The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Author: admin
The Cyber Dimensions of the Russia-Ukraine War by European Cyber Conflict Research Initiative (ECCRI).
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Quality Assurance for Software Development Must Include Cybersecurity – Why Cybersecurity and Software Quality Assurance Go Together ? by Anish Roy
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Are Quality and Security Synonymous in Software by Zeronorth
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Phishing Dark Waters – The Offensive and Defensive Sides of Maliciosus Emails
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
OWASP PRO Active Controls for Developers v. 3 – Securing Coding Best Practices – 10 Critical Security Areas where developers must know and follow the recommendatios mandatory
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Perfect Weapon – WAR, SABOTAGE and FEAR in the Cyber Age by David E. Sanger
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
TESLA Cars Cyber Security – Threats Vulnerabilities Hacking Protection by Dror Amrami
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Security Implications of ChatGPT RC by Cloud Security Alliance – CSA
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
New to Cyber Field Manaul – The Ultimate Guide to Getting Into Cybersecurity by SANS GIAC
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Hacking Connected Cars – Tactics, Techniques and Procedures by Alissa Knight – Wiley
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Complete Guide to Understanding Apple Mac Security for Enterprise by SentinelOne
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity Preparedness in Critical Infraestructure – Avoinding The Big Shutdown
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity and the role of the Board of Directors in Latin America and the Caribbean – ECLAC
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Security Incident Information Management Handbook
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CISO PLAYBOOK – Protecting The Crown Jewels by Cyber Leadership Institute – Building a cyber security strategy around high value digital assets
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cyber Threat “Info Stealer” explained in Simple way: A mallware and set of techniques used by attackers to steal your confidential information !!! and much more that you should know By Marcos Jaimovich.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Introduction to Artificial Intelligence for Security Professionals free e-book by the Cylance Data Science Team – Apply Artificial Intelligence to Information Security Problems.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
TOP 250 MSSPs 2022 edition by MSSP Alert – A CyberRisk Alliance Resource
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
North Korea’s Lazarus Group Launders $900 Million in Cryptocurrency – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 06, 2023NewsroomCyber Crime / Cryptocurrency As much as $7 billion in cryptocurrency has been illicitly laundered through cross-chain crime, with...
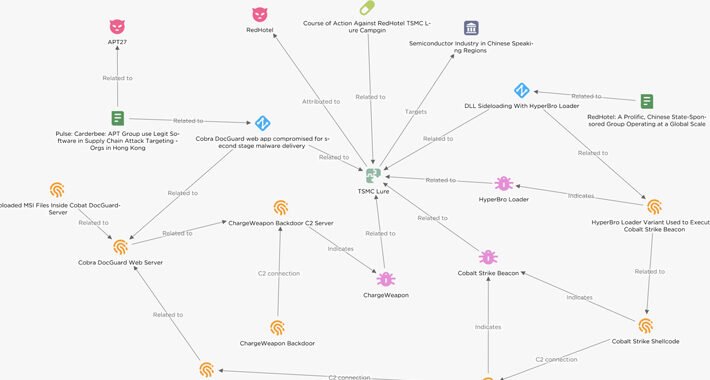
Chinese Hackers Target Semiconductor Firms in East Asia with Cobalt Strike – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 06, 2023NewsroomCyber Attack / Malware Threat actors have been observed targeting semiconductor companies in East Asia with lures masquerading as...
‘Operation Jacana’ Reveals DinodasRAT Custom Backdoor – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading A fresh malware threat dubbed “DinodasRAT” has been uncovered, after being used in a targeted...
Legions of Critical Infrastructure Devices Subject to Cyber Targeting – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading There are at least 100,000 industrial control systems (ICS) exposed to the public Internet around...
10 Routine Security Gaffes the Feds Are Begging You to Fix – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The National Security Agency (NSA) and Cybersecurity and Infrastructure Security Agency (CISA) have issued a plea to...
Madagascar Drops Predator Spyware on Citizens in Watering Hole Attack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Madagascar’s government services — such as police or domestic intelligence — have apparently purchased and leveraged Predator...
Group-IB: ‘GoldDigger’ Banking Trojan Targets Vietnamese Organizations – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Group-IB discovered an Android Trojan in August targeting more than 50 financial organizations in Vietnam that it’s...
Stealthy, Thieving Python Packages Slither Onto Windows Systems – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading A threat actor has been delivering a “relentless campaign” since early April to seed the software supply...
Critical ‘ShellTorch’ Flaws Light Up Open Source AI Users, Like Google – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading A newly discovered set of critical vulnerabilities in a machine learning framework known as TorchServe could allow...
New OS Tool Tells You Who Has Access to What Data – Source:thehackernews.com
Source: thehackernews.com – Author: . Ensuring sensitive data remains confidential, protected from unauthorized access, and compliant with data privacy regulations is paramount. Data breaches result in...
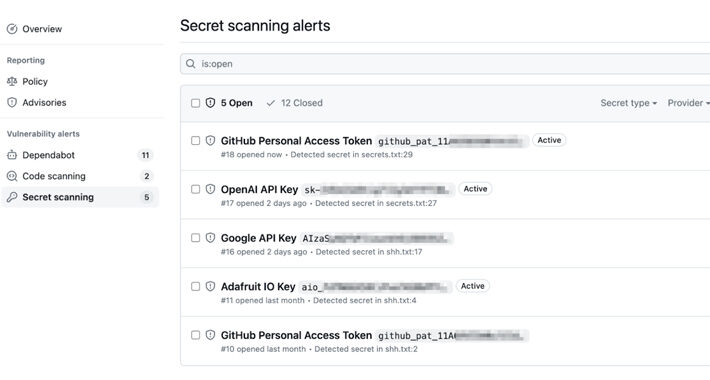
GitHub’s Secret Scanning Feature Now Covers AWS, Microsoft, Google, and Slack – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 06, 2023NewsroomProgramming / Software Security GitHub has announced an improvement to its secret scanning feature that extends validity checks to...