Teen hacking suspect charged with computer misuse and breach of bail conditionsCould the 16-year-old arrested in Oxford in March now be the 17-year-old arrested in Oxfordshire...
Author: admin
Leaking Passwords through the Spellchecker
Leaking Passwords through the SpellcheckerSometimes browser spellcheckers leak passwords: When using major web browsers like Chrome and Edge, your form data is transmitted to Google and...
Microsoft SQL servers hacked in TargetCompany ransomware attacks
Microsoft SQL servers hacked in TargetCompany ransomware attacksSecurity analysts at ASEC have discovered a new wave of attacks targeting vulnerable Microsoft SQL servers, involving the deployment...
8 mistakes CIOs make and how to avoid them
8 mistakes CIOs make and how to avoid themFrom driving transformative change, to sharing insights into the political nature of the role, IT leaders and advisors...
Windows 11 now warns when typing your password in Notepad, websites
Windows 11 now warns when typing your password in Notepad, websitesWindows 11 22H2 was just released, and with it comes a new security feature called Enhanced...
Optus data security breach: what should I do to protect myself?
Optus data security breach: what should I do to protect myself?Experts say while ‘there’s no need to panic’, there are steps you can take to ensure...
Optus faces potential class action and pledges free credit monitoring to data-breach customers
Optus faces potential class action and pledges free credit monitoring to data-breach customersHome affairs minister Clare O’Neil says company to blame and flags new laws with...
Threat Research: New Method of Volume Shadow Backup Deletion Seen in Recent Ransomware
Threat Research: New Method of Volume Shadow Backup Deletion Seen in Recent RansomwareVMware Threat Analysis Unit (TAU) researchers have recently observed a new technique for the...
The Evolution of the Chromeloader Malware
The Evolution of the Chromeloader MalwareExecutive Summary ChromeLoader proves to be an extremely prevalent and persistent malware. It initially drops as an .iso and can be...
Threat Report: Illuminating Volume Shadow Deletion
Threat Report: Illuminating Volume Shadow DeletionExecutive Summary Ransomware is one of the greatest threats to all industries. Threat actors have the ability to severely hinder, or...
Patch now! Microsoft issues critical security updates as PCs attacked through zero-day flaw
Patch now! Microsoft issues critical security updates as PCs attacked through zero-day flawWindows users are once again being told to update their systems with the latest...
Smashing Security podcast #289: Printer peeves, health data hangups, and Twitter tussles – with Rory Cellan-Jones
Smashing Security podcast #289: Printer peeves, health data hangups, and Twitter tussles – with Rory Cellan-JonesHow could your inkjet printer finally help you make some money,...
FBI warns of criminals attacking healthcare payment processors
FBI warns of criminals attacking healthcare payment processorsMillions of dollars have been stolen from healthcare companies after fraudsters gained access to customer accounts and redirected payments....
Uber’s hacker *irritated* his way into its network, stole internal documents
Uber’s hacker *irritated* his way into its network, stole internal documentsUber has suffered a security breach which allowed a hacker to break into its network, and...
5G Technology – Ensuring Cybersecurity for Businesses
5G Technology – Ensuring Cybersecurity for BusinessesBy Mohit Shrivastava, Chief Analyst ICT, Future Market Insights 5G network, the fifth generation of the cellular technology […] The...
Are Cyber Scams More Common and How Do We Avoid Them?
Are Cyber Scams More Common and How Do We Avoid Them?By Harry Turner, Freelance Writer Cyber scams seem to become more and more common and are...
Starbucks Singapore warns customers after hacker steals data, offers it for sale on underground forum
Starbucks Singapore warns customers after hacker steals data, offers it for sale on underground forum200,000 customers of Starbucks in Singapore have had their personal details put...
Hackers Exploited Zero-Day RCE Vulnerability in Sophos Firewall — Patch Released
Hackers Exploited Zero-Day RCE Vulnerability in Sophos Firewall — Patch ReleasedSecurity software company Sophos has released a patch update for its firewall product after it was...
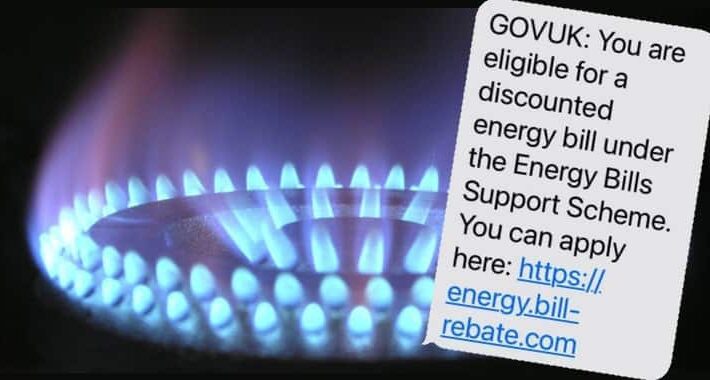
Energy bill rebate scams spread via SMS and email
Energy bill rebate scams spread via SMS and emailThe UK’s National Cyber Security Centre (NCSC) has warned that fraudsters are sending out emails and SMS texts...
London Police Arrested 17-Year-Old Hacker Suspected of Uber and GTA 6 Breaches
London Police Arrested 17-Year-Old Hacker Suspected of Uber and GTA 6 BreachesThe City of London Police on Friday revealed that it has arrested a 17-year-old teenager...
Reflections in your glasses can leak information while you’re on a Zoom call
Reflections in your glasses can leak information while you’re on a Zoom callBespectacled video conferencing participants have more to worry about than if their hair is...
What Is Data Exfiltration? MITRE ATT&CK® Exfiltration Tactic | TA0010
What Is Data Exfiltration? MITRE ATT&CK® Exfiltration Tactic | TA0010 The process of stealing data from a corporate system is also known as exfiltration. MITRE ATT&CK®...
OpIran: Anonymous declares war on Teheran amid Mahsa Amini’s death
OpIran: Anonymous declares war on Teheran amid Mahsa Amini’s deathOpIran: Anonymous launched Operation Iran against Teheran due to the ongoing crackdown on dissent after Mahsa Amini’s...
Smashing Security podcast #290: Uber, Rockstar, and crystal balls
Smashing Security podcast #290: Uber, Rockstar, and crystal ballsResearchers reveal how your eyeglasses could be leaking secrets when you’re on video conferencing calls, we take a...
Air Force Upgrades Digital Modernization Strategy to “As a Service” Model
Air Force Upgrades Digital Modernization Strategy to "As a Service" ModelThe transition will be carried out through three procurements to be awarded before the end of...
Weekly Update 313
Weekly Update 313I came so close to skipping this week's video. I'm surrounded by family, friends and my amazing wife to be in only a couple...
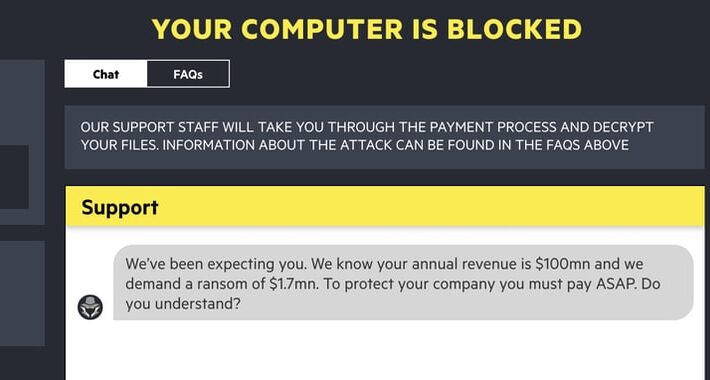
How to have fun negotiating with a ransomware gang
How to have fun negotiating with a ransomware gangThe Financial Times has created an imaginative ransomware negotiation simulator which lets you imagine you’re in the hot...
Attackers impersonate CircleCI platform to compromise GitHub accounts
Attackers impersonate CircleCI platform to compromise GitHub accountsThreat actors target GitHub users to steal credentials and two-factor authentication (2FA) codes by impersonating the CircleCI DevOps platform....
Avoiding the Risks of Ransomware Strikes in Life Sciences
Avoiding the Risks of Ransomware Strikes in Life SciencesBy Travis Tidwell, Business Development Lead, Rockwell Automation While Life Sciences companies have become even more important to...
Come to the National Information Security Conference in October, and see Smashing Security LIVE!
Come to the National Information Security Conference in October, and see Smashing Security LIVE!Between 5-7 October, I will be chairing the UK's National Information Security Conference...