29, 2023THNVulnerability / Network Security Cisco is warning of attempted exploitation of a security flaw in its IOS Software and...
Government Shutdown Poised to Stress Nation’s Cybersecurity Supply Chain – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading The looming US federal government shutdown will put the nation’s cybersecurity apparatus under intense strain, increasing the...
Chrome Flags Third Zero-Day This Month That’s Tied to Spying Exploits – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Google has fixed a zero-day vulnerability in its Chrome browser that a commercial vendor has already...
New Cisco IOS Zero-Day Delivers a Double Punch – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading A vulnerability affecting Cisco operating systems could enable attackers to take full control of affected devices,...
Johnson Controls International Disrupted by Major Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Johnson Controls International (JCI) this week reported in a filing with the US Securities and Exchange Commission...
Q&A: UK Ambassador on Creating New Cybersecurity Agencies Around the World – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Juliette Wilcox, cybersecurity ambassador for the UK’s Department for International Trade. The UK’s National Cybersecurity Centre...
Novel ZenRAT Scurries Onto Systems via Fake Password Manager Tool – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading A novel info-stealing malware variant is lurking behind fake installation packages of the open source password manager...
4 Legal Surprises You May Encounter After a Cybersecurity Incident – Source: www.darkreading.com
Source: www.darkreading.com – Author: Beth Burgin Waller, Chair, Cybersecurity & Data Privacy Practice, Woods Rogers Vandeventer Black Most security professionals know the parade of problems that...
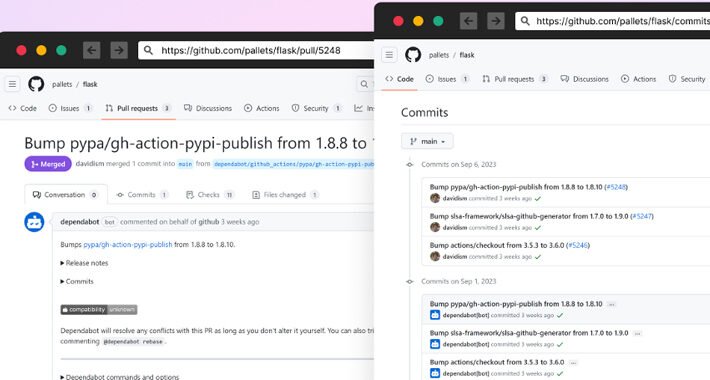
Supply Chain Attackers Escalate With GitHub Dependabot Impersonation – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading In the latest attack to target software supply chains, attackers managed to slip in malicious code...
Kenyan Financial Firm Fined for Mishandling Data – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The Kenyan Data Protection Commissioner has issued monetary penalties to multiple organizations over the mishandling of personal...
GitHub Repositories Hit by Password-Stealing Commits Disguised as Dependabot Contributions – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 28, 2023THNSupply Chain / Malware A new malicious campaign has been observed hijacking GitHub accounts and committing malicious code disguised...
China’s BlackTech Hacking Group Exploited Routers to Target U.S. and Japanese Companies – Source:thehackernews.com
Source: thehackernews.com – Author: . Cybersecurity agencies from Japan and the U.S. have warned of attacks mounted by a state-backed hacking group from China to stealthily...
The Dark Side of Browser Isolation – and the Next Generation Browser Security Technologies – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 28, 2023The Hacker NewsBrowser Security / Cybersecurity The landscape of browser security has undergone significant changes over the past decade....
China-Linked Budworm Targeting Middle Eastern Telco and Asian Government Agencies – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 28, 2023THNMalware / Cyber Threat Government and telecom entities have been subjected to a new wave of attacks by a...
Update Chrome Now: Google Releases Patch for Actively Exploited Zero-Day Vulnerability – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 28, 2023THNZero Day / Vulnerability Google on Wednesday rolled out fixes to address a new actively exploited zero-day in the...
CAPTCHAs Easy for Humans, Hard for Bots – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Proton, the company behind the end-to-end encrypted Proton Mail, released PRoton CAPTCHA, a layered system to differentiate...
A Preview of Windows 11’s Passkeys Support – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jeffrey Schwartz, Contributing Writer, Dark Reading Back in May 2022, Microsoft promised support for passwordless authentication using passkeys in the Windows operating...
Researchers Release Details of New RCE Exploit Chain for SharePoint – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Researchers who discovered two critical vulnerabilities in Microsoft SharePoint Server have released details of an exploit...
China APT Cracks Cisco Firmware in Attacks Against the US and Japan – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading An old Chinese state-linked threat actor has been quietly manipulating Cisco routers to breach multinational organizations...
Microsoft Adds Passkeys to Windows 11 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading In a major update to its Windows 11 operating system this week, Microsoft has integrated Passkeys alongside...
Hackers Trick Outlook Into Showing Fake AV Scans – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Threat actors are employing an existing technique of zero-point font obfuscation in a new way to fool...
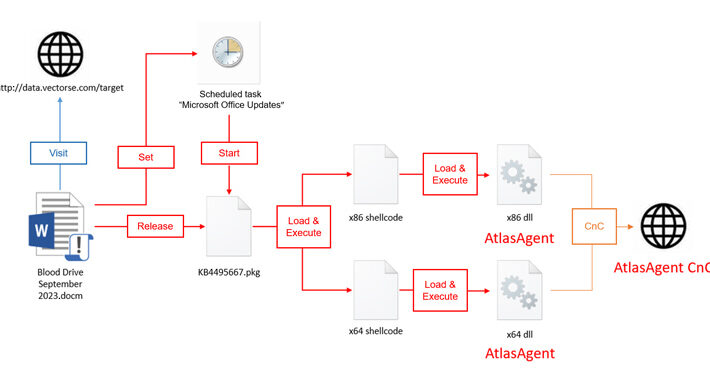
Red Cross-Themed Phishing Attacks Distributing DangerAds and AtlasAgent Backdoors – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 27, 2023THNMalware / Cyber Attack A new threat actor known as AtlasCross has been observed leveraging Red Cross-themed phishing lures...
Researchers Uncover New GPU Side-Channel Vulnerability Leaking Sensitive Data – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 27, 2023THNVulnerability / Endpoint Security A novel side-channel attack called GPU.zip renders virtually all modern graphics processing units (GPU) vulnerable...
New Survey Uncovers How Companies Are Confronting Data Security Challenges Head-On – Source:thehackernews.com
Source: thehackernews.com – Author: . Data security is in the headlines often, and it’s almost never for a positive reason. Major breaches, new ways to hack...
Will Government Secure Open Source or Muck It Up? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading Can open source software be regulated? Should it be regulated? And if so, will it lead...
Suspicious New Ransomware Group Claims Sony Hack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading A new threat actor is offering files purportedly stolen from Sony on the Dark Web, but...