Hackers Hide Malware in Stunning Images Taken by James Webb Space TelescopeA persistent Golang-based malware campaign dubbed GO#WEBBFUSCATOR has leveraged the deep field image taken from...
Author: admin
Back to School: 7 Top Cybersecurity Tips at this Busy Time
Back to School: 7 Top Cybersecurity Tips at this Busy Time It’s the last week of the summer holidays, and parents, kids, teens, college students... The...
Chrome patches 24 security holes, enables “Sanitizer” safety system
Chrome patches 24 security holes, enables “Sanitizer” safety system24 existing bugs fixed. And, we hope, numerous potential future bugs prevented.Leer másNaked Security24 existing bugs fixed. And,...
Unicorn? Soonicorn? Make Sure SOX ITGC is in Your Sights | anecdotes
Unicorn? Soonicorn? Make Sure SOX ITGC is in Your Sights | anecdotesIf your company is thinking about going IPO, streamlining SOX ITGC Compliance with automation should...
LastPass: When the Password Manager Gets Owned
LastPass: When the Password Manager Gets Owned The LastPass hack currently generating media attention is distressingly common. We’re told that an “unauthorized party” was somehow able...
The Exploitation of Privileged Accounts
The Exploitation of Privileged Accounts The flow of news about data breaches and ransomware attacks is relentless. Businesses of all sizes—large companies included—continue to suffer. Not only...
Cryptominer Disguised as Google Translate Targeted 11 Countries
Cryptominer Disguised as Google Translate Targeted 11 CountriesCreated by a Turkish-speaking entity, the malware claimed around 111,000 victims in 11 countriesLeer másCreated by a Turkish-speaking entity,...
Baker & Taylor’s Systems Remain Offline a Week After Ransomware Attack
Baker & Taylor's Systems Remain Offline a Week After Ransomware AttackThe company said it will proceed to restore its systems as soon as they are sanitizedLeer...
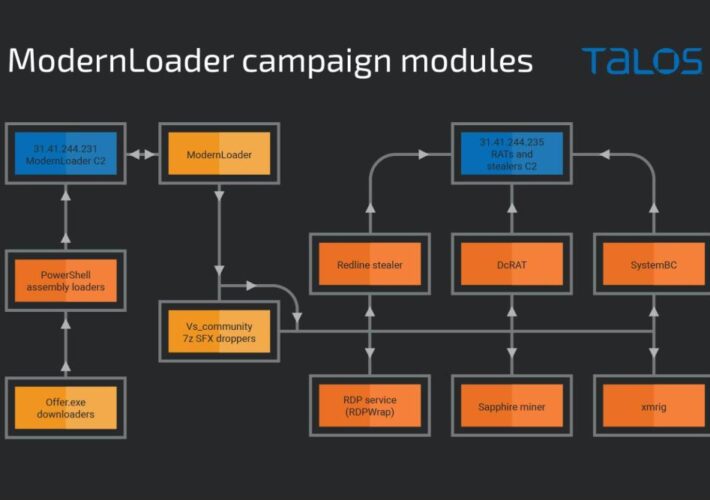
ModernLoader Delivers Stealers, Cryptominers and RATs Via Fake Amazon Gift Cards
ModernLoader Delivers Stealers, Cryptominers and RATs Via Fake Amazon Gift CardsThe association between the three apparently unrelated campaigns was made by Cisco TalosLeer másThe association between...
ICO Pursues Traffic Accident Data Thieves
ICO Pursues Traffic Accident Data ThievesData protection regulator begins criminal proceedingsLeer másData protection regulator begins criminal proceedings
TikShock: Don’t get caught out by these 5 TikTok scams
TikShock: Don’t get caught out by these 5 TikTok scamsAre you aware of the perils of the world’s no. 1 social media? Do you know how...
Ukrainian Police Bust Crypto Fraud Call Centers
Ukrainian Police Bust Crypto Fraud Call CentersScammers spoofed legitimate banks’ phone numbersLeer másScammers spoofed legitimate banks’ phone numbers
Initiative Aims to Encourage Diverse Talent into Cyber
Initiative Aims to Encourage Diverse Talent into CyberNational Cybersecurity Alliance launches HBCU career programLeer másNational Cybersecurity Alliance launches HBCU career program
Intel Selects Check Point Quantum IoT Protect for RISC-V Platform
Intel Selects Check Point Quantum IoT Protect for RISC-V PlatformIoT device manufacturers can now incorporate security at the start of the product life-cycleLeer másIoT device manufacturers...
Three campaigns delivering multiple malware, including ModernLoader and XMRig miner
Three campaigns delivering multiple malware, including ModernLoader and XMRig minerResearchers spotted three campaigns delivering multiple malware, including ModernLoader, RedLine Stealer, and cryptocurrency miners Cisco Talos researchers...
A new Google bug bounty program now covers Open Source projects
A new Google bug bounty program now covers Open Source projectsGoogle this week launched a new bug bounty program that covers the open source projects of...
Russian streaming platform Start discloses a data breach impacting 7.5M users
Russian streaming platform Start discloses a data breach impacting 7.5M usersThe Russian subscription-based streaming service Start discloses a data breach affecting 7.5 million users. The Russian...
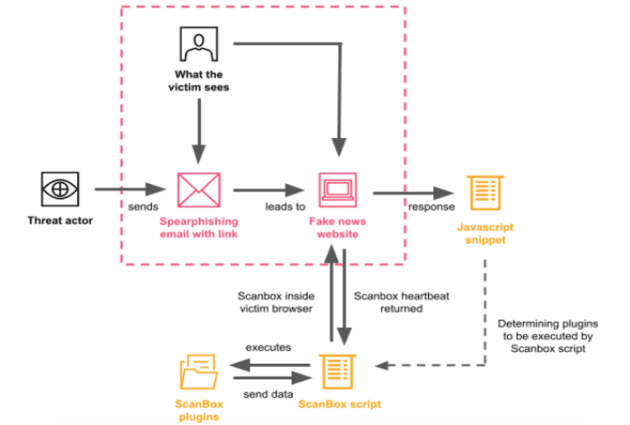
China-linked APT40 used ScanBox Framework in a long-running espionage campaign
China-linked APT40 used ScanBox Framework in a long-running espionage campaignExperts uncovered a cyber espionage campaign conducted by a China-linked APT group and aimed at several entities...
2.5M People Had Their Student Loan Accounts Data Stolen
2.5M People Had Their Student Loan Accounts Data StolenAbout 2,501,324 individuals have been affected by a breach in the network of Nelnet Servicing, a technology services...
Agenda, a New Golang Ransomware, Is on the Loose
Agenda, a New Golang Ransomware, Is on the LooseA new type of ransomware has been identified. Agenda is written in Go language (or Golang), a language...
Cyber Insurance: a fast-changing landscape
Cyber Insurance: a fast-changing landscapeFocus on the evolving cyber insurance market in Europe for businesses, and the key factors that companies looking […] The post Cyber...
HYPERSCRAPE Detection: Iranian Cyberespionage Group APT35 Uses a Custom Tool to Steal User Data
HYPERSCRAPE Detection: Iranian Cyberespionage Group APT35 Uses a Custom Tool to Steal User Data The malicious campaigns of the Iran-backed APT34 hacking collective also tracked as...
MagicWeb Detection: NOBELIUM APT Uses Sophisticated Authentication Bypass
MagicWeb Detection: NOBELIUM APT Uses Sophisticated Authentication Bypass A notorious APT group tracked as NOBELIUM (aka APT29, Cozy Bear, and The Dukes) adds new threats to...
High-School Graduation Prank Hack
High-School Graduation Prank HackThis is a fun story, detailing the hack a group of high school students perpetrated against an Illinois school district, hacking 500 screens...
How 1-Time Passcodes Became a Corporate Liability
How 1-Time Passcodes Became a Corporate LiabilityPhishers are enjoying remarkable success using text messages to steal remote access credentials and one-time passcodes from employees at some...
Privacy, please! Why a VPN on your smartphone may be a smart move for you.
Privacy, please! Why a VPN on your smartphone may be a smart move for you. Using a VPN on your smartphone can boost your privacy in...
Malicious Cookie Stuffing Chrome Extensions with 1.4 Million Users
Malicious Cookie Stuffing Chrome Extensions with 1.4 Million Users Authored by Oliver Devane and Vallabh Chole A few months ago, we blogged about malicious extensions redirecting...
Our Quest: Advancing Product Labels to Help Consumers Consider Cybersecurity
Our Quest: Advancing Product Labels to Help Consumers Consider CybersecurityFor many decades, consumers have relied on labels to help them make decisions about which products to...
US govt sues Kochava for selling sensitive geolocation data
US govt sues Kochava for selling sensitive geolocation dataThe U.S. Federal Trade Commission (FTC) announced today that it filed a lawsuit against Idaho-based location data broker...
Pirate sites ban in Austria took down Cloudflare CDNs by mistake
Pirate sites ban in Austria took down Cloudflare CDNs by mistakeExcessive and indiscriminate blocking is underway in Austria, with internet service providers (ISPs) complying to a...