S3 Ep105: WONTFIX! The MS Office cryptofail that “isn’t a security flaw” [Audio + Text]The coolest video game ever! And lots of solid cybersecurity advice -...
Author: admin
GitHub Repojacking Bug Could’ve Allowed Attackers to Takeover Other Users’ Repositories
GitHub Repojacking Bug Could've Allowed Attackers to Takeover Other Users' RepositoriesCloud-based repository hosting service GitHub has addressed a high-severity security flaw that could have been exploited...
Apple megaupdate: Ventura out, iOS and iPad kernel zero-day – act now!
Apple megaupdate: Ventura out, iOS and iPad kernel zero-day – act now!Ventura hits the market with 112 patches, Catalina's gone missing, and iPhones and iPads get...
Serious Security: How randomly (or not) can you shuffle cards?
Serious Security: How randomly (or not) can you shuffle cards?What if you could guess the next card correctly twice as often as you should?Leer másNaked SecurityWhat...
Micro-Segmentation: Where Does It Fit into Zero Trust?
Micro-Segmentation: Where Does It Fit into Zero Trust?Micro-Segmentation Is Not Zero Trust Alone Or Vice Versa By Brian Haugli – CEO, SideChannel Micro-segmentation is not […]...
When cops hack back: Dutch police fleece DEADBOLT criminals (legally!)
When cops hack back: Dutch police fleece DEADBOLT criminals (legally!)Crooks: Show us the money! Cops: How about you show us the decryption keys first?Leer másNaked SecurityCrooks:...
S3 Ep106: Facial recognition without consent – should it be banned?
S3 Ep106: Facial recognition without consent – should it be banned?Latest episode - listen (or read) now. Teachable moments for X-Ops professionals!Leer másNaked SecurityLatest episode -...
Samsung Galaxy Store Bug Could’ve Let Hackers Secretly Install Apps on Targeted Devices
Samsung Galaxy Store Bug Could've Let Hackers Secretly Install Apps on Targeted DevicesA now-patched security flaw has been disclosed in the Galaxy Store app for Samsung...
Online ticketing company “See” pwned for 2.5 years by attackers
Online ticketing company “See” pwned for 2.5 years by attackersDon't be a cybersecurity slowcoach - you need to spot possible attacks as soon as you can.Leer...
Clearview AI image-scraping face recognition service hit with €20m fine in France
Clearview AI image-scraping face recognition service hit with €20m fine in France"We told you to stop but you ignored us," said the French regulator, "so now...
Updates to Apple’s zero-day update story – iPhone and iPad users read this!
Updates to Apple’s zero-day update story – iPhone and iPad users read this!Turns out that Tuesday's zero-day for iOS 16 is Friday's zero-day for iOS 15...Leer...
Chrome issues urgent zero-day fix – update now!
Chrome issues urgent zero-day fix – update now!We've said it before/And we'll say it again/It's not *if* you should patch/It's a matter of *when*. (Hint: now!)Leer...
Phishing attacks increase by over 31% in third quarter: Report
Phishing attacks increase by over 31% in third quarter: ReportEmail security and threat detection company Vade has found that phishing emails in the third quarter this...
Data capture by border agencies can and will happen – are your on-the-road employees prepared?
Data capture by border agencies can and will happen – are your on-the-road employees prepared?Does your company have a travel policy that instructs and supports employees...
Former British Prime Minister Liz Truss ‘s phone was allegedly hacked by Russian spies
Former British Prime Minister Liz Truss ‘s phone was allegedly hacked by Russian spiesAccording to the Daily Mail, Former British Prime Minister Liz Truss ‘s personal...
How Card Skimming Disproportionally Affects Those Most In Need
How Card Skimming Disproportionally Affects Those Most In NeedWhen people banking in the United States lose money because their payment card got skimmed at an ATM,...
Sigma2SaveLives: Equip Yourself with Curated Sigma Rules While Donating to Save Lives in Ukraine
Sigma2SaveLives: Equip Yourself with Curated Sigma Rules While Donating to Save Lives in Ukraine On April 4, 2022, SOC Prime launched Sigma2SaveLives charity subscription with 100%...
Microsoft releases out-of-band updates to fix OneDrive crashes
Microsoft releases out-of-band updates to fix OneDrive crashesMicrosoft has released out-of-band updates today to address a known issue causing OneDrive and OneDrive for Business to crash...
Single chip transfers the entire internet’s traffic in a second
Single chip transfers the entire internet’s traffic in a secondEXECUTIVE SUMMARY: A single chip has managed a transfer of over a petabit-per-second, according to new research...
How To Protect Against The 83 million Cyber Attacks Detected In 2021
How To Protect Against The 83 million Cyber Attacks Detected In 2021The 4 Basic Cybersecurity Practices Experts Say Prevent Most Attacks By CyberLock Defense, Lockton Affinity...
Threat Actors Target AWS EC2 Workloads to Steal Credentials
Threat Actors Target AWS EC2 Workloads to Steal CredentialsWe found malicious samples attempting to steal Amazon Elastic Compute Cloud (EC2) Workloads' access keys and tokens via...
Raising the Alarm on DDoS Attacks
Raising the Alarm on DDoS AttacksBy Ivan Shefrin, Executive Director for Managed Security Services at Comcast Business Many organizations underappreciate the risk of […] The post...
Twilio reveals hackers compromised its systems a month earlier than previously thought
Twilio reveals hackers compromised its systems a month earlier than previously thoughtCloud communications firm Twilio reveals that it fell victim to a voice phishing attack in...
Apple Only Commits to Patching Latest OS Version
Apple Only Commits to Patching Latest OS VersionPeople have suspected this for a while, but Apple has made it official. It only commits to fully patching...
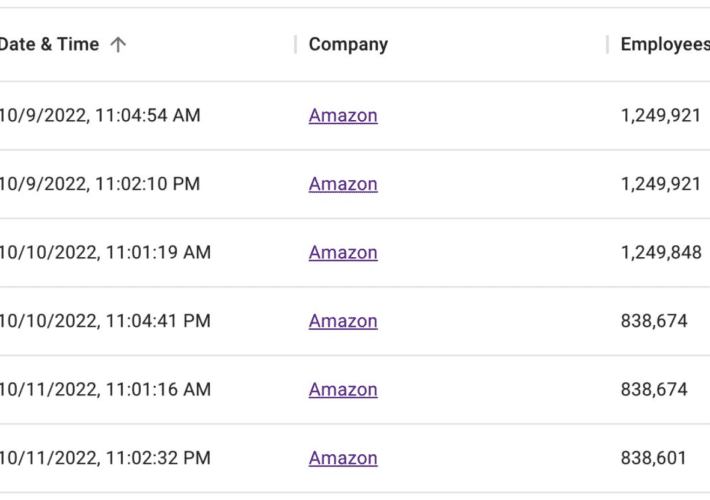
Battle with Bots Prompts Mass Purge of Amazon, Apple Employee Accounts on LinkedIn
Battle with Bots Prompts Mass Purge of Amazon, Apple Employee Accounts on LinkedInOn October 10, 2022, there were 576,562 LinkedIn accounts that listed their current employer...
Announcing GUAC, a great pairing with SLSA (and SBOM)!
Announcing GUAC, a great pairing with SLSA (and SBOM)!Posted by Brandon Lum, Mihai Maruseac, Isaac Hepworth, Google Open Source Security Team Supply chain security is at...
Cranefly uses new communication technique in attack campaigns
Cranefly uses new communication technique in attack campaignsA threat actor dubbed "Cranefly" uses a new technique for its communications on infected targets. The post Cranefly uses...
Why Employers Should Embrace Competency-Based Learning in Cybersecurity
Why Employers Should Embrace Competency-Based Learning in CybersecurityThere is a growing movement toward increasing the use of competency and skills-based education and hiring practices in both...
GUEST ESSAY: A roadmap to achieve a better balance of network security and performance
GUEST ESSAY: A roadmap to achieve a better balance of network security and performanceHere’s a frustrating reality about securing an enterprise network: the more closely you...
Online age-verification system could create ‘honeypot’ of personal data and pornography-viewing habits, privacy groups warn
Online age-verification system could create ‘honeypot’ of personal data and pornography-viewing habits, privacy groups warnAs the government develops online safety guidelines, digital rights groups says any...