OpenSSF releases npm best practices to help developers tackle open-source dependency risksThe Open Source Security Foundation (OpenSSF) has released the npm Best Practices Guide to help...
Author: admin
Top 12 managed detection and response solutions
Top 12 managed detection and response solutionsOf all foundational elements for information security, logging requires far more care and feeding than its fellow cornerstones such as...
How Azure Active Directory opens new authentication risks
How Azure Active Directory opens new authentication risksIt's been common knowledge for years that local Windows Active Directory networks are vulnerable to NTLM relay and pass-the-hash...
Samsung reports second data breach in 6 months
Samsung reports second data breach in 6 monthsSamsung has opened up about a data breach it detected on or around August 4, affecting the personal information...
The Heartbleed bug: How a flaw in OpenSSL caused a security crisis
The Heartbleed bug: How a flaw in OpenSSL caused a security crisisWhat is Heartbleed? Heartbleed is a vulnerability in OpenSSL that came to light in April...
‘DangerousSavanna’ Hackers Targeted Financial Institutions in Africa For Two Years
'DangerousSavanna' Hackers Targeted Financial Institutions in Africa For Two YearsThe campaign relied on spearphishing techniques to initiate infection chainsLeer másThe campaign relied on spearphishing techniques to...
Ukraine Shutters Two More Russian Bot Farms
Ukraine Shutters Two More Russian Bot FarmsFacilities used to spread Russian disinformationLeer másFacilities used to spread Russian disinformation
NATO-Member Albania Cut Ties With Iran Over Cyber-Attack
NATO-Member Albania Cut Ties With Iran Over Cyber-AttackTehran denied any link, claiming Tirana’s action was “based on such baseless claims”Leer másTehran denied any link, claiming Tirana’s...
The North Face Warns of Major Credential Stuffing Campaign
The North Face Warns of Major Credential Stuffing CampaignApparel giant detects unusual activity on accountsLeer másApparel giant detects unusual activity on accounts
Ransomware attacks on retailers rose 75% in 2021
Ransomware attacks on retailers rose 75% in 2021Retailers are fast becoming the favorite targets for ransomware criminals, with two out of three companies in the sector...
A Pocket Guide to FAIR
A Pocket Guide to FAIR FAIR, short for Factor Analysis of Information Risk, is a risk quantification methodology founded to help businesses evaluate information risks. FAIR...
North Korean state-sponsored hacker group Lazarus adds new RAT to its malware toolset
North Korean state-sponsored hacker group Lazarus adds new RAT to its malware toolsetSecurity researchers have discovered a new remote access Trojan (RAT) being used in attack...
Researchers Reveal New Iranian Threat Group APT42
Researchers Reveal New Iranian Threat Group APT42Group has been active since at least 2015Leer másGroup has been active since at least 2015
How Governments Request Your Data From Service Providers
How Governments Request Your Data From Service Providers A recently-released Surfshark report looked into global inquiries into the activities of specific accounts made by governments to...
Darktrace’s Share Value Plummets as Thoma Bravo Buyout Falls Through
Darktrace's Share Value Plummets as Thoma Bravo Buyout Falls ThroughThe buyout fell through hours before the UK company said that millions of pounds in revenue had...
Ransomware Campaigns Linked to Iranian Govt’s DEV-0270 Hackers
Ransomware Campaigns Linked to Iranian Govt's DEV-0270 HackersDEV-0270 leverages exploits for newly disclosed vulnerabilities to gain access to devicesLeer másDEV-0270 leverages exploits for newly disclosed vulnerabilities...
Over 10% of Enterprise IT Assets Found Missing Endpoint Protection
Over 10% of Enterprise IT Assets Found Missing Endpoint ProtectionThe document analyzes data aggregated from visibility into more than 500,000 IT assetsLeer másThe document analyzes data...
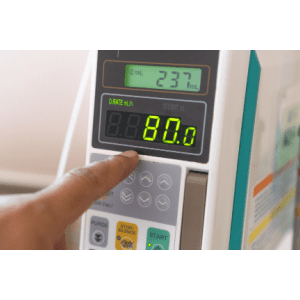
Rapid7 Discusses SIGMA Spectrum Infusion Pump and WiFi Battery Vulnerabilities
Rapid7 Discusses SIGMA Spectrum Infusion Pump and WiFi Battery VulnerabilitiesThe vulnerabilities, now fixed, allowed for a potential man in the middle attackLeer másThe vulnerabilities, now fixed,...
Toys behaving badly: How parents can protect their family from IoT threats
Toys behaving badly: How parents can protect their family from IoT threatsIt pays to do some research before taking a leap into the world of internet-connected...
Classified NATO documents sold on darkweb after they were stolen from Portugal
Classified NATO documents sold on darkweb after they were stolen from PortugalThreat actors claimed to have stolen classified NATO documents from the Armed Forces General Staff...
Our Statement of Condolence – Queen Elizabeth II – 1926 – 2022
Our Statement of Condolence - Queen Elizabeth II - 1926 - 2022We are deeply saddened by the passing of Her Majesty Queen Elizabeth II. We send...
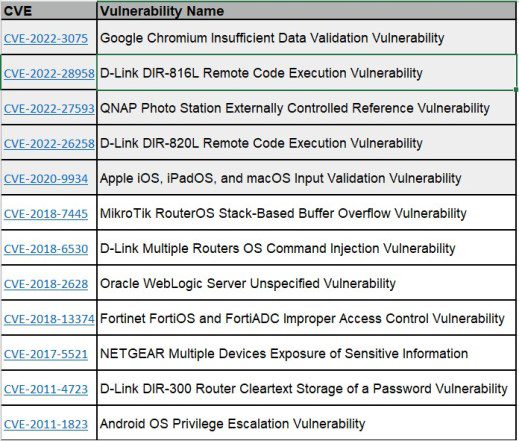
CISA adds 12 new flaws to its Known Exploited Vulnerabilities Catalog
CISA adds 12 new flaws to its Known Exploited Vulnerabilities CatalogCISA added 12 more security flaws to its Known Exploited Vulnerabilities Catalog including four D-Link vulnerabilities. The...
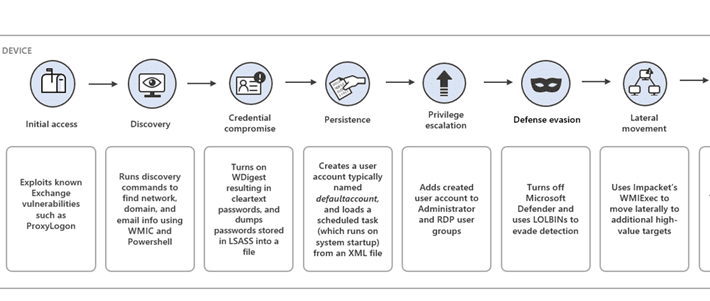
Iran-linked DEV-0270 group abuses BitLocker to encrypt victims’ devices
Iran-linked DEV-0270 group abuses BitLocker to encrypt victims’ devicesIran-linked APT group DEV-0270 (aka Nemesis Kitten) is abusing the BitLocker Windows feature to encrypt victims’ devices. Microsoft...
Experts warn of attacks exploiting zero-day in WordPress BackupBuddy plugin
Experts warn of attacks exploiting zero-day in WordPress BackupBuddy pluginThreat actors are exploiting a zero-day vulnerability in a WordPress plugin called BackupBuddy, Wordfence researchers warned. On September...
How To Design and Build Longer Lasting Drones
How To Design and Build Longer Lasting DronesOvercoming the limitations inherent in drone technology By Shaun Passley, Founder, Zenadrone Drones work. From search and rescue […]...
How To Increase User and Executive Participation In Security Awareness Training Programs
How To Increase User and Executive Participation In Security Awareness Training ProgramsBy Theo Zafirakos, CISO, Terranova Security The universal participation of an organization’s employees in security...
ZTNA and the Distributed Workforce: Hype vs. Reality
ZTNA and the Distributed Workforce: Hype vs. RealityBy Timothy Liu, CTO & Co-Founder, Hillstone Networks ZTNA, or zero-trust network access, seems to be one of […]...
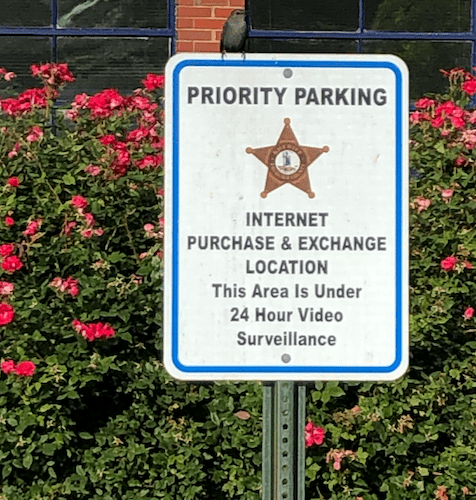
Transacting in Person with Strangers from the Internet
Transacting in Person with Strangers from the InternetCommunities like Craigslist, OfferUp, Facebook Marketplace and others are great for finding low- or no-cost stuff that one can...
Summertime Blues: TA558 Ramps Up Attacks on Hospitality, Travel Sectors
Summertime Blues: TA558 Ramps Up Attacks on Hospitality, Travel SectorsContenido de la entradaLeer másProofpoint News Feed
Our Quest: Advancing Product Labels to Help Consumers Consider Cybersecurity
Our Quest: Advancing Product Labels to Help Consumers Consider CybersecurityFor many decades, consumers have relied on labels to help them make decisions about which products to...