85% of Android users are concerned about privacyGoogle’s security guidelines also drew the majority of this year’s requests in apps, according to Kaspersky’s Privacy Checker website....
Author: admin
Microsoft 365 version 2206 update pulled due to apps crashing
Microsoft 365 version 2206 update pulled due to apps crashingMicrosoft has pulled the Microsoft 365 version 2206 update after users report their Office applications are crashing...
Cisco reveals cyberattack on its corporate network
Cisco reveals cyberattack on its corporate networkThough cybercriminals have published a list of breached files, Cisco said that no sensitive customer or employee data was compromised...
CopperStealer Distributes Malicious Chromium-based Browser Extension to Steal Cryptocurrencies
CopperStealer Distributes Malicious Chromium-based Browser Extension to Steal CryptocurrenciesWe tracked the latest deployment of the group behind CopperStealer, this time stealing cryptocurrencies and users’ wallet account...
Zimbra auth bypass bug exploited to breach over 1,000 servers
Zimbra auth bypass bug exploited to breach over 1,000 serversAn authentication bypass Zimbra security vulnerability is being exploited to compromise Zimbra Collaboration Suite (ZCS) email servers worldwide....
Oil and Gas Cybersecurity: Threats Part 2
Oil and Gas Cybersecurity: Threats Part 2In part two of our oil and gas series, we look at more threats that can expose the industry to...
How credential phishing attacks threaten a host of industries and organizations
How credential phishing attacks threaten a host of industries and organizationsThe first half of 2022 saw a 48% increase in email attacks from the previous six...
2022 Threat Report
2022 Threat ReportThe BlackBerry 2022 Threat Report is not a simple retrospective of the cyberattacks of 2021. It is a high-level look at issues affecting cybersecurity...
1. Cracking the Hackers: How to Build a 100% Engaged Human Firewall
1. Cracking the Hackers: How to Build a 100% Engaged Human FirewallCritical steps for a successful cyber security awareness campaign Staff working remotely are at greater...
Ransomware Prevention and Remediation
Ransomware Prevention and RemediationWhile phishing remains the most common attack vector, threat actors have introduced tactics, techniques, and procedures that don’t require a victim to click...
US govt will pay you $10 million for info on Conti ransomware members
US govt will pay you $10 million for info on Conti ransomware membersThe U.S. State Department announced a $10 million reward today for information on five...
Microsoft shares workarounds for Outlook crashing after launch
Microsoft shares workarounds for Outlook crashing after launchMicrosoft is investigating customer reports of a known issue causing Outlook for Microsoft 365 to freeze and crash right after...
Amazon One collects handprints, privacy advocates seriously disturbed
Amazon One collects handprints, privacy advocates seriously disturbedEXECUTIVE SUMMARY: Amazon wants to read your palm – and the technology might foretell the future. Amazon, which owns...
Black Basta: New ransomware threat aiming for the big league
Black Basta: New ransomware threat aiming for the big leagueMany ransomware gangs have risen to the top over the years only to suddenly disband and be...
73 NPS—How to Get a High Net Promoter Score in Bot Protection
73 NPS—How to Get a High Net Promoter Score in Bot ProtectionDataDome's high NPS (mentioned in The Forrester Wave: Bot Management, Q2 2022) is 73—far above...
How a Venezuelan disinformation campaign swayed voters in Colombia
How a Venezuelan disinformation campaign swayed voters in ColombiaEver since the Kremlin's troll farm, the Internet Research Agency, targeted the American electorate during the 2016 U.S....
Aspen Security Forum 2022 – Moderator: David Sanger – Technology and National Security
Aspen Security Forum 2022 – Moderator: David Sanger – Technology and National SecurityJane Harman, Distinguished Fellow and President Emerita, Wilson Center Kent Walker, President, Global Affairs...
Cisco admits hack on IT network, links attacker to LAPSUS$ threat group
Cisco admits hack on IT network, links attacker to LAPSUS$ threat groupIT, networking, and cybersecurity solutions giant Cisco has admitted suffering a security incident targeting its...
Applying Identity to DevSecOps Processes
Applying Identity to DevSecOps ProcessesApplying Identity to DevSecOps Processes brooke.crothers Thu, 08/11/2022 - 12:11 5 views Identity Means Secrets You prove identity by validating credentials; secrets...
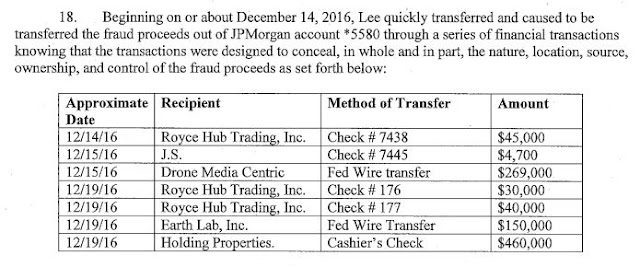
Three UK-based Nigerian BEC Scammers Used Construction Intelligence Service to Target Victims
Three UK-based Nigerian BEC Scammers Used Construction Intelligence Service to Target Victims On 10AUG2022 three Nigerians were extradited from the UK to the US to face charges...
What happened to the Lapsus$ hackers?
What happened to the Lapsus$ hackers?[Editor's note: This article originally appeared on the CSO Germany website on July 29.] Claire Tills, senior research engineer at Tenable,...
Hybrid Security Threats and Malign Influence Campaigns
Hybrid Security Threats and Malign Influence CampaignsThree key vulnerabilities to keep on the radar The post Hybrid Security Threats and Malign Influence Campaigns appeared first on...
Critical Flaws Disclosed in Device42 IT Asset Management Software
Critical Flaws Disclosed in Device42 IT Asset Management SoftwareCybersecurity researchers have disclosed multiple severe security vulnerabilities asset management platform Device42 that, if successfully exploited, could enable a malicious...
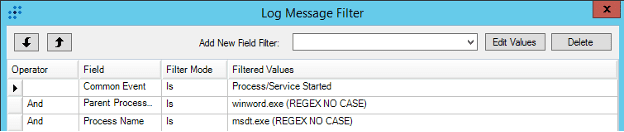
Detecting Follina (CVE-2022-30190): Microsoft Office Zero-Day Exploit
Detecting Follina (CVE-2022-30190): Microsoft Office Zero-Day ExploitFollina (CVE-2022-30190) is a Microsoft Office zero-day vulnerability that has recently been discovered. It’s a high-severity vulnerability that hackers can...
Cisco Confirms It’s Been Hacked by Yanluowang Ransomware Gang
Cisco Confirms It's Been Hacked by Yanluowang Ransomware GangNetworking equipment major Cisco on Wednesday confirmed it was the victim of a cyberattack on May 24, 2022...
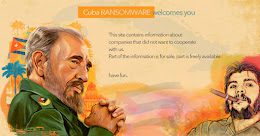
Hackers Behind Cuba Ransomware Attacks Using New RAT Malware
Hackers Behind Cuba Ransomware Attacks Using New RAT MalwareThreat actors associated with the Cuba ransomware have been linked to previously undocumented tactics, techniques and procedures (TTPs),...
Network mistakes, misconfigurations cost companies millions
Network mistakes, misconfigurations cost companies millionsNetwork misconfigurations cost companies an average of 9% of annual revenues, according to a study released Wednesday by a network security...
What the Zola Hack Can Teach Us About Password Security
What the Zola Hack Can Teach Us About Password SecurityPassword security is only as strong as the password itself. Unfortunately, we are often reminded of the...
Conti Cybercrime Cartel Using ‘BazarCall’ Phishing Attacks as Initial Attack Vector
Conti Cybercrime Cartel Using 'BazarCall' Phishing Attacks as Initial Attack VectorA trio of offshoots from the notorious Conti cybercrime cartel have resorted to the technique of...
Black Hat 2022 Trip Report
Black Hat 2022 Trip Report It felt like I had stepped out of a time machine and it was 2019. I was walking about a mile...