Ragnar Locker Ransomware Targets Energy Sector, Cybereason SuggestsThe malware can also check if specific products are installed, particularly security softwareLeer másThe malware can also check if...
Author: admin
Peter Eckersley, co-creator of Let’s Encrypt, dies at just 43
Peter Eckersley, co-creator of Let’s Encrypt, dies at just 43This site, like millions of others, has a certificate from Let's Encrypt. Farewell, Peter Eckersley, PhD, who...
S3 Ep98: The LastPass saga – should we stop using password managers? [Audio + Text]
S3 Ep98: The LastPass saga – should we stop using password managers? [Audio + Text]Latest episode - listen now!Leer másNaked SecurityLatest episode - listen now!
Source Code of Over 1800 Android and iOS Apps Gives Access to AWS Credentials
Source Code of Over 1800 Android and iOS Apps Gives Access to AWS CredentialsRoughly 50% of all the apps analyzed were seen using the same AWS...
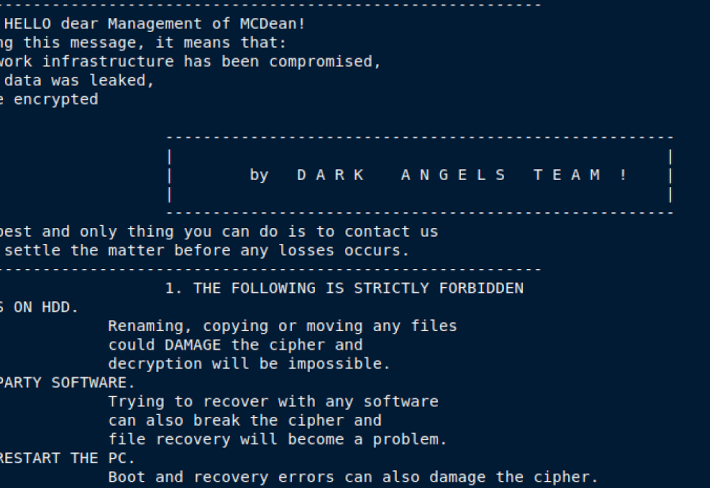
Chile and Montenegro Floored by Ransomware
Chile and Montenegro Floored by RansomwareGovernments reveal system compromise in separate incidentsLeer másGovernments reveal system compromise in separate incidents
NATO Countries Hit With Unprecedented Cyber Attacks
NATO Countries Hit With Unprecedented Cyber AttacksMontenegro, Estonia and new NATO applicant Finland are just three of the countries being hit hard by sophisticated cyber attacks....
UK Government Releases New AI Security Guidance
UK Government Releases New AI Security GuidanceNew principles set to take on adversarial machine learningLeer másNew principles set to take on adversarial machine learning
CISA, NSA and npm Release Software Supply Chain Guidance
CISA, NSA and npm Release Software Supply Chain GuidanceBest practices are designed to help developers bolster securityLeer másBest practices are designed to help developers bolster security
New Ransomware Group BianLian Activity Exploding
New Ransomware Group BianLian Activity ExplodingThe threat actor using the common Go programming language and a custom toolkit claims twenty victimsLeer másThe threat actor using the...
Will cyber‑insurance pay out? – Week in security with Tony Anscombe
Will cyber‑insurance pay out? – Week in security with Tony AnscombeWhat if your organization is hit by a cyberattack that is attributed to a nation state?...
Attack infrastructure used in Cisco hack linked to Evil Corp affiliate
Attack infrastructure used in Cisco hack linked to Evil Corp affiliateResearchers discovered that the infrastructure used in Cisco hack was the same used to target a...
JuiceLedger Hacker Linked to First Phishing Campaign Targeting PyPI Users
JuiceLedger Hacker Linked to First Phishing Campaign Targeting PyPI UsersJuiceLedger started poisoning open-source packages as a way to target a wider audience in AugustLeer másJuiceLedger started...
Google Chrome Vulnerability Lets Sites Quietly Overwrite Clipboard Contents
Google Chrome Vulnerability Lets Sites Quietly Overwrite Clipboard ContentsThe bug was discovered by developer Jeff Johnson, who detailed his findings in a blog postLeer másThe bug...
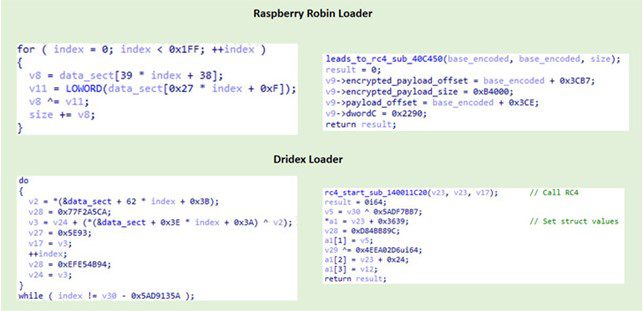
Experts link Raspberry Robin Malware to Evil Corp cybercrime gang
Experts link Raspberry Robin Malware to Evil Corp cybercrime gangResearchers attribute the Raspberry Robin malware to the Russian cybercrime group known as Evil Corp group. IBM...
Google Chrome issue allows overwriting the clipboard content
Google Chrome issue allows overwriting the clipboard contentA security issue in the Google Chrome browser could allow malicious web pages to automatically overwrite clipboard content. A...
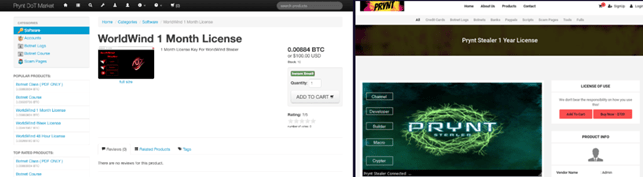
The Prynt Stealer malware contains a secret backdoor. Crooks steal data from other cybercriminals
The Prynt Stealer malware contains a secret backdoor. Crooks steal data from other cybercriminalsThe information-stealing malware Prynt Stealer contains a backdoor that allows stealing the data...
US Police Deployed Obscure Smartphone Tracking Tool With No Warrants
US Police Deployed Obscure Smartphone Tracking Tool With No WarrantsIt would allow police to search billions of mobile device-based records, including GPS dataLeer másIt would allow...
Another Ransomware For Linux Likely In Development
Another Ransomware For Linux Likely In DevelopmentUptycs researchers recently spotted a new Linux ransomware that appears to be under active development. The Uptycs Threat Research team...
Google rolled out emergency fixes to address actively exploited Chrome zero-day
Google rolled out emergency fixes to address actively exploited Chrome zero-dayGoogle rolled out emergency fixes to address a vulnerability in the Chrome web browser that is...
Samsung discloses a second data breach this year
Samsung discloses a second data breach this yearElectronics giant Samsung has confirmed a new data breach after some of its US systems were compromised in July....
Security Affairs newsletter Round 382
Security Affairs newsletter Round 382A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs free for you in...
IRS mistakenly published confidential info for roughly 120K taxpayers
IRS mistakenly published confidential info for roughly 120K taxpayersThe Internal Revenue Service (IRS) mistakenly leaked confidential information for approximately 120,000 taxpayers. Bad news for approximately 120,000...
Alleged Iranian threat actors leak the code of their CodeRAT malware
Alleged Iranian threat actors leak the code of their CodeRAT malwareThe author of the remote access trojan (RAT) CodeRAT has leaked the source code of its...
A New Cyberattack on TAP Air Portugal
A New Cyberattack on TAP Air PortugalOn Thursday night, August 25, TAP Air Portugal was the victim of a cyberattack claimed by the Ragnar Locker ransomware...
Weekly Update 311
Weekly Update 311Well, after a crazy amount of work, a lot of edits, reflection, and feedback cycles, "Pwned" is almost here: This better be a sizzling...
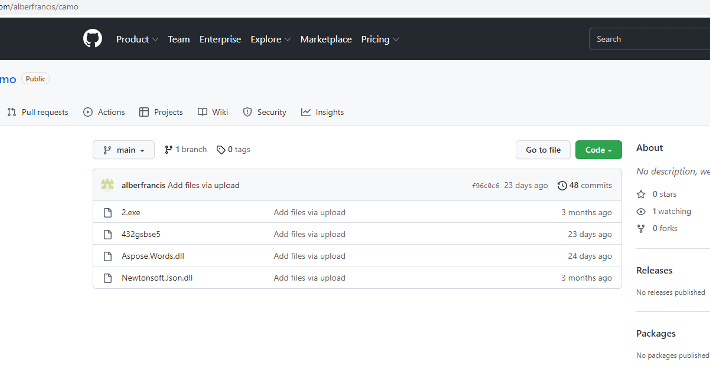
AgentTesla Spyware Massively Distributed in Phishing Campaigns Targeting Ukrainian, Austrian, and German Organizations
AgentTesla Spyware Massively Distributed in Phishing Campaigns Targeting Ukrainian, Austrian, and German Organizations On August 30 and 31, 2022, CERT-UA revealed a burst of adversary activity...
Linux Systems Are a More Common Target as the Attack Surface Expands
Linux Systems Are a More Common Target as the Attack Surface ExpandsOften overlooked by security experts, Linux systems become a more common target for cybercriminals. Aiming...
Anomaly Detection In Cybersecurity For Dummies
Anomaly Detection In Cybersecurity For DummiesThe pandemic has changed the way businesses operate, and one of these changes is that companies across the […] The post...
Source Code Protection Market
Source Code Protection MarketDo we need backup software for DevOps ecosystems? By Marta Przybylska, Marketing Manager, GitProtect.io / Xopero Software […] The post Source Code...
EVERYONE is Part of the Security Team and Solution
EVERYONE is Part of the Security Team and SolutionBy Jim Nitterauer, Director of Information Security, Graylog Often, companies approach cybersecurity as a technology problem, forgetting that...