Hackers Use ModernLoader to Infect Systems with Stealers and CryptominersAs many as three disparate but related campaigns between March and Jun 2022 have been found to...
Author: admin
Importance of being agile & the necessary ingredients
Importance of being agile & the necessary ingredientsFraud represents an asymmetric challenge. A fast reaction time plays an important role in minimizing the attacker’s advantage and...
What is mobile security?
What is mobile security?The use of smartphones has surged, but the users’ knowledge regarding the security of mobile devices has not kept pace with this uptick....
Automatic Restoration of Corrupted UPX-packed Samples
Automatic Restoration of Corrupted UPX-packed SamplesIn this blog, we share a tool (available on Git Hub) that can automatically fix various types of tampered UPX-packed files...
Pondurance Innovations and Integrations for Cloud Security
Pondurance Innovations and Integrations for Cloud SecurityCloud computing has created the biggest tectonic shift in IT this century. It has reshaped and optimized the process of...
Educational institutions and students on hacker’s radar
Educational institutions and students on hacker’s radarOver the last two months, hackers have stepped up attacks on academic institutions and students thereby opening a new frontier...
Consistent Authentication and Device Posture policies for SaaS
Consistent Authentication and Device Posture policies for SaaSThe adoption of SaaS (Software as a Service) started as far back as the 1960s, but picked up steam...
New Golang-based ‘Agenda Ransomware’ Can Be Customized For Each Victim
New Golang-based 'Agenda Ransomware' Can Be Customized For Each VictimA new ransomware strain written in Golang dubbed "Agenda" has been spotted in the wild, targeting healthcare...
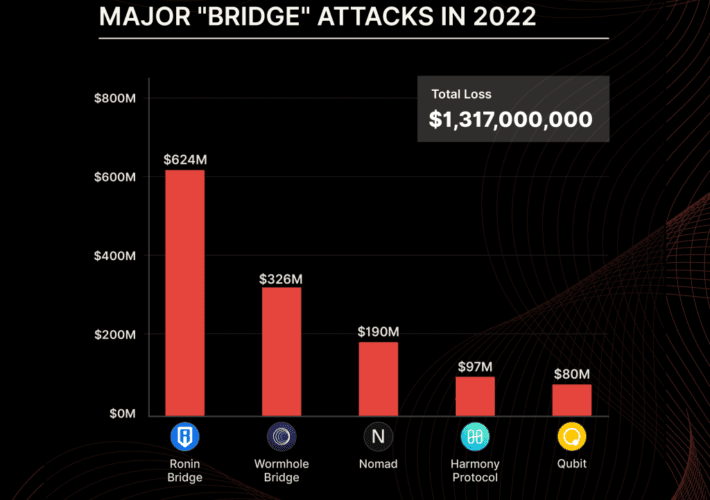
FBI Warns Investors to Take Precautions with Decentralized Financial Platforms
FBI Warns Investors to Take Precautions with Decentralized Financial PlatformsThe U.S. Federal Bureau of Investigation (FBI) on Monday warned of cyber criminals increasingly exploiting flaws in...
FTC Sues Data Broker Over Selling Location Data for Hundreds of Millions of Phones
FTC Sues Data Broker Over Selling Location Data for Hundreds of Millions of PhonesThe U.S. Federal Trade Commission (FTC) on Monday said it filed a lawsuit...
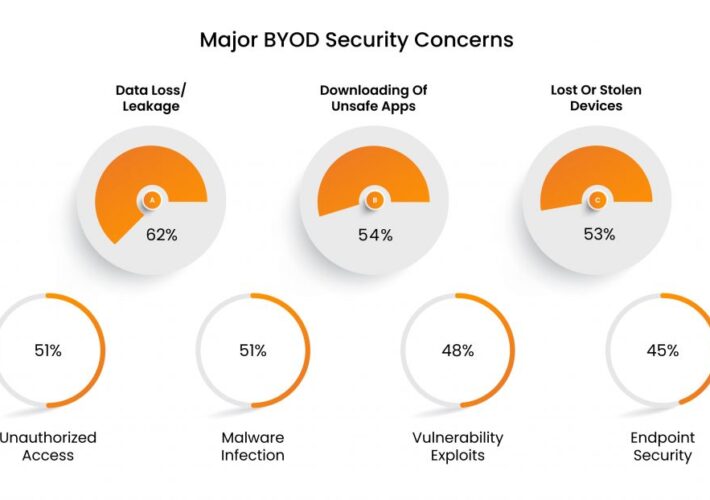
The Emergence Of BYOD: Are Personal Devices Acceptable?
The Emergence Of BYOD: Are Personal Devices Acceptable?To bring or not to ‘bring your own device’ to work, that is the question! During COVID-19, when organizations...
India’s Newest Airline Akasa Air Found Leaking Passengers’ Personal Information
India's Newest Airline Akasa Air Found Leaking Passengers' Personal InformationAkasa Air, India's newest commercial airline, exposed the personal data belonging to its customers that the company...
Forrester: CISO Budgets Not Immune to Cuts
Forrester: CISO Budgets Not Immune to Cuts With looming pullbacks in enterprise technology budgets—including, potentially, security budgets—despite rising digital attacks, regulatory pressure, increasing enterprise business-technology architectural...
LastPass source code breach – do we still recommend password managers?
LastPass source code breach – do we still recommend password managers?What does the recent LastPass breach mean for password managers? Just a bump in the road,...
Sophisticated BEC scammers bypass Microsoft 365 multi-factor authentication
Sophisticated BEC scammers bypass Microsoft 365 multi-factor authenticationBusiness email compromise (BEC) attacks, where hackers hijack finance-related email threads and trick employees into wiring money to the...
Why It’s Important to Take Notice of AWS IAM Roles Anywhere
Why It’s Important to Take Notice of AWS IAM Roles Anywhere IAM Roles Anywhere may be a pivotal moment for security; it lets you enrich the arsenal...
Confessions of a Network Engineer – Remote Access VPNs
Confessions of a Network Engineer – Remote Access VPNs In 2001, I joined a global retailer based in the Pacific Northwest as a network engineer. My...
US Cyber Command and NSA Partner On Defence Efforts For Midterms Elections
US Cyber Command and NSA Partner On Defence Efforts For Midterms ElectionsThe group's main goal is to monitor foreign adversaries who may interfere with electionsLeer másThe...
Global Ransomware Damages to Exceed $30bn by 2023
Global Ransomware Damages to Exceed $30bn by 2023Six hundred malicious email campaigns made their way across the internet in the first half of 2022Leer másSix hundred...
UK Spies Fund New Course for Female Coders
UK Spies Fund New Course for Female CodersGCHQ wants to improve diversity for better resultsLeer másGCHQ wants to improve diversity for better results
FBI: Hackers Are Exploiting DeFi Bugs to Steal Funds
FBI: Hackers Are Exploiting DeFi Bugs to Steal FundsUsers of decentralized finance platforms at riskLeer másUsers of decentralized finance platforms at risk
New Go-based Ransomware ‘Agenda’ Delivers Customized Attacks
New Go-based Ransomware 'Agenda' Delivers Customized AttacksAgenda can reboot systems in safe mode and stop many server-specific processes and servicesLeer másAgenda can reboot systems in safe...
Google Launches Major Open Source Bug Bounty Program
Google Launches Major Open Source Bug Bounty ProgramInitiative is part of $10bn commitment to improve cybersecurityLeer másInitiative is part of $10bn commitment to improve cybersecurity
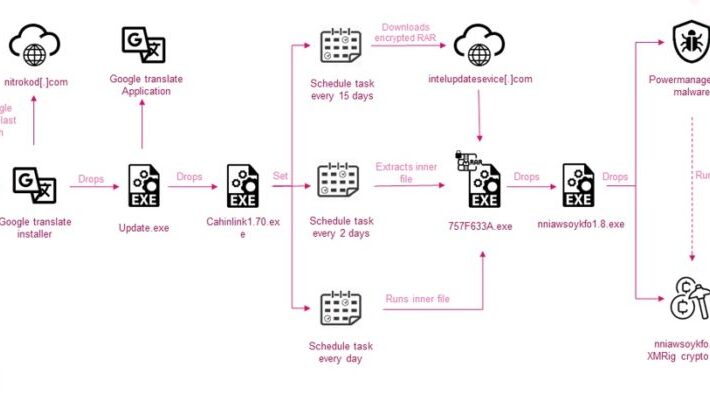
Nitrokod crypto miner infected systems across 11 countries since 2019
Nitrokod crypto miner infected systems across 11 countries since 2019Researchers spotted a Turkish-based crypto miner malware campaign, tracked as Nitrokod, which infected systems across 11 countries....
US FTC sued US data broker Kochava for selling sensitive and geolocation data
US FTC sued US data broker Kochava for selling sensitive and geolocation dataThe U.S. FTC sued US data broker Kochava for selling sensitive and precise geolocation...
Twilio breach let attackers access Authy two-factor accounts of 93 users
Twilio breach let attackers access Authy two-factor accounts of 93 usersThreat actors behind the Twilio hack also gained access to the accounts of 93 individual users...
World’s largest distributors of books Baker & Taylor hit by ransomware
World’s largest distributors of books Baker & Taylor hit by ransomwareBaker & Taylor, one of the world’s largest distributors of books, revealed that it was hit...
Crooks are increasingly targeting DeFi platforms to steal cryptocurrency
Crooks are increasingly targeting DeFi platforms to steal cryptocurrencyThe U.S. FBI warns investors that crooks are increasingly exploiting security issues in Decentralized Finance (DeFi) platforms to...
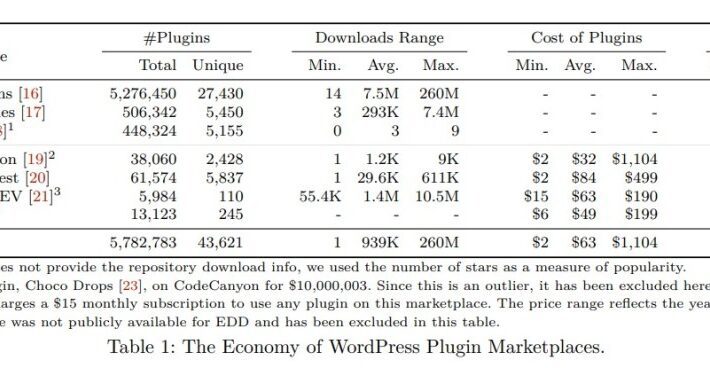
A study on malicious plugins in WordPress Marketplaces
A study on malicious plugins in WordPress MarketplacesA group of researchers from the Georgia Institute of Technology discovered malicious plugins on tens of thousands of WordPress...
LockBit Malware Group Threatens with Triple Extortion
LockBit Malware Group Threatens with Triple ExtortionLockBit ransomware gang – a ransomware operation that has been active for almost three years now listing over 700 victims...