What is data migration?In business and technology, migrating data means moving it from one system or platform to another. Learn the processes and challenges of data...
Author: admin
K30671731: Apache Shiro vulnerability CVE-2022-40664
K30671731: Apache Shiro vulnerability CVE-2022-40664Apache Shiro vulnerability CVE-2022-40664 Security Advisory Security Advisory Description Apache Shiro before 1.10.0, Authentication Bypass Vulnerability in Shiro when forwarding or including...
Will Twitter Sink or Swim Under Elon Musk’s Direction?
Will Twitter Sink or Swim Under Elon Musk's Direction?Billionaire Faces Cybersecurity, Disinformation, Legal and Other ChallengesElon Musk lugged a sink into Twitter headquarters to announce his...
Threat Analysis: Active C2 Discovery Using Protocol Emulation Part3 (ShadowPad)
Threat Analysis: Active C2 Discovery Using Protocol Emulation Part3 (ShadowPad)ShadowPad is a modular malware platform privately shared with multiple PRC-linked threat actors since 2015. According to...
Medibank cyber-attack: should the health insurer pay a ransom for its customers’ data?
Medibank cyber-attack: should the health insurer pay a ransom for its customers’ data?Speculation is rife about whether the insurer will pay a hacker who claims to...
Live Webinar | Hacking the Hacker: Assessing and Addressing Your Organization’s Cyber Defense Weaknesses
Live Webinar | Hacking the Hacker: Assessing and Addressing Your Organization’s Cyber Defense WeaknessesContenido de la entradaLeer másDataBreachToday.com RSS Syndication
Threat Analysis: Active C2 Discovery Using Protocol Emulation Part3 (ShadowPad)
Threat Analysis: Active C2 Discovery Using Protocol Emulation Part3 (ShadowPad)ShadowPad is a modular malware platform privately shared with multiple PRC-linked threat actors since 2015. According to...
Feds Urge Healthcare Entities to Train for Incident Response
Feds Urge Healthcare Entities to Train for Incident ResponsePlans Should Emphasize Rehearsing Various Hacking, Breach ScenariosHealthcare entities need to rehearse breach response playbooks to avoid paying...
K30671731: Apache Shiro vulnerability CVE-2022-40664
K30671731: Apache Shiro vulnerability CVE-2022-40664Apache Shiro vulnerability CVE-2022-40664 Security Advisory Security Advisory Description Apache Shiro before 1.10.0, Authentication Bypass Vulnerability in Shiro when forwarding or including...
K30671731: Apache Shiro vulnerability CVE-2022-40664
K30671731: Apache Shiro vulnerability CVE-2022-40664Apache Shiro vulnerability CVE-2022-40664 Security Advisory Security Advisory Description Apache Shiro before 1.10.0, Authentication Bypass Vulnerability in Shiro when forwarding or including...
Threat Analysis: Active C2 Discovery Using Protocol Emulation Part3 (ShadowPad)
Threat Analysis: Active C2 Discovery Using Protocol Emulation Part3 (ShadowPad)ShadowPad is a modular malware platform privately shared with multiple PRC-linked threat actors since 2015. According to...
CISA Releases Performance Goals for Critical Infrastructure
CISA Releases Performance Goals for Critical InfrastructureMeasures Are Not Mandatory and Not Comprehensive, Federal Officials StressThe Department of Homeland Security released a set of cybersecurity practices...
Forescout CEO Wael Mohamed to Exit as Firm Lays Off Workers
Forescout CEO Wael Mohamed to Exit as Firm Lays Off WorkersMohamed's Departure Means IoT Security Firm Will Get Its 4th CEO Since Fall 2020Forescout will get...
Medlab Pathology Breach Affects 223,000 Australians
Medlab Pathology Breach Affects 223,000 AustraliansMedical Records and Credit Card Details of Patients CompromisedOne of Australia's largest private testing laboratories announced a data breach affecting 223,000...
COVID-19 was an all-you-can-eat buffet for social engineers
COVID-19 was an all-you-can-eat buffet for social engineersContenido de la entradaLeer másProofpoint News Feed
CISOs, corporate boards in wide disagreement on cyber resilience
CISOs, corporate boards in wide disagreement on cyber resilienceContenido de la entradaLeer másProofpoint News Feed
Product Highlight | Vendor Application Security in K-12 Schools Using ManagedMethods
Product Highlight | Vendor Application Security in K-12 Schools Using ManagedMethodsManagedMethods Makes Managing Vendor Application Security in Google/Microsoft Fast & Easy The concept of “shadow IT”...
Proofpoint Introduces Advanced Email Protection Integration with Microsoft Defender for Endpoint
Proofpoint Introduces Advanced Email Protection Integration with Microsoft Defender for EndpointContenido de la entradaLeer másProofpoint News Feed
FAQ-SaaS Security Posture Management (SSPM)
FAQ-SaaS Security Posture Management (SSPM)SSPM are important for SaaS security. Learn what you need in place to get the move value for your security program. The...
How are CKYC, KYC and eKYC different? Definitive Guide to CKYC
How are CKYC, KYC and eKYC different? Definitive Guide to CKYCWith the rising fraud in the financial industry, it is critical to preserve adequate client records...
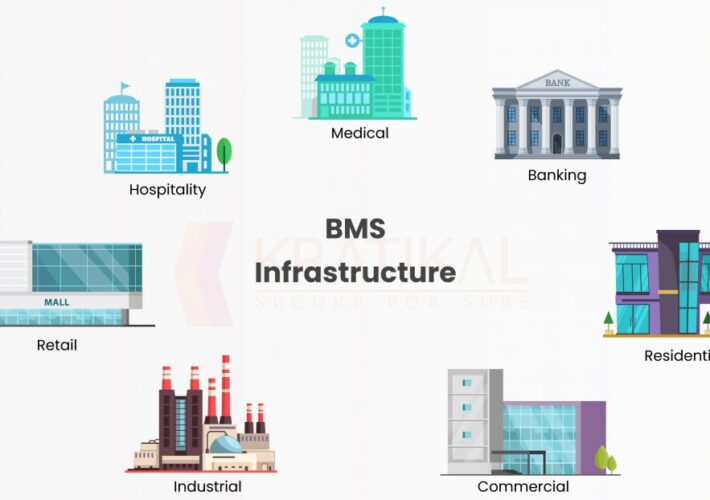
OT Security Assessment of BMS
OT Security Assessment of BMSPeople are not aware that modern buildings are changing and have changed to an industrial control system. They are now embedded with...
BlackByte ransomware picks up where Conti and Sodinokibi left off
BlackByte ransomware picks up where Conti and Sodinokibi left offBlackByte is using Exbyte, a new custom exfiltration tool, to steal data. Learn how to protect your...
Fighting cybersecurity risks for law enforcement: On-premises vs. cloud native systems
Fighting cybersecurity risks for law enforcement: On-premises vs. cloud native systemsLarry Zorio, chief information security officer at Mark43, offers helpful insight from the battlefront. The post...
Make Your Device Run Like New Again | Avast
Make Your Device Run Like New Again | Avast Are you secretly tech-challenged? Don’t be ashamed to say so –– you’re not alone. A British study...
How to navigate the current 5G and IoT threat landscape
How to navigate the current 5G and IoT threat landscape5G and IoT have made promising strides in the business and consumer technology spaces, but with new...
How to Solve Code Signing Certificate Expiration Issues?
How to Solve Code Signing Certificate Expiration Issues?Expiring Code Signing Certificate: Know its Impact on Your Software and How to Renew and Prevent the Certificate from...
Proofpoint Expands Threat Protection Platform with New Deployment, Detection, and Behavioral Analytics Innovations
Proofpoint Expands Threat Protection Platform with New Deployment, Detection, and Behavioral Analytics InnovationsContenido de la entradaLeer másProofpoint News Feed
Iran’s Atomic Energy Agency Confirms Hack
Iran’s Atomic Energy Agency Confirms HackThe Iranian Atomic Energy Organization (AEOI) confirms that one of the email servers of its subsidiaries was hacked after the “Black...
Two POS Malware Used by Hackers to Steal Card Details
Two POS Malware Used by Hackers to Steal Card DetailsPOS malware is still a threat exploited by cybercriminals, even if the card payment industry has been...
Phishing: The tip of the iceberg
Phishing: The tip of the iceberg Day after day, we see news about new cyberattacks: Data breaches, yet another ransomware attack, and so on. From big...