Weekly Update 314Wow, what a week! Of course there's lots of cyber / tech stuff in this week's update, but it was really only the embedded...
Author: admin
Building A Layered Plan for Battling Cybercrime
Building A Layered Plan for Battling CybercrimeBy Kimberly White, Senior Director, Fraud and Identity, LexisNexis® Risk Solutions As interactions with customers evolve over time, […] The...
“Fake crypto millionaire” charged with alleged $1.7M cryptomining scam
“Fake crypto millionaire” charged with alleged $1.7M cryptomining scamA self-proclaimed cryptocurrency millionaire has been charged with multiple felonies for his alleged role in a scam that...
Prompt Injection/Extraction Attacks against AI Systems
Prompt Injection/Extraction Attacks against AI SystemsThis is an interesting attack I had not previously considered. The variants are interesting, and I think we’re just starting to...
Oxford teen arrested in UK on suspicion of hacking
Oxford teen arrested in UK on suspicion of hackingThe boy, who has not been named, was arrested as part of an investigation by the National Crime...
Leaking Screen Information on Zoom Calls through Reflections in Eyeglasses
Leaking Screen Information on Zoom Calls through Reflections in EyeglassesOkay, it’s an obscure threat. But people are researching it: Our models and experimental results in a...
Friday Squid Blogging: Another Giant Squid Washes Up on New Zealand Beach
Friday Squid Blogging: Another Giant Squid Washes Up on New Zealand BeachThis one has chewed-up tentacles. (Note that this is a different squid than the one...
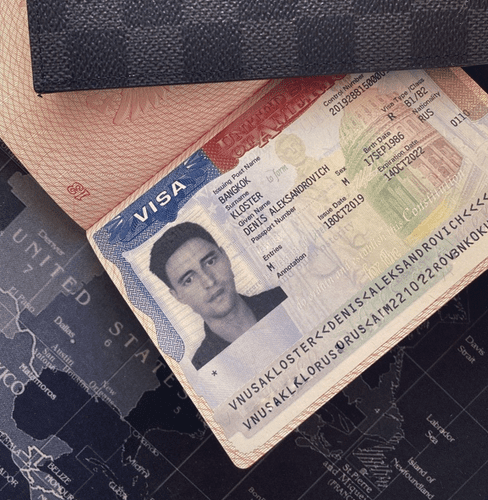
Accused Russian RSOCKS Botmaster Arrested, Requests Extradition to U.S.
Accused Russian RSOCKS Botmaster Arrested, Requests Extradition to U.S.A 36-year-old Russian man recently identified by KrebsOnSecurity as the likely proprietor of the massive RSOCKS botnet has...
The top 20 cyber security movers and shakers 2022
The top 20 cyber security movers and shakers 2022Cyber Security Hub’s inaugural power list is live, profiling the achievements from cyber security leaders at Microsoft, Visa,...
How Often Should You Change Your Passwords?
How Often Should You Change Your Passwords? When it comes to passwords, most of us would love nothing more than to set it and forget it....
Protect Your Social Media Accounts from Hacks and Attacks
Protect Your Social Media Accounts from Hacks and Attacks Here’s to the hashtags, the likes, the followers, the DMs, and the LOLs—June 30th marks Social Media Day, a...
Windows 11 now warns when typing your password in Notepad, websites
Windows 11 now warns when typing your password in Notepad, websitesWindows 11 22H2 was just released, and with it comes a new security feature called Enhanced...
8 mistakes CIOs make and how to avoid them
8 mistakes CIOs make and how to avoid themFrom driving transformative change, to sharing insights into the political nature of the role, IT leaders and advisors...
Real Estate Phish Swallows 1,000s of Microsoft 365 Credentials
Real Estate Phish Swallows 1,000s of Microsoft 365 CredentialsContenido de la entradaLeer másProofpoint News Feed
Uber Ex-CSO’s Trial: Who’s Responsible for Breach Reporting?
Uber Ex-CSO's Trial: Who's Responsible for Breach Reporting?While Joe Sullivan Is Accused of Perpetrating Cover-Up, Where Should the Buck Stop?Should the now-former CSO of Uber have...
It’s 2022. Do You Know Where Your Old Hard Drives Are?
It's 2022. Do You Know Where Your Old Hard Drives Are?The latest edition of the ISMG Security Report discusses financial giant Morgan Stanley's failure to invest...
K28942395: OpenSSH vulnerability CVE-2018-15473
K28942395: OpenSSH vulnerability CVE-2018-15473OpenSSH vulnerability CVE-2018-15473 Security Advisory Security Advisory Description OpenSSH through 7.7 is prone to a user enumeration vulnerability due to not delaying bailout...
Malicious Apps With Millions of Downloads Found in Apple App Store, Google Play
Malicious Apps With Millions of Downloads Found in Apple App Store, Google PlayThe ongoing ad fraud campaign can be traced back to 2019, but recently expanded...
AFP investigates $1m ransom demand posted online for allegedly hacked Optus data
AFP investigates $1m ransom demand posted online for allegedly hacked Optus dataAttorney general Mark Dreyfus has been briefed by the privacy commissioner about hack and is...
App Developers Increasingly Targeted via Slack, DevOps Tools
App Developers Increasingly Targeted via Slack, DevOps ToolsSlack, Docker, Kubernetes, and other applications that allow developers to collaborate have become the latest vector for software supply...
The Evolution of the Chromeloader Malware
The Evolution of the Chromeloader MalwareExecutive Summary ChromeLoader proves to be an extremely prevalent and persistent malware. It initially drops as an .iso and can be...
Threat Research: New Method of Volume Shadow Backup Deletion Seen in Recent Ransomware
Threat Research: New Method of Volume Shadow Backup Deletion Seen in Recent RansomwareVMware Threat Analysis Unit (TAU) researchers have recently observed a new technique for the...
Webinar | Top AD Exploits and How to Effectively Mitigate Them.
Webinar | Top AD Exploits and How to Effectively Mitigate Them.Contenido de la entradaLeer másDataBreachToday.com RSS Syndication
Threat Report: Illuminating Volume Shadow Deletion
Threat Report: Illuminating Volume Shadow DeletionExecutive Summary Ransomware is one of the greatest threats to all industries. Threat actors have the ability to severely hinder, or...
K28942395: OpenSSH vulnerability CVE-2018-15473
K28942395: OpenSSH vulnerability CVE-2018-15473OpenSSH vulnerability CVE-2018-15473 Security Advisory Security Advisory Description OpenSSH through 7.7 is prone to a user enumeration vulnerability due to not delaying bailout...
OnDemand I Business Keynote: Design your Multi-Cloud Strategy for freedom of Choice
OnDemand I Business Keynote: Design your Multi-Cloud Strategy for freedom of ChoiceAccelerate your digital transformation!Watch this videocast to know more about being in control of your...
OnDemand Fire Side Chat I Multicloud Success Stories
OnDemand Fire Side Chat I Multicloud Success StoriesWatch this videocast to hear real life success stories and complete journey to multicloud.Leer másDataBreachToday.com RSS SyndicationWatch this videocast...
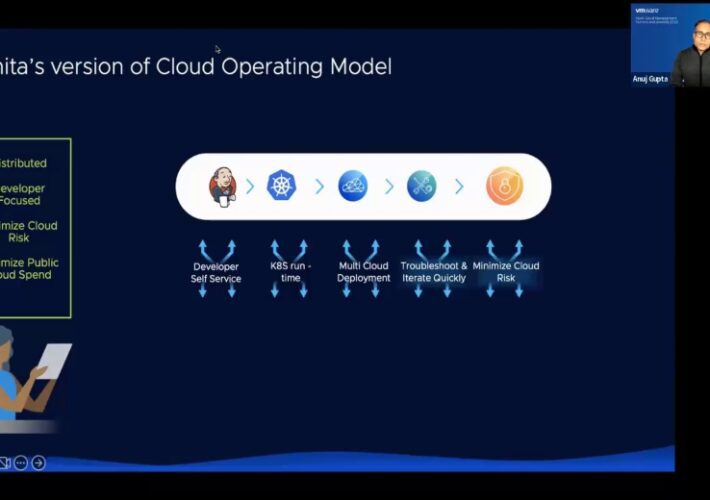
OnDemand Technical Keynote: How to build your own personified Cloud Operating Model
OnDemand Technical Keynote: How to build your own personified Cloud Operating ModelAccelerate your digital transformation!Leer másDataBreachToday.com RSS SyndicationAccelerate your digital transformation!
OnDemand VMware Power Demo: Cloud Operating Model to Simplify , Optimize & Secure your Multi Cloud Consumption
OnDemand VMware Power Demo: Cloud Operating Model to Simplify , Optimize & Secure your Multi Cloud ConsumptionAccelerate your digital transformation!Leer másDataBreachToday.com RSS SyndicationAccelerate your digital transformation!
HIVE Ransomware Claims Responsibility for NYRA Attack
HIVE Ransomware Claims Responsibility for NYRA AttackThe New York Racing Association disclosed that, on June 30th, a cyberattack impacted IT operations, website availability, and compromised member...