Nitrokod Crypto Miner Infected Over 111,000 Users with Copies of Popular SoftwareA Turkish-speaking entity called Nitrokod has been attributed to an active cryptocurrency mining campaign that...
Author: admin
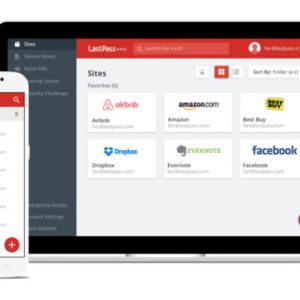
LastPass Admits Hackers Stole Source Code, Proprietary Tech Info
LastPass Admits Hackers Stole Source Code, Proprietary Tech Info The last thing any company that makes its living from security wants is a security incident, but...
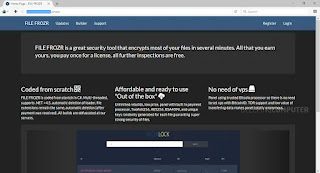
BSidesTLV 2022 – Rani Hod’s ‘How Not To Encrypt Your Files’
BSidesTLV 2022 – Rani Hod’s ‘How Not To Encrypt Your Files’Our thanks to BSidesTLV for publishing their outstanding conference videos on the organization's YouTube channel. Permalink...
Exposing a Compilation of Known Ransomware Group’s Dark Web Onion Web Sites – An OSINT Analysis
Exposing a Compilation of Known Ransomware Group’s Dark Web Onion Web Sites – An OSINT Analysis Dear blog readers, I've decided to share with everyone some...
Will Voluntary CISA Cyber Goals Be Enough to Protect Critical Infrastructure?
Will Voluntary CISA Cyber Goals Be Enough to Protect Critical Infrastructure?The Cybersecurity and Infrastructure Security Agency is getting pushback from critical infrastructure owners and operators on...
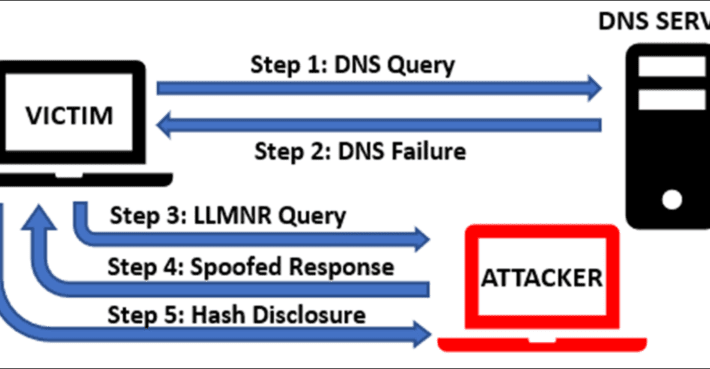
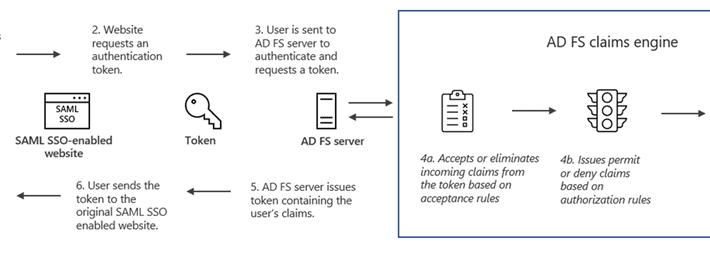
How to Prevent High Risk Authentication Coercion Vulnerabilities
How to Prevent High Risk Authentication Coercion VulnerabilitiesMost of us already know the basic principle of authentication, which, in its simplest form, helps us to identify...
BSidesTLV 2022 – Philip Tsukerman’s And Amir Kutcher’s ‘Unmasked! – Fighting Stealthy Execution Methods Using Process Creation Properties’
BSidesTLV 2022 – Philip Tsukerman’s And Amir Kutcher’s ‘Unmasked! – Fighting Stealthy Execution Methods Using Process Creation Properties’Our thanks to BSidesTLV for publishing their outstanding conference...
Key Points from the IBM Cost of a Data Breach Report 2022
Key Points from the IBM Cost of a Data Breach Report 2022The volume and impact of data breaches have accelerated largely in 2022, which has contributed...
Twilio hackers also breached the food delivery firm DoorDash
Twilio hackers also breached the food delivery firm DoorDashTwilio hackers also compromised the food delivery firm DoorDash, the attackers had access to company data, including customer...
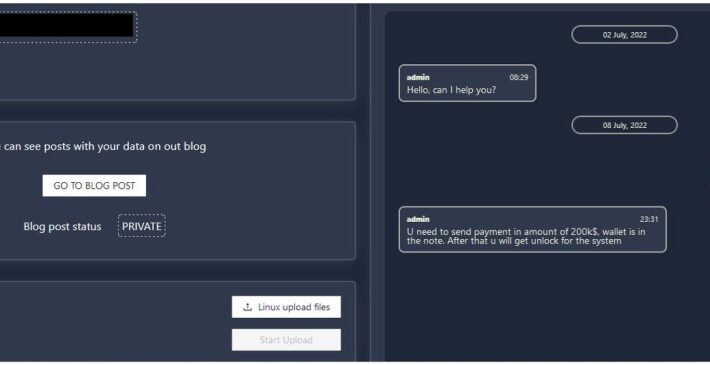
New Agenda Ransomware appears in the threat landscape
New Agenda Ransomware appears in the threat landscapeTrend Micro researchers warn of a new ransomware family called Agenda, which has been used in attacks on organizations...
Security Affairs newsletter Round 381
Security Affairs newsletter Round 381A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs free for you in...
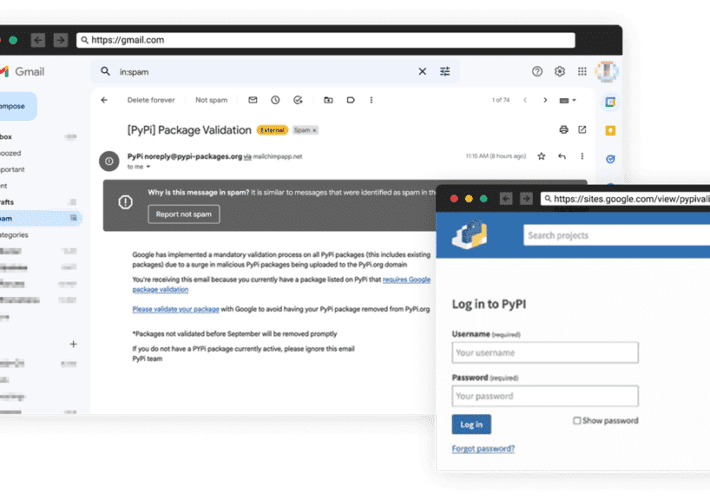
Experts warn of the first known phishing attack against PyPI
Experts warn of the first known phishing attack against PyPIThe Python Package Index (PyPI) warns of an ongoing phishing campaign to steal developer credentials and distribute...
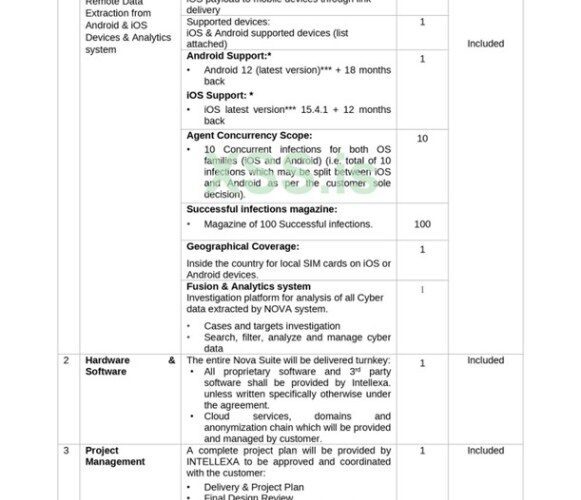
Surveillance firm’s leaked docs show the purchase of an $8M iOS RCE zero-day exploit
Surveillance firm’s leaked docs show the purchase of an $8M iOS RCE zero-day exploitLeaked documents show the surveillance firm Intellexa offering exploits for iOS and Android...
Friday Squid Blogging: 14-foot Giant Squid Washes Ashore in Cape Town
Friday Squid Blogging: 14-foot Giant Squid Washes Ashore in Cape TownIt’s an Architeuthis dux, the second this year. As usual, you can also use this squid...
How to Remove Personal Information From Data Broker Sites
How to Remove Personal Information From Data Broker Sites Data brokers are companies that collect your information from a variety of sources to sell or license...
7 Signs Your Phone Has a Virus and What You Can Do
7 Signs Your Phone Has a Virus and What You Can Do Our phones store a lot of personal data, including contacts, social media account details,...
8 Signs It May Be Time for Parental Controls
8 Signs It May Be Time for Parental Controls Equipping and guiding your digitally connected child is one of the toughest challenges you will face as...
Here’s How to Steer Clear of Bot Accounts on Social Media
Here’s How to Steer Clear of Bot Accounts on Social Media “Congratulations, you’re a winner!” “Did you know this public figure is trying to make your...
Embrace change! Chris’s McAfee Journey
Embrace change! Chris’s McAfee Journey In this career-journey series, Internal Audit Manager Chris shares his recent journey joining the McAfee finance team and why he is...
K55354030: OpenJDK vulnerabilities CVE-2021-2341, CVE-2021-2369, CVE-2021-2388, CVE-2021-2432
K55354030: OpenJDK vulnerabilities CVE-2021-2341, CVE-2021-2369, CVE-2021-2388, CVE-2021-2432OpenJDK vulnerabilities CVE-2021-2341, CVE-2021-2369, CVE-2021-2388, CVE-2021-2432 Security Advisory Security Advisory Description CVE-2021-2341 Vulnerability in the Java SE, Oracle GraalVM ......
K80970653: BIG-IP iRules vulnerability CVE-2022-33962
K80970653: BIG-IP iRules vulnerability CVE-2022-33962BIG-IP iRules vulnerability CVE-2022-33962 Security Advisory Security Advisory Description The node iRules command may allow an attacker to bypass the access control...
Extending the Zero Trust Architecture Concept to APIs
Extending the Zero Trust Architecture Concept to APIsApplication programming interfaces (APIs) are critical to modern applications. APIs are used to communicate information between users and applications,...
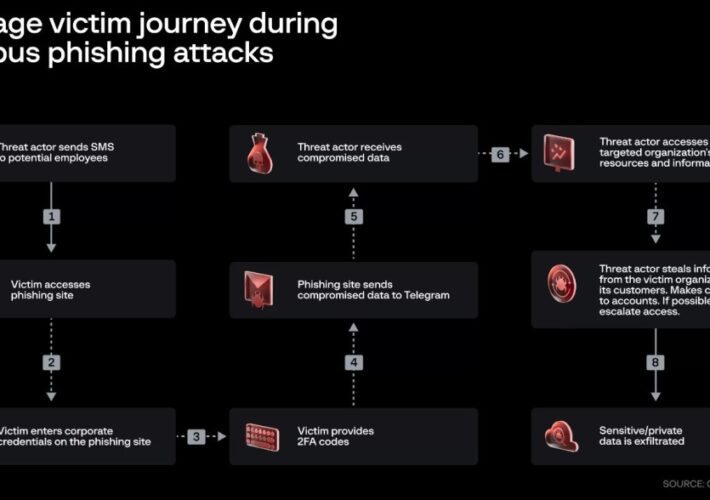
Twilio Hackers Scarf 10K Okta Credentials in Sprawling Supply-Chain Attack
Twilio Hackers Scarf 10K Okta Credentials in Sprawling Supply-Chain AttackThe "0ktapus" cyberattackers set up a well-planned spear-phishing effort that affected at least 130 orgs beyond Twilio...
Nobelium APT uses new Post-Compromise malware MagicWeb
Nobelium APT uses new Post-Compromise malware MagicWebRussia-linked APT group Nobelium is behind a new sophisticated post-exploitation malware tracked by Microsoft as MagicWeb. Microsoft security researchers discovered...
LastPass data breach: threat actors stole a portion of source code
LastPass data breach: threat actors stole a portion of source codePassword management software firm LastPass has suffered a data breach, threat actors have stole source code...
0ktapus phishing campaign: Twilio hackers targeted other 136 organizations
0ktapus phishing campaign: Twilio hackers targeted other 136 organizationsThe threat actors behind Twilio and Cloudflare attacks have been linked to a phishing campaign that targeted other 136 organizations. The...
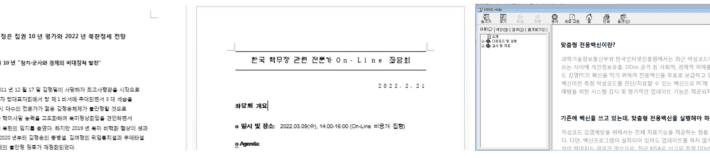
GoldDragon campaign: North-Korea linked Kimsuky APT adopts victim verification technique
GoldDragon campaign: North-Korea linked Kimsuky APT adopts victim verification techniqueThe North Korea-linked Kimsuky APT is behind a new campaign, tracked as GoldDragon, targeting political and diplomatic...
CISA Releases Guidelines to Aid Companies Transition to Post-quantum Cryptography
CISA Releases Guidelines to Aid Companies Transition to Post-quantum CryptographyThe guide provides overview of potential impacts of quantum computing on National Critical FunctionsLeer másThe guide provides...
Iran-linked Mercury APT exploited Log4Shell in SysAid Apps for initial access
Iran-linked Mercury APT exploited Log4Shell in SysAid Apps for initial accessAn Iran-linked Mercury APT group exploited the Log4Shell vulnerability in SysAid applications for initial access to...
Talos Renews Cybersecurity Support For Ukraine on Independence Day
Talos Renews Cybersecurity Support For Ukraine on Independence DayCisco and Talos both have resources available to organizations in Ukraine in need of assistanceLeer másCisco and Talos...