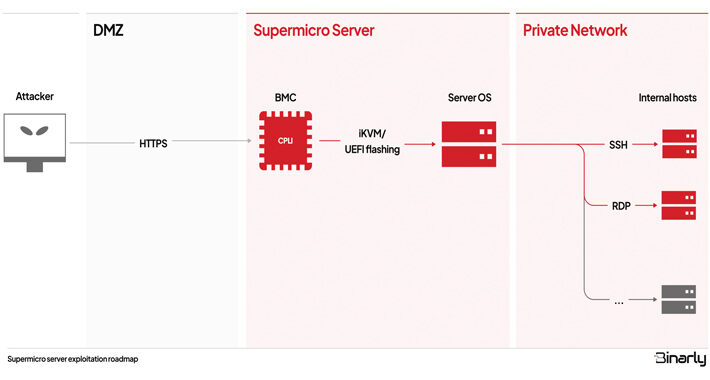
Source: thehackernews.com – Author: . Oct 06, 2023NewsroomServer Security / Vulnerability Multiple security vulnerabilities have been disclosed in the Intelligent Platform Management Interface (IPMI) firmware for...
Author: admin
QakBot Threat Actors Still in Action, Using Ransom Knight and Remcos RAT in Latest Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 05, 2023NewsroomRansomware / Malware Despite the disruption to its infrastructure, the threat actors behind the QakBot malware have been linked...
Cisco Releases Urgent Patch to Fix Critical Flaw in Emergency Responder Systems – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 05, 2023NewsroomNetwork Security / Software Patch Cisco has released updates to address a critical security flaw impacting Emergency Responder that...
Analysis and Config Extraction of Lu0Bot, a Node.js Malware with Considerable Capabilities – Source:thehackernews.com
Source: thehackernews.com – Author: . Nowadays, more malware developers are using unconventional programming languages to bypass advanced detection systems. The Node.js malware Lu0Bot is a testament...
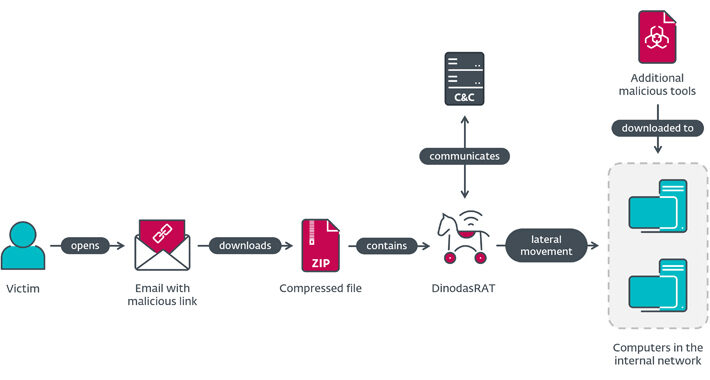
Guyana Governmental Entity Hit by DinodasRAT in Cyber Espionage Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 05, 2023NewsroomCyber Espionage / Cyber Threat A governmental entity in Guyana has been targeted as part of a cyber espionage...
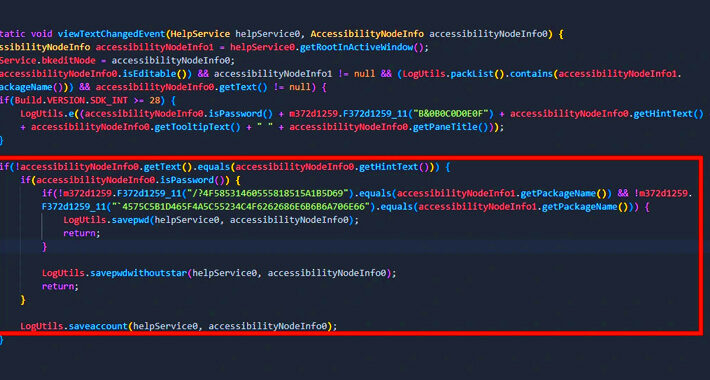
GoldDigger Android Trojan Targets Banking Apps in Asia Pacific Countries – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 05, 2023NewsroomMobile Security / crypto A new Android banking trojan named GoldDigger has been found targeting several financial applications with...
Unkillable? Qakbot Infections Fly On Even After Its High-Profile Raid – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading The Qakbot (aka Qbot) first-stage malware operation is still kicking, even after the “Operation Duck Hunt”...
Critical Zero-Day Bug in Atlassian Confluence Under Active Exploit – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading A critical privilege-escalation vulnerability in Atlassian Confluence Server and Confluence Data Center has been disclosed,...
AWS Plans Multifactor Authentication Mandates for 2024 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Amazon Web Services announced that starting mid-2024, root users of an AWS Organization account will be required...
On the Dark Web, Prices Are Down for Middle Eastern Network Access – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The cost of access to Middle East corporate networks dropped by half in a year. Users on...
‘Looney Tunables’ Bug Opens Millions of Linux Systems to Root Takeover – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Attackers can now gain root privileges on millions of Linux systems — by exploiting an easy-to-exploit, newly discovered buffer...
Turnkey Rootkit for Amateur Hackers Makes Supply Chain Attacks Easy – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Researchers have discovered a typosquatting npm package concealing a full-service Discord remote access Trojan (RAT) that...
How to Measure Patching and Remediation Performance – Source: www.darkreading.com
Source: www.darkreading.com – Author: Matt Middleton-Leal, Managing Director for EMEA North, Qualys When it comes to security, fixing problems before they are exploited is easier and...
Patch Confusion for Critical Exim Bug Puts Email Servers at Risk — Again – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading A disorderly disclosure process last week led to the release of information on six vulnerabilities in...
CISA Warns of Active Exploitation of JetBrains and Windows Vulnerabilities – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 05, 2023NewsroomVulnerability / Cyber Attack The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Wednesday added two security flaws to...
Apple Rolls Out Security Patches for Actively Exploited iOS Zero-Day Flaw – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 05, 2023NewsroomZero Day / Vulnerability Apple on Wednesday rolled out security patches to address a new zero-day flaw in iOS...
Atlassian Confluence Hit by New Actively Exploited Zero-Day – Patch Now – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 05, 2023NewsroomZero Day / Vulnerability Atlassian has released fixes to contain an actively exploited critical zero-day flaw impacting publicly accessible...
Insurance Companies Have a Lot to Lose in Cyberattacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Stephen Lawton, Contributing Writer Insurance companies have a huge target on their proverbial backs as cyber attackers increase their focus on an...
Bing Chat LLM Tricked Into Circumventing CAPTCHA Filter – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading This past week, a user on the X platform (formerly known as Twitter) devised and successfully executed...
Researchers Link DragonEgg Android Spyware to LightSpy iOS Surveillanceware – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 04, 2023THNMobile Security / Spyware New findings have identified connections between an Android spyware called DragonEgg and another sophisticated modular...
Wing Disrupts the Market by Introducing Affordable SaaS Security – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 04, 2023The Hacker NewsSaaS Security / Enterprise Security Today, mid-sized companies and their CISOs are struggling to handle the growing...
Rogue npm Package Deploys Open-Source Rootkit in New Supply Chain Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 04, 2023THNSupply Chain / Malware A new deceptive package hidden within the npm package registry has been uncovered deploying an...
Microsoft Warns of Cyber Attacks Attempting to Breach Cloud via SQL Server Instance – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 04, 2023THNCloud Security / Cyber Threat Microsoft has detailed a new campaign in which attackers unsuccessfully attempted to move laterally...
Quick Glossary: Cybersecurity Attacks – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: It doesn’t matter whether your organization is a huge multinational business enterprise or a one-person operation. At some point, your computer networks...
Looney Tunables: New Linux Flaw Enables Privilege Escalation on Major Distributions – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 04, 2023THNEndpoint Security / Vulnerability A new Linux security vulnerability dubbed Looney Tunables has been discovered in the GNU C...
Russian Hacktivism Takes a Toll on Organizations in Ukraine, EU, US – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Though sometimes they appear to be all bark and no bite, experts say Russian hacktivist groups...
Attacks on Maximum Severity WS_FTP Bug Have Been Limited — So Far – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading After an early flurry of exploit activity, attacks targeting a maximum-severity flaw that Progress Software disclosed...
USPS Anchors Snowballing Smishing Campaigns – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading A cyber campaign by threat actors targeting the US Postal Service (USPS) using smishing and phishing tactics...
Name That Edge Toon: Office Artifacts – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Klossner, Cartoonist Many companies — like, nine out of 10, according to a recent survey — are calling their employees back...
Fast-Growing Dropbox Campaign Steals Microsoft SharePoint Credentials – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Threat actors are using messages sent from Dropbox to steal Microsoft user credentials in a fast-growing business email...